What is WifiPineapple
The Wifipineapple is a wifi auditing platform by Hack5 that offers extensive features for defensive and offensive wifi security applications through a slick interface that you can access from any web browesers. You can easily manage your wifipineapple and use it connect wireless engagements to gather passive on a target network or even execute man-in-the-middle style attack.
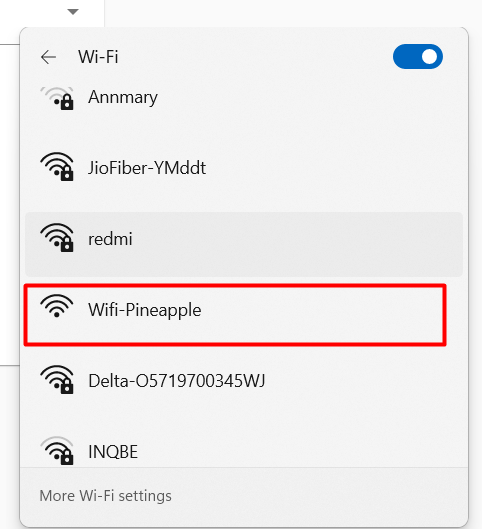
Then we can started you can log into your wifipineapple over at 172.16.42.1 on port 1471, before you connect the ip first we have to connect our wifi pineapple to our computer, my pipeapple plugged into usb type-C which is connected to a usb port on my computer.
Then we access the ip we get a login page and default username and password is,
root:change_on_install
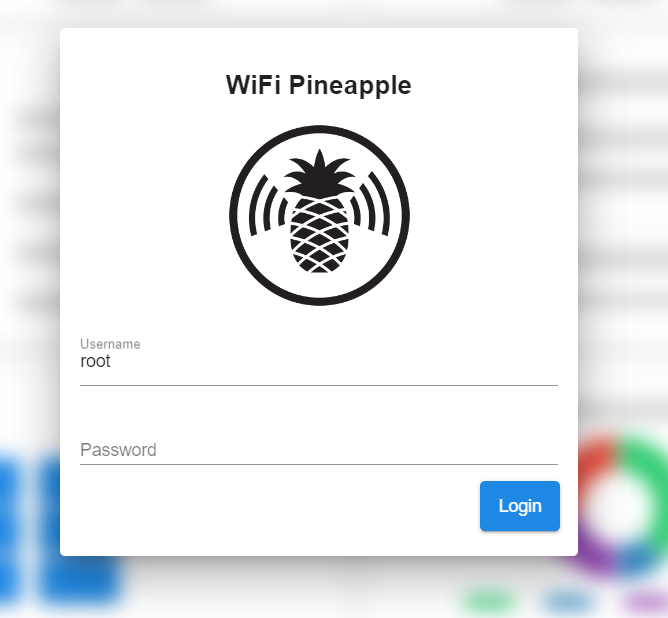
or also you can connect over a wifi access point or also over a tethered user-interface like i have.
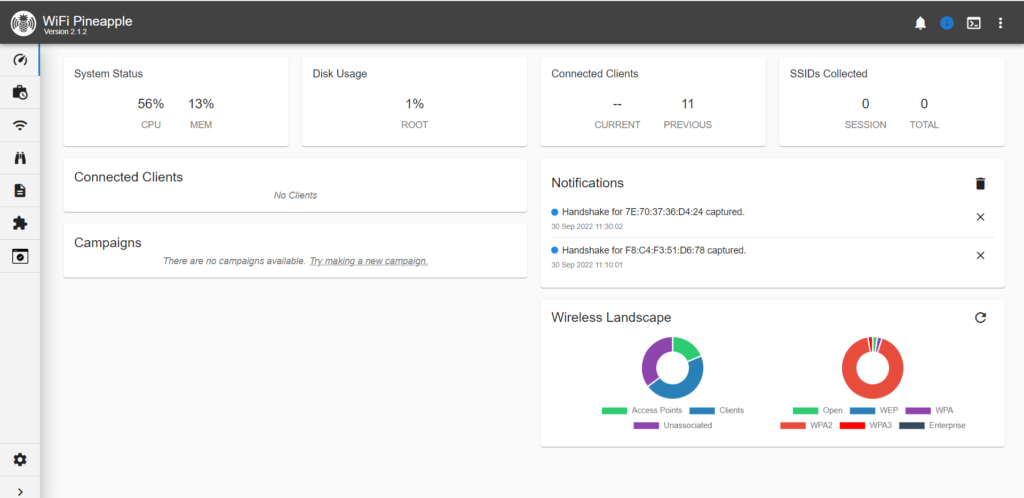
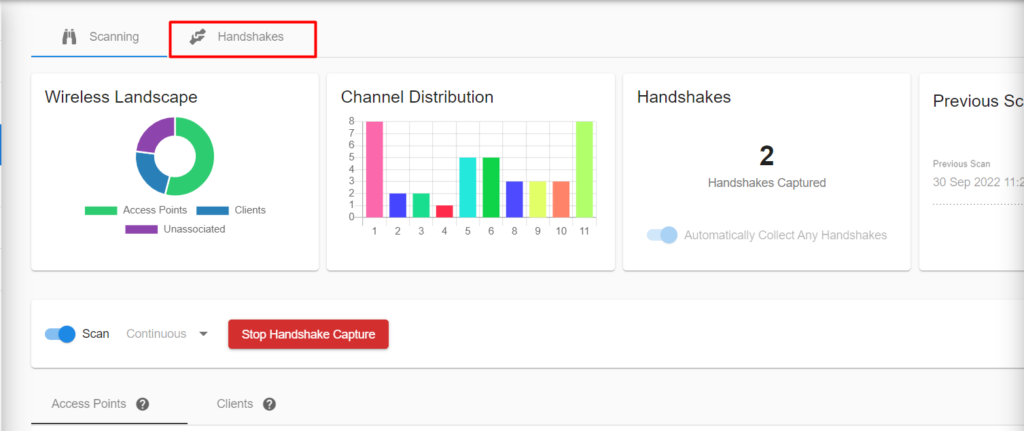
thus we can see many types of attacks in their and we choose the Reconnaissance
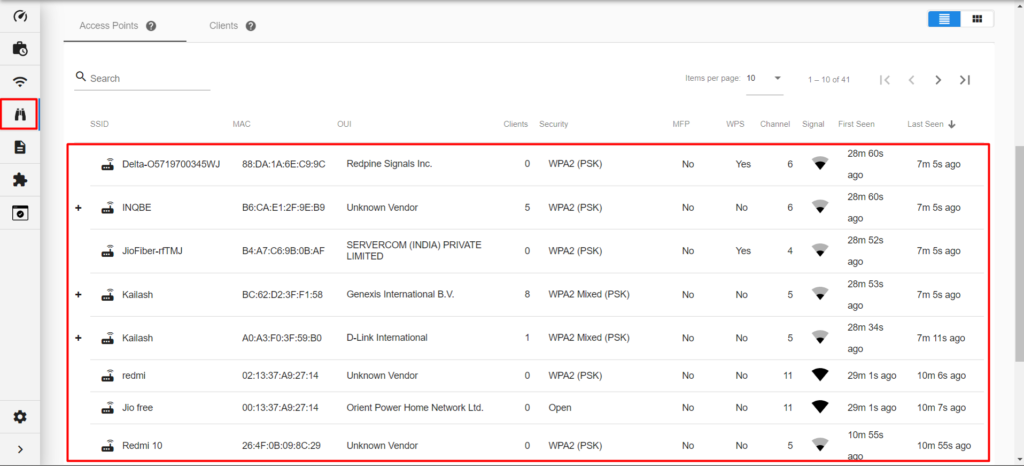
we can see many access points are listed there and choose one access point.(i choose my access point Annmary)
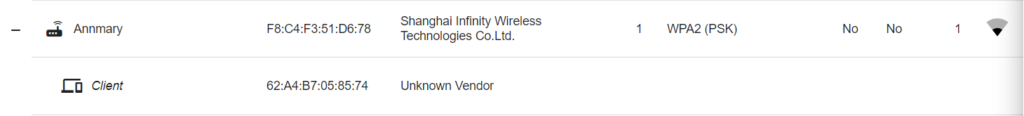
lets start the capture the handshake of access point.
Handshake is a type of an attack, the attacker forces all clients to connect from the router, and when they go to reconnect (default behavior for client devices), the attacker captures the handshake. This can then be cracked offline to reveal the Wi-Fi password.
Click on access point and get a “Capture WPA Handshakes” choose that option.
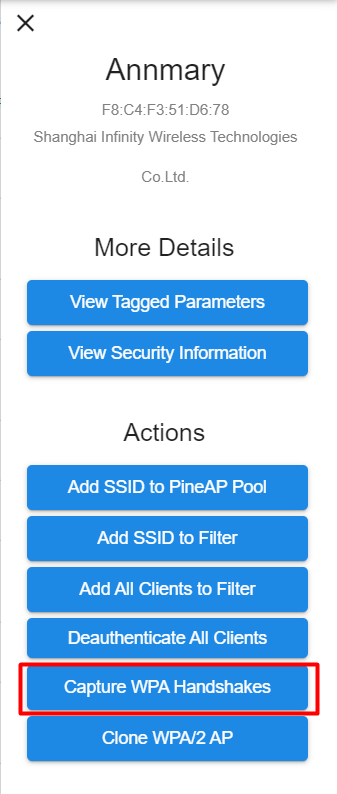
At same time starts capture the handshake.
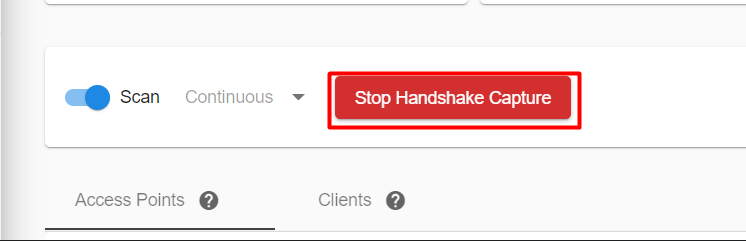
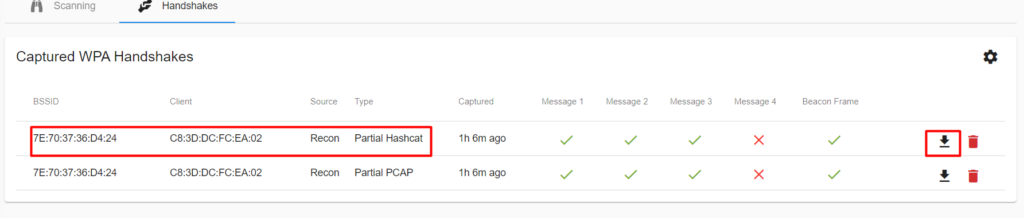
if we can see a client is connected on my access point , later we start the capture the handshake, we forcefully de-authenticated the client from the access point. The normal behaviour is if any wifi is disconnect and the client always search for another or same network to connect. Thus the time client will reconnect and we get a handshake of that router.
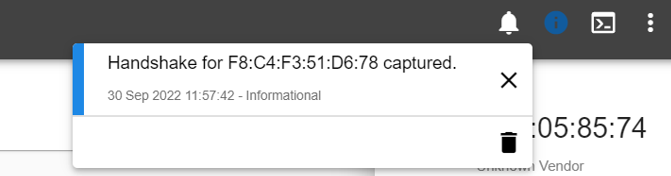
Yes, the handshake is captured : )
and open the handshake and we can download the file.
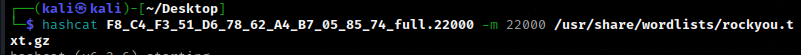
then its over we get their hash file and we crack using hashcat tool, then open terminal and enter the command
hashcat <filename.22000> -m 22000 <wordlist_path>
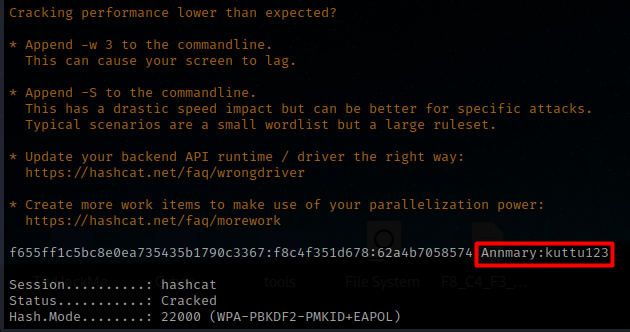
; ) we get password ….HaPpy HaCkiNg








Leave a Reply