what is a pwnagotchi ?
A pwnagotchi is a Tamagotchi like digital toy,but it feeds on Wi-Fi handshakes.The pwnagotchi is made with the help of a raspberry pi zero. It sniff around for the Wi-Fi signals around it and deauthenticate the client from the access point and captures the handshakes while they try to reconnect. This handshakes will be saved as a .pcap file which can later be decrypted into plain text. Unlike manually feeding him with digital food he will feed on the handshakes captured. The more he eat the more happy he is.
HOW DOES IT WORK ?
A Pwnagotchi is an A2C-based AI(artificial inteligance), powered by a tool bettercap (made by Simone Margaritelli, known as evilsocket).It has 3 modes “manu” ,”auto” and “AI”, manual mode is used to retrieve the handshakes captured by the pwnagotchi. In auto mode the pwnagotchi does it’s job smoothly, it listens to it’s environment and looks for wifi singnals and sends deauthentication signal to the AP(access point) and the clients connected to the AP gets disconnected and the client device immediately tries to reconnect but the pwanogotchi listens to the handshake and captures it and save sit in a “.pcap” file in the root directory,This process is called feeding the pwnagotchi .In AI mode the pwanogotchi learns about the wifi signal and the captured handshakes and cracks the wifi handshakes in a better way day by day.

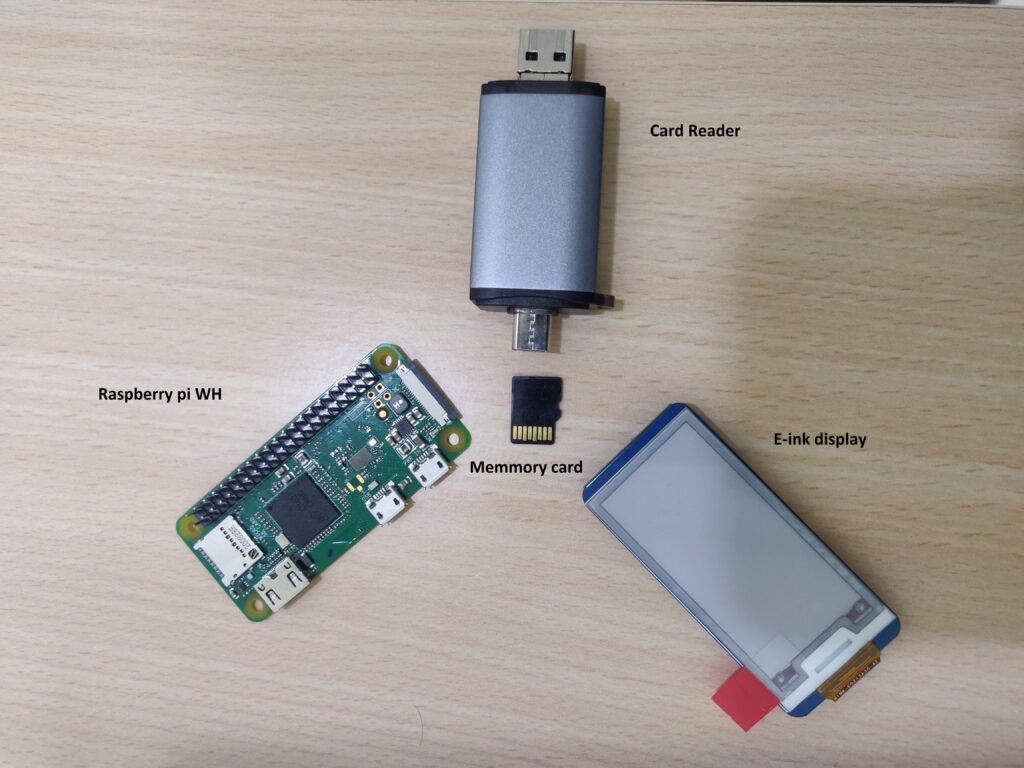
COMPONENTS REQUIRED
Components required to make a pwanogotchi are a Raspberry pi zero WH (W stands for wifi enabled, H stands for pre soldered hedder pins),an E-ink display (version 2), a memory card (minimum 8 GB),a good card reader and 2 data cables.
How to setup this little guy?
- Connect the Raspberry Pi Zero and e-ink display.
- Flash the linux image to the sd card with the help of balenaEtcher.
- Set up the config file in the boot folder,save it in the boot partition as config.toml
- connect the power port to a power bank or your computer and wait for sometime for his first boot. (It will take some time).
- Take him out for a day, Collect handshakes, download the .pcap file.
What happens behind the screen?
WPA is not secure and WPA2 is also not secure if you don’t have a good strong password but it’s everywhere so pwnagotchi feeds on these wifi handshakes.
In order to understand how this hardware is able to capture handshake it will be helpful to know how handshakes are used in WPA/WPA2 wireless protocol. Let’s assume that our laptop or mobile phone is trying to connect to a WI-FI network and is able to securely transmit to and receive data from that access point, because of a process called the 4-Way Handshake. A 4-Way Handshake needs to happen in order for the WPA encryption keys to be generated. This process consists of the exchange of four packets (hence the “4” in “4-Way”) between the client device and the Access point; these are used to derive session keys from the access point’s Wi-Fi password. Once the packets have been successfully exchanged and the keys are generated, the client device is authenticated and can start sending and receiving data packets (now secured by encryption) to and from wireless AP.
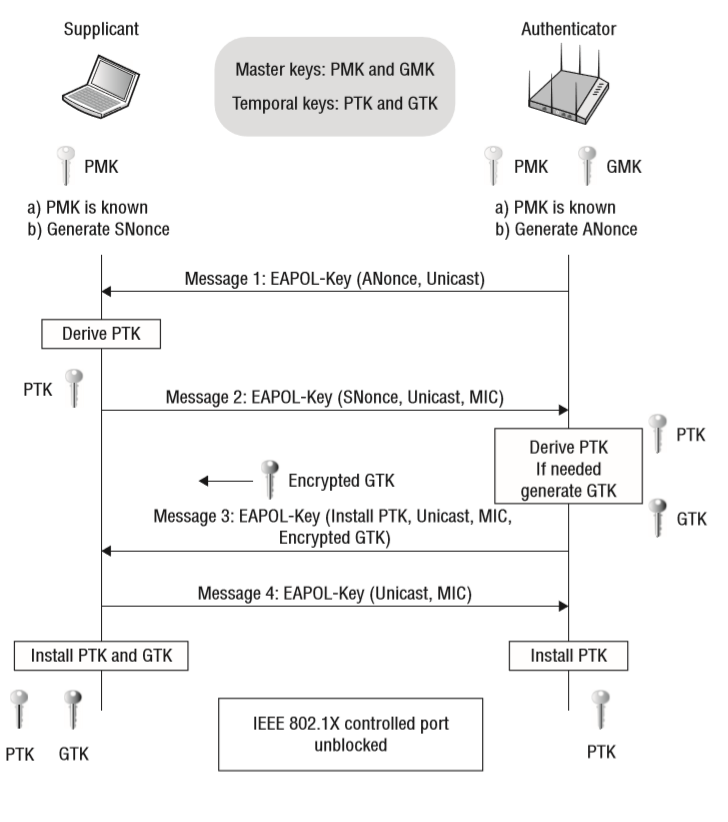
So…what’s the catch? Well, these four packets can easily be “sniffed” by an attacker monitoring nearby environment (in our case, with a Pwnagotchi ). And once hand shake is captured, that attacker can use dictionary or bruteforce attacks to crack the handshakes and recover the original WiFi key. As a matter of fact, successful recovery of the Wi-Fi key doesn’t necessarily even need all four packets! A half-handshake (containing only two of the four packets) can be cracked, too — and in some other (most) cases, just a single packet is enough, even without any clients.
In order to eat/collect as many of these crackable handshake packets as possible, Pwnagotchi uses two strategies:
1. Deauthenticating the client stations it detects. A deauthenticated device must reauthenticate to its access point by re-doing the 4-Way Handshake process with the AP, thereby giving Pwnagotchi another chance to sniff the handshake packets and collect more crackable material.
2. Sending association frames directly to the access points themselves to try to force them to leak the PMKID of the device.
3. All the handshakes captured by our pwnagotchiiii are saved to a .pcap file in the file system of the pwnagotchi it can be copied from there and the handshakes captured can be cracked with proper hardware and software.
What to do after the handshakes are captured ?
To demonstrate this process let’s set up a personal testing lab setup. I have setup a personal Wi-Fi access point “Hidden network” and I am going to power up the pwnagotchi. After some time the pwnagotchi might have captured the wifi handshakes. To see these let’s connect the device to our computer using the data port and SSH into it.
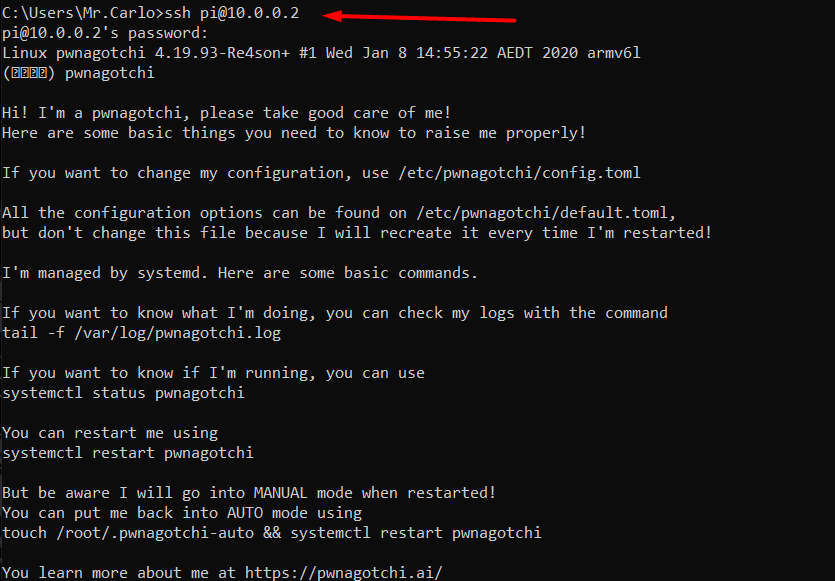
Then go to the handshakes directory and copy the files to the pi directory so that we can copy the .pcap files to our machine and we can test a bruteforce attack on it.
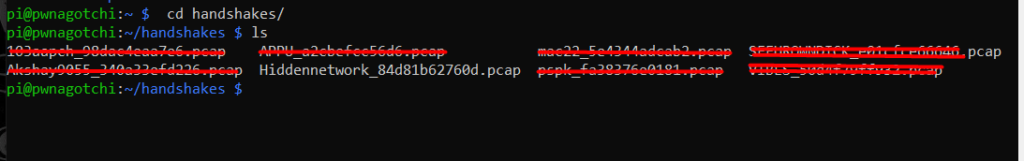
Eventhough our intention was to test only the setup lab wifi, the weakly protected wifi signals in the environment was also captured by the pwnagotchi.Copy only the file we need ie, “Hidden network” to the pi directory.
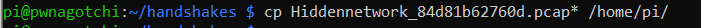
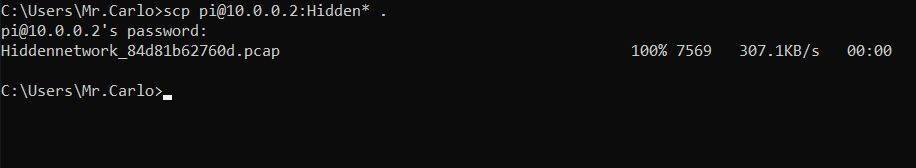
Now we have the .pcap file,let’s take it to the kali linux operating system, there we have sophisticated tools for this purpose.
The handshake contains many information about your Wi-Fi network which can be used by hackers. To do further attacks on your Wi-Fi network. It can be brute forced easily. Let’s see that on our test file itself.
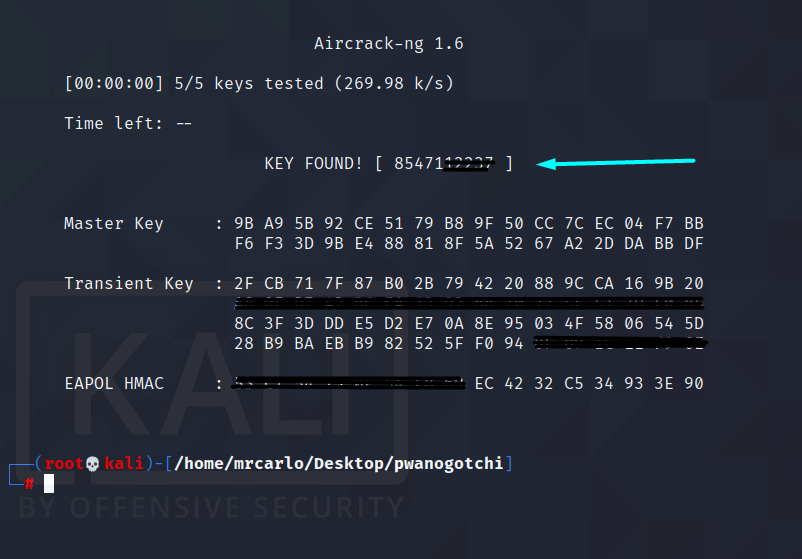
Here we used a custom wordlist to crack it for the demonstration purpose. All it took was less than a second to brute force the .pcap file and we got the password.
Or you can simply upload your .pcap file to this website and they will do the job for you.
Conclusion
Perfect security is a myth,but it is our responsibility and right to be safe in this digital century.
- Change the default name of your home Wi-Fi.
- Make your wireless network password unique and strong.
- Enable network encryption.
- Turn off network name broadcasting.
- Keep your router’s software up to date.
- Make sure you have a good firewall.
Use VPNs to access public network
Read more
NB: This blog is for educational purpose only,use it with required permission, and use it responsibly. I am not responsible for any illegal use of this information.







Leave a Reply