When we talk about web applications nowadays they are one of the most indispensable parts of many of the business activities of any companies around the globe that we engage in every day. While the web applications have great advantages like availability all around the world through the internet and are easy to deploy without any effort and investment from the user’s side they only need a browser with an internet connection
While web applications have numerous benefits for users, it also has some serious weaknesses and vulnerabilities which lead to account takeovers and data breaches so to prevent attacks against web apps we have to know the most common web application attacks. We are discussing the five most common web application attacks
Cross-site scripting (XSS)
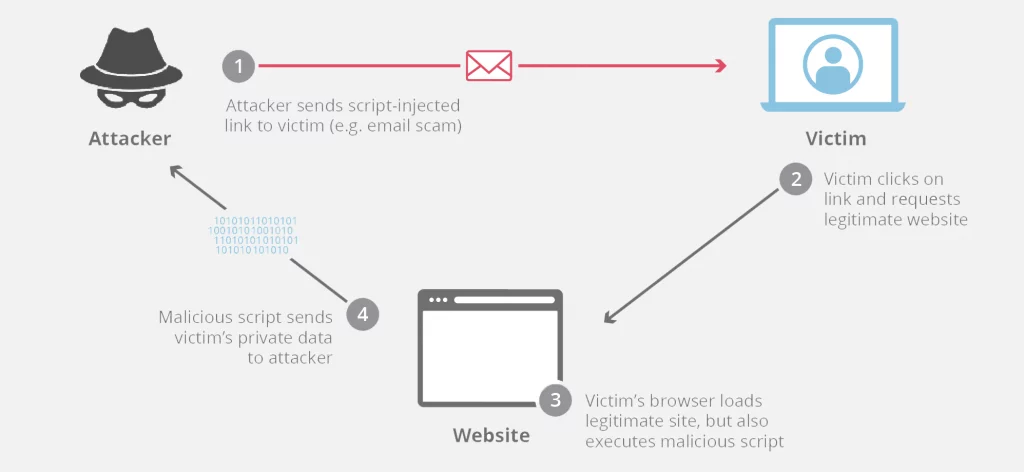
Cross-site scripting is one of the most common web app attacks out there. XSS involves the attacker inducing a web app to execute arbitrary or malicious JavaScript code the attacker uploaded. usually, because the site fails to properly sanitize the user inputs. . The attack does not target the server itself but instead the users. If another visitor loads the malicious or compromised web page, their browser may execute the malicious code, infecting the victim. most XSS attacks are done by less sophisticated so-called script kiddies, so this attack is more common. stealing cookies, Defacing, and Phishing attacks are the common use of XSS
There are three types of common XSS attacks
- Reflected XSS Non-persistent (reflected) XSS: Malicious JavaScript sent in the client request is echoed back in HTML code sent by the server and executed by the victim’s browser
- stored XSS Malicious JavaScript is stored in server-side content (for example, in a comment database) and executed every time a user’s browser loads it.
- DOM-based (client-side) XSS An indirect attack where the server’s HTTP response doesn’t include the actual malicious script. Instead, the browser is instructed to insert malicious code into its DOM structure and only then is the JavaScript executed.
SQL Injection (SQLi)
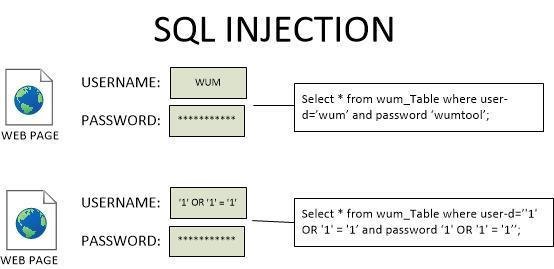
The second most common web application attacks are SQLi in which the attacker manipulates the database management SQL language queries that an application makes to its database. This attack might cause the attacker to view and edit or delete the data they are not normally able to retrieve. which can cause persistent changes to the application’s content.
There are three common SQLI
- In-band SQLi The term in-band means that the attacker receives the result as a direct response using the same communication channel. For example, if the attacker performs the attack manually using a web browser, the result of the attack will be displayed in the same web browser.
- Error based where the error output from the SQL database is used to manipulate the data inside the database. errors can be enough for the attacker to understand the database entirely
- Union-based Union based SQL injection allows an attacker to extract information from the database by extending the results returned by the original query. The Union operator can only be used if the original/new queries have the same structure (number and data type of columns)
- Blind SQLi
If the web app is vulnerable to SQLi. but does not contain relevant SQL query results or database errors in the HTTP response. in this case, the attacker can detect the SQLi by asking true or false questions or using time-based SQLi methods and by analyzing the response the attacker can identify the structure of the database.- Boolean-based By evaluating the results from various queries which return either true or false the attacker can confirm if the database is vulnerable to Blind SQLi
- Time-based Time-based techniques are often used to achieve tests when there is no other way to retrieve information from the database server. This kind of attack injects a SQL segment that contains a specific DBMS function or heavy query that generates a time delay. Depending on the time it takes to get the server response, it is possible to deduct some information.
- Out-of-band SQLi Out-of-band SQL injection occurs when an attacker is unable to use the same channel to launch the attack and gather results.Out-of-band SQLi techniques would rely on the database server’s ability to make DNS or HTTP requests to deliver data to an attacker. Such is the case with Microsoft SQL Server’s
xp_dirtreecommand, which can be used to make DNS requests to a server an attacker controls;
Path traversal.
Path traversal or directory traversal attack allows an attacker to access files, directories and commands that reside outside of the web root folder. The attacker use patterns like “../” to move up in the server directory hierarchy. which may allow attackers to obtain users’ credentials, configuration files, etc. Most of the times reason for this attack is inadequate input sanitization.
File Inclusion
File inclusion is a vulnerability that allows attackers to target poorly written web apps and the attack occurs when a web app allows users to include a file from within the server or from outside the server
Two File inclusion methods are
- Local file inclusion(LFI) LFI occurs when an application includes a file as user input without properly validating it. LFI can expose critical data or allow threat actors to launch attacks like remote code execution from within the server.
- Remote file inclusion(RFI) This allows an attacker to exploit the inclusion referencing function in a web app to upload arbitrary code like reverse shells from a remote URL hosted in a different domain.
Distributed Denial of Service (DDoS)
DDOS attacks affect the web application’s availability. Attack will attempt to make an online service unavailable by overwhelming it with traffic from multiple sources. by overwhelming a web app with fake traffic this fake network traffic will make the web app unavailable to legitimate users by exhausting the server resources. the attacks are launched from botnets which is a term used for a network of computers and other devices infected by malware that are under the control of the attacker. due to the nature of DDOS attacks, it is harder to track the attacker








Leave a Reply