Table of contents
- Introduction
- What is TCP protocol?
- Advantages of TCP protocol
- Disadvantages of TCP protocol
- Attacks on the TCP
- What is UDP protocol?
- Advantages of UDP protocol
- Disadvantages of UDP protocol
- Attacks on the UDP
- TCP vs UDP
1. Introduction
A communication protocol is a set of rules and regulations which are performed to transfer data to the source and destination through the physical or wireless communication channel.
2. What is TCP protocol?
TCP stands for Transmission Control Protocol. The TCP protocol is a communication standard that helps to transfer data through the network to any of the computing devices. TCP is one of the most commonly used protocols within a digital network for end-to-end data delivery.
TCP organizes data so it can transmit data between the server and the client. It guarantees the integrity of data being transferred through a network. Before it transmits data, TCP establishes a connection between a source and its destination, which it ensures remains live until communication begins. It then breaks large amounts of data into smaller packets, while ensuring data integrity is in place throughout the process.
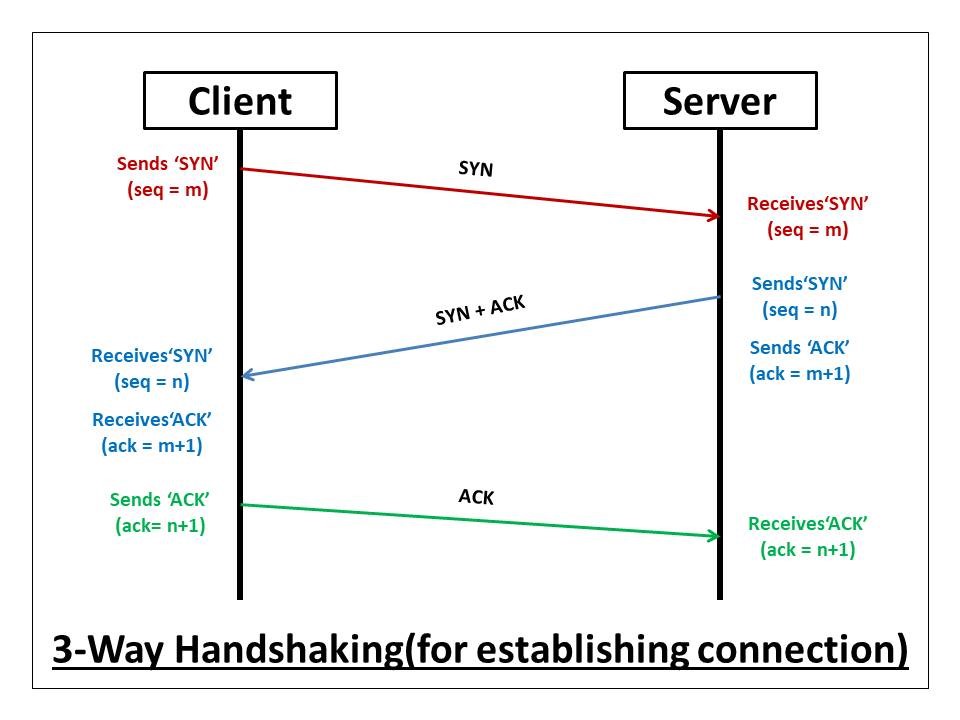
TCP is used a three way handshake function for establishing a connection between sender and receiver.
High-level protocols that need to transmit data all use TCP Protocol. Examples include peer-to-peer sharing methods like File Transfer Protocol (FTP), Secure Shell (SSH), and Telnet. It is also used to send and receive email through Internet Message Access Protocol (IMAP), Post Office Protocol (POP), and Simple Mail Transfer Protocol (SMTP), and for web access through the Hypertext Transfer Protocol (HTTP).
3. Advantages of TCP protocol
- TCP is an industry-standard model that can be effectively deployed in practical networking problems.
- TCP is interoperable, e.g., it allows cross-platform communications among heterogeneous networks.
- TCP is an open protocol suite. It is not owned by any particular institute and so can be used by any individual or organization.
- TCP is a scalable, client-server architecture. This allows networks to be added without disrupting the current services.
- TCP assigns an IP address to each computer on the network, thus making each device to be identifiable over the network. It assigns each site a domain name. It provides name and address resolution services.
4. Disadvantages of TCP protocol
- TCP is not generic in nature. So, it fails to represent any protocol stack other than the TCP/IP suite. For example, it cannot describe the Bluetooth connection.
- TCP does not clearly separate the concepts of services, interfaces, and protocols. So, it is not suitable to describe new technologies in new networks.
- It does not distinguish between the data link and the physical layers, which have very different functionalities. The data link layer should concern with the transmission of frames. On the other hand, the physical layer should lay down the physical characteristics of the transmission. A proper model should segregate the two layers.
- It was originally designed and implemented for wide area networks. It is not optimized for small networks like LAN (local area network) and PAN (personal area network).
- Among its suite of protocols, TCP and IP were carefully designed and well implemented. Some of the other protocols were developed ad hoc and so proved to be unsuitable in long run. However, due to the popularity of the model, these protocols are being used even 30–40 years after their introduction.
5. Attacks on the TCP
- SYN Flooding Attack: – A SYN flood is a form of denial-of-service attack in which an attacker rapidly initiates a connection to a server without finalizing the connection. The server has to spend resources waiting for half-opened connections, which can consume enough resources to make the system unresponsive to legitimate traffic.
- TCP RST Attacks on telnet and ssh Connections: – TCP packets can be transmitted with the RST flag set indicating that the connection must be terminated. This is not the same as the usual connection teardown that would be implied with a TCP FIN packet. Because the RST packet can preemptively close a connection, it has obvious use to an attacker.
- TCP RST Attacks on Video Streaming Applications: – The design of this attack was the same used the TCP RST attack against telnet in the previous section. TCP packets can be transmitted with the RST flag set indicating that the connection must be terminated. This is not the same as the usual connection teardown that would be implied with a TCP FIN packet. Because the RST packet can preemptively close a connection, it has obvious use to an attacker.
- ICMP Blind Connection-Reset: – ICMP connection-reset attacks once again take advantage of assumptive behavior. This attack sends a false signal that there has been a ‘hard error’ defined as a type 3 with a code 2, 3, or 4. These messages should immediately abort the connection.
- Source-Quench Attacks: – As with the ICMP connection-reset attack, source-quench attacks use an error type and code to cause action against a target. The ICMP message type 4 code 0 is a source-quench which is a signal to reduce the transmission rate. This can throttle the target, which would be a more subtle attack than completely severing or refusing a connection.
- TCP Session Hijacking: – Session hijacking is a way of passing some levels of security. Usually, when a connection between two hosts is established, there is some form of initial authentication, such as used in telnet. Session hijacking hopes to ‘piggyback’ in a way on that connection through various means.
6. What is UDP Protocol?
User Datagram Protocol (UDP), which is used to establish low-latency connections between applications and decrease transmissions time. TCP can be an expensive network tool as it includes absent or corrupted packets and protects data delivery with controls like acknowledgments, connection startup, and flow control.
UDP doesn’t make any kind of connection between sender and receiver through the communication channel. Just share the data packets one after one.
UDP does not provide error connection or packet sequencing nor does it signal a destination before it delivers data, which makes it less reliable but less expensive. As such, it is a good option for time-sensitive situations, such as Domain Name System (DNS) lookup, Voice over Internet Protocol (VoIP), and streaming media.
7. Advantages of UDP Protocol
- UDP uses a small packet size with a small header (8 bytes). This fewer bytes in the overhead makes UDP protocol need less time in processing the packet and need less memory.
- UDP does not require a connection to be established and maintained.
- The absence of an acknowledgment field in UDP makes it faster as it need not have to wait on ACK or need not have to hold data in memory until they are ACKed.
- UDP uses a checksum with all the packets for error detection.
- UDP can be used in events where a single packet of data needs to be exchanged between the hosts.
8. Disadvantages of UDP Protocol
- UDP is a connectionless and unreliable transport protocol. There is no windowing and no function to ensure data is received in the same order as it was transmitted.
- UDP does not use any error control. Hence if UDP detects an error in the received packet, it silently drops it.
- There is no congestion control. Couldn’t use any kind of method used for monitoring the process of regulating the total amount of data entering the network to keep traffic levels at an acceptable value.
- Only the application layer deals with error recovery. Hence applications can simply turn to the user to send the message again.
- Routers can be careless with UDP. They do not retransmit a UDP datagram after a collision and will often discard UDP packets before TCP packets.
9. Attacks on the UDP
- UDP flood attack: – A UDP flood is a form of volumetric Denial-of-Service (DoS) attack where the attacker targets and overwhelms random ports on the host with IP packets containing User Datagram Protocol (UDP) packets. In this type of attack, the host looks for applications associated with these datagrams. However, a UDP flood attack can be initiated by sending a large number of UDP packets to random ports on a remote host.
- UDP Reflection Attacks: – A reflection attack involves an attacker spoofing a target’s IP address and sending a request for information, primarily using the User Datagram Protocol (UDP) or in some cases, the Transmission Control Protocol (TCP). The server then responds to the request, sending an answer to the target’s IP address.
- UDP-Based Amplification Attacks: –Amplification attacks generate a high volume of packets that are used to overwhelm the target website without alerting the intermediary. This occurs when a vulnerable service responds with a large reply when the attacker sends his request, often called the “trigger packet”.
10. TCP vs UDP
| TCP | UDP |
| TCP is a connection-oriented protocol. | UDP is a connectionless protocol. |
| TCP reads data as streams of bytes, and the message is transmitted to segment boundaries. | UDP messages contain packets that were sent one by one. It also checks for integrity at the arrival time. |
| TCP messages make their way across the internet from one computer to another. | UDP is not connection-based, so one program can send lots of packets to another. |
| TCP rearranges data packets in a specific order. | UDP protocol has no fixed order because all packets are independent of each other. |
| The speed for TCP is slower. | UDP is faster as error recovery is not attempted. |
| The header size is 20 bytes. | The header size is 8 bytes. |
| TCP is heavy-weight. TCP needs three packets to set up a socket connection before any user data can be sent. | UDP is lightweight. There are no tracking connections, ordering of messages, etc. |
| TCP does error checking and also makes error recovery. | UDP performs error checking, but it discards erroneous packets. |
| Acknowledgment segments | No Acknowledgment segments. |
| Using handshake protocols like SYN, SYN-ACK, ACK | No handshake (so connectionless protocol) |
| TCP is reliable as it guarantees the delivery of data to the destination router. | The delivery of data to the destination can’t be guaranteed in UDP. |
| TCP offers extensive error checking mechanisms because it provides flow control and acknowledgment of data. | UDP has just a single error checking mechanism that is used for checksums. |










Nicely presented document.